Support for TLS 1.3 protocol
The NetScaler VPX and NetScaler MPX appliances now support the TLS 1.3 protocol, specified in RFC 8446.
Notes:
TLS 1.3 hardware acceleration is supported on the following platforms:
- MPX 5900
- MPX/SDX 8900
- MPX/SDX 9100
- MPX/SDX 9200
- MPX/SDX 15000
- MPX/SDX 15000-50G
- MPX/SDX 16000
- MPX/SDX 17000
- MPX/SDX 26000
- MPX/SDX 26000-50S
- MPX/SDX 26000-100G
Software-only support for the TLS 1.3 protocol is available on all other NetScaler MPX and SDX appliances except NetScaler FIPS appliances.
TLS 1.3 is only supported with the enhanced profile. To enable the enhanced profile, see Enable the default profile. The terms “default” and “enhanced” are used interchangeably for SSL profile.
To use TLS 1.3, you must use a client that conforms to the RFC 8446 specification.
Supported NetScaler features
The following SSL features are supported:
| SSL features | Support on the front end | Support on the back end |
|---|---|---|
| Cipher suite TLS 1.3-AES256-GCM-SHA384 (0x1302) | Yes | Yes |
| Cipher suite TLS 1.3_CHACHA20_POLY1305_SHA256 (0x1303) | Yes | Yes |
| Cipher suite TLS 1.3-AES128_GCM-SHA256 (0x1301) | Yes | Yes |
| ECC curve P_256 for ephemeral DH key exchange | Yes | Yes |
| ECC curve P_384 for ephemeral DH key exchange | Yes | Yes |
| ECC curve P_521 for ephemeral DH key exchange | Yes | Yes |
| Abbreviated handshakes when ticket-based session resumption is enabled | Yes | No |
| 0-RTT early application data | Yes | No |
| Replay attack protection for 0-RTT early application data | Yes | *NA |
| Optional or mandatory certificate-based client authentication, with support for OCSP and CRL validation of peer certificates | Yes | Yes |
| Server name extension: server certificate selection by using SNI | Yes | *NA |
| Application protocol negotiation (ALPN) by using the application_level_protocol_negotiation extension | Yes | Yes |
| OCSP stapling | Yes | *NA |
| Log messages and AppFlow records are produced for TLS 1.3 handshakes | Yes | Yes |
Optional logging of TLS 1.3 traffic secrets by the nstrace packet capture utility |
Yes | Yes |
| Interoperability with TLS peers implementing RFC 8446. For example, Mozilla Firefox, Google Chrome, and OpenSSL. | Yes | Yes |
*NA - not applicable
Configuration
TLS 1.3 is disabled by default on an SSL profile. Although you can enable TLS 1.3 on the legacy profile, some features, such as abbreviated handshakes when ticket-based session resumption is enabled and 0-RTT early application data are not supported on the legacy profile.
Add a front-end SSL profile by using the CLI
At the command prompt, type:
add ssl profile tls13profile -tls13 ENABLED
<!--NeedCopy-->
Example:
sh ssl profile tls13profile
1) Name: tls13profile (Front-End)
SSLv3: DISABLED TLSv1.0: ENABLED TLSv1.1: ENABLED TLSv1.2: ENABLED TLSv1.3: ENABLED
Client Auth: DISABLED
Use only bound CA certificates: DISABLED
Strict CA checks: NO
Session Reuse: ENABLED Timeout: 120 seconds
DH: DISABLED
DH Private-Key Exponent Size Limit: DISABLED Ephemeral RSA: ENABLED Refresh Count: 0
Deny SSL Renegotiation ALL
Non FIPS Ciphers: DISABLED
Cipher Redirect: DISABLED
SSL Redirect: DISABLED
Send Close-Notify: YES
Strict Sig-Digest Check: DISABLED
Zero RTT Early Data: DISABLED
DHE Key Exchange With PSK: NO
Tickets Per Authentication Context: 1
Push Encryption Trigger: Always
PUSH encryption trigger timeout: 1 ms
SNI: DISABLED
OCSP Stapling: DISABLED
Strict Host Header check for SNI enabled SSL sessions: NO
Push flag: 0x0 (Auto)
SSL quantum size: 8 kB
Encryption trigger timeout 100 mS
Encryption trigger packet count: 45
Subject/Issuer Name Insertion Format: Unicode
SSL Interception: DISABLED
SSL Interception OCSP Check: ENABLED
SSL Interception End to End Renegotiation: ENABLED
SSL Interception Maximum Reuse Sessions per Server: 10
Session Ticket: DISABLED
HSTS: DISABLED
HSTS IncludeSubDomains: NO
HSTS Max-Age: 0
ECC Curve: P_256, P_384, P_224, P_521
1) Cipher Name: DEFAULT Priority :1
Description: Predefined Cipher Alias
Done
<!--NeedCopy-->
Add a front-end SSL profile by using the GUI
- Navigate to System > Profiles. Select SSL Profiles.
