Configure GSLB on an active-standby high-availability setup
You can configure global server load balancing (GSLB) on active-standby HA deployment on Azure in three steps:
-
Create a VPX HA pair on each GSLB site. See Configure a high-availability setup with multiple IP addresses and NICs for information about how to create an HA pair.
-
Configure the Azure Load Balancer (ALB) with the front-end IP address and rules to allow GSLB and DNS traffic.
This step involves the following substeps. See the scenario in this section for the PowerShell commands used to complete these substeps.
a. Create a front-end
IPconfigfor GSLB site.b. Create a back-end address pool with IP address of NIC 1/1 of nodes in HA.
c. Create load-balancing rules for following:
TCP/3009 – gslb communication TCP/3008 - gslb communication UDP/53 - DNS communicationd. Associate back-end address pool with the LB rules created in step c.
e. Update the network security group of NIC 1/1 of nodes in both the HA pair to allow the traffic for TCP 3008, TCP 3009 and UDP 53 ports.
-
Enable GSLB on each HA pair.
Scenario
This scenario includes two sites - Site 1 and Site 2. Each site has an HA pair (HA1 and HA2) configured with multiple NICs, multiple IP addresses, and GSLB.
Figure: GLSB on Active-Standy HA Deployment on Azure
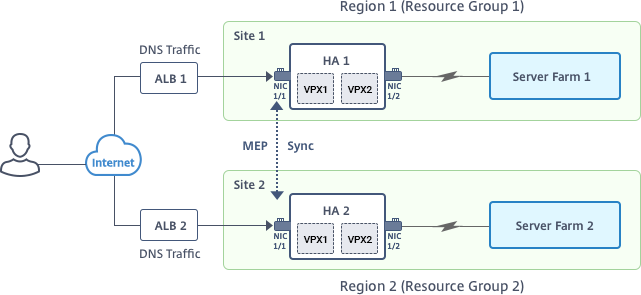
In this scenario, each VM has three NICs - NIC 0/1, 1/1, and 1/2. The NICs are configured for the following purposes.
NIC 0/1: to serve management traffic
NIC 1/1: to serve client-side traffic
NIC 1/2: to communicate with back-end servers
Parameter Settings
Following are sample parameters settings for the ALB. You can use different settings if you want.
$locName="South east Asia"
$rgName="MulitIP-MultiNIC-RG"
$pubIPName4="PIPFORGSLB1"
$domName4="vpxgslbdns"
$lbName="MultiIPALB"
$frontEndConfigName2="FrontEndIP2"
$backendPoolName1="BackendPoolHttp"
$lbRuleName2="LBRuleGSLB1"
$lbRuleName3="LBRuleGSLB2"
$lbRuleName4="LBRuleDNS"
$healthProbeName="HealthProbe"
Configure ALB with the front-end IP address and rules to allow GSLB and DNS traffic
Step 1. Create a public IP for GSLB site IP
$pip4=New-AzureRmPublicIpAddress -Name $pubIPName4 -ResourceGroupName $rgName -DomainNameLabel $domName4 -