- Click Add and specify a name for the profile.
-
In Protocol, select TLSv13.
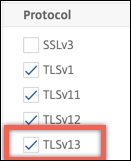
- Click OK and then click Done.
Add a back-end SSL profile by using the CLI
At the command prompt, type:
add ssl profile profile1 -sslprofileType BackEnd -tls13 ENABLED
<!--NeedCopy-->
Example:
add ssl profile tls13profile2 -sslprofileType BackEnd
sh ssl profile tls13profile2
1) Name: tls13profile2 (Back-End)
SSLv3: DISABLED TLSv1.0: ENABLED TLSv1.1: ENABLED TLSv1.2: ENABLED TLSv1.3: ENABLED
Server Auth: DISABLED
Use only bound CA certificates: DISABLED
Strict CA checks: NO
Session Reuse: ENABLED Timeout: 300 seconds
DH: DISABLED
Ephemeral RSA: DISABLED
Deny SSL Renegotiation ALL
Non FIPS Ciphers: DISABLED
Cipher Redirect: DISABLED
SSL Redirect: DISABLED
Send Close-Notify: YES
Strict Sig-Digest Check: DISABLED
Push Encryption Trigger: Always
PUSH encryption trigger timeout: 1 ms
SNI: DISABLED
OCSP Stapling: DISABLED
Strict Host Header check for SNI enabled SSL sessions: NO
Push flag: 0x0 (Auto)
SSL quantum size: 8 kB
Encryption trigger timeout 100 mS
Encryption trigger packet count: 45
Allow Extended Master Secret: NO
ECC Curve: P_256, P_384, P_224, P_521
1) Cipher Name: DEFAULT_BACKEND Priority :1
Description: Predefined Cipher Alias
Done
<!--NeedCopy-->
Add a back-end SSL profile by using the GUI
- Navigate to System > Profiles. Select SSL Profiles.
- Click Add and specify a name for the profile.
-
In SSL Profile Type, select BackEnd.
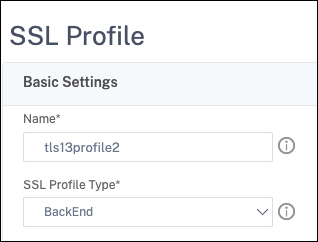
- In Protocol, select TLSv13.
- Click OK and then click Done.
Bind an SSL profile to an SSL virtual server by using the CLI
At the command prompt, type:
set ssl vserver <vserverName> -sslProfile <profile-name>
Example:
set ssl vserver ssl-vs -sslProfile tls13profile
Bind an SSL profile to an SSL virtual server by using the GUI
- Navigate to Traffic Management > Load Balancing > Virtual Servers, and select an SSL virtual server.
- Click Edit.
- In Advanced Settings, click SSL Profile.
- Select the TLS 1.3 profile created earlier.
- Click OK and then click Done.
Bind an SSL profile to an SSL service by using the CLI
At the command prompt, type:
set ssl service <serviceName> -sslProfile <profile-name>
Example:
set ssl service ssl-service -sslProfile tls13profile2
Note:
A warning appears if you bind a front-end profile to an SSL service.
Bind an SSL profile to an SSL service by using the GUI
- Navigate to Traffic Management > Load Balancing > Services, and select an SSL service.
- Click Edit.
- In Advanced Settings, click SSL Profile.
- Select the TLS 1.3 profile created earlier.
- Click OK and then click Done.
SSL profile parameters for TLS 1.3 protocol
Notes:
- Only tls13 applies to a back-end SSL profile.
- Starting from release 14.1 build 3.4, the debug logs for failed TLSv1.3 handshakes are recorded.
-
Enable or disable TLS 1.3 parameters in an SSL profile.
tls13: State of TLS 1.3 protocol support for the SSL profile.
Possible values: ENABLED, DISABLED
Default value: DISABLED
set ssl profile tls13profile -tls13 enable <!--NeedCopy-->set ssl profile tls13profile -tls13 disable <!--NeedCopy--> -
Set the number of session tickets issued.
tls13SessionTicketsPerAuthContext: Number of tickets the SSL virtual server issues when TLS 1.3 is negotiated, ticket-based resumption is enabled, and either (1) a handshake completes or (2) client authentication completes after the handshake.
This value can be increased to enable peers to open multiple parallel connections using a fresh ticket for each connection.
No tickets are sent if resumption is disabled.
Default value: 1
Minimum value: 1
Maximum value: 10
set ssl profile tls13profile -tls13sessionTicketsPerAuthContext 1 set ssl profile tls13profile -tls13sessionTicketsPerAuthContext 10 <!--NeedCopy--> -
Set DH key exchange.
dheKeyExchangeWithPsk: Specifies whether an SSL virtual server requires a DHE key exchange to occur when a preshared key is accepted during a TLS 1.3 session resumption handshake. A DHE key exchange ensures forward secrecy, even if ticket keys are compromised, at the expense of extra resources required to carry out the DHE key exchange.Available settings work as follows, if the session ticket is enabled:
YES: DHE key exchange is required when a pre-shared key is accepted, regardless of whether the client supports the key exchange. The handshake is aborted with a fatal alert, if the client does not support DHE key exchange when offering a pre-shared key.
NO: DHE key exchange is performed when a pre-shared key is accepted, only if requested by the client.
Possible values: YES, NO
Default value: NO
set ssl profile tls13profile dheKeyExchangeWithPsk yes set ssl profile tls13profile dheKeyExchangeWithPsk no <!--NeedCopy--> -
Enable or disable 0-RTT early data acceptance.
zeroRttEarlyData: State of TLS 1.3 early application data. Applicable settings work as follows:ENABLED: Early application data might be processed before the handshake is complete.
DISABLED: Early application data is ignored.
Possible values: ENABLED, DISABLED
Default value: DISABLED
set ssl profile tls13profile -zeroRttEarlyData ENABLED set ssl profile tls13profile -zeroRttEarlyData DISABLED <!--NeedCopy-->
Default cipher group
The default cipher group includes TLS 1.3 ciphers.
sh cipher DEFAULT
1) Cipher Name: TLS1-AES-256-CBC-SHA Priority : 1
Description: SSLv3 Kx=RSA Au=RSA Enc=AES(256) Mac=SHA1 HexCode=0x0035
2) Cipher Name: TLS1-AES-128-CBC-SHA Priority : 2
Description: SSLv3 Kx=RSA Au=RSA Enc=AES(128) Mac=SHA1 HexCode=0x002f
…
…
27) Cipher Name: TLS 1.3-AES256-GCM-SHA384 Priority : 27
Description: TLS 1.3 Kx=any Au=any Enc=AES-GCM(256) Mac=AEAD HexCode=0x1302
28) Cipher Name: TLS 1.3_CHACHA20_POLY1305_SHA256 Priority : 28
Description: TLS 1.3 Kx=any Au=any Enc=CHACHA20/POLY1305(256) Mac=AEAD HexCode=0x1303
29) Cipher Name: TLS 1.3-AES128_GCM-SHA256 Priority : 29
Description: TLS 1.3 Kx=any Au=any Enc=AES-GCM(128) Mac=AEAD HexCode=0x1301
Done
<!--NeedCopy-->
sh cipher DEFAULT_BACKEND
1) Cipher Name: TLS1-AES-256-CBC-SHA Priority : 1
Description: SSLv3 Kx=RSA Au=RSA Enc=AES(256) Mac=SHA1 HexCode=0x0035
2) Cipher Name: TLS1-AES-128-CBC-SHA Priority : 2
Description: SSLv3 Kx=RSA Au=RSA Enc=AES(128) Mac=SHA1 HexCode=0x002f
...
...
27) Cipher Name: TLS 1.3-AES256-GCM-SHA384 Priority : 27
Description: TLS 1.3 Kx=any Au=any Enc=AES-GCM(256) Mac=AEAD HexCode=0x1302
28) Cipher Name: TLS 1.3-CHACHA20-POLY1305-SHA256 Priority : 28
Description: TLS 1.3 Kx=any Au=any Enc=CHACHA20/POLY1305(256) Mac=AEAD HexCode=0x1303
29) Cipher Name: TLS 1.3-AES128-GCM-SHA256 Priority : 29
Description: TLS 1.3 Kx=any Au=any Enc=AES-GCM(128) Mac=AEAD HexCode=0x1301
Done
<!--NeedCopy-->
Limitations
- TLS 1.3 is not supported on a NetScaler FIPS appliance.
- Only RSA certificates with 1024-bit and larger keys are supported in a TLS 1.3 handshake.
- Prior to release 14.1 build 3.4, TLSv1.3 handshake logs are not captured even if the debug level was set.
Security restrictions
TLS 1.3 server operators must keep in mind the following security restrictions for backward compatibility outlined in RFC 8446. The default configuration on a NetScaler appliance is compliant with these restrictions. However, a NetScaler appliance does not enforce these rules.
-
The security of RC4 cipher suites is considered insufficient as described in RFC7465. Implementations must not offer or negotiate RC4 cipher suites for any version of TLS.
-
Old versions of TLS allowed the use of low strength ciphers. Ciphers with a strength less than 112 bits must not be offered or negotiated for any version of TLS.
-
The security of SSL 3.0 [SSLv3] is considered insufficient as described in RFC7568, and must not be negotiated. Disable SSLv3 when TLS 1.3 is enabled (SSLv3 is disabled by default).
Note:
For information about troubleshooting protocols that run over TLS 1.3, see Decrypting TLS 1.3 traffic from packet trace.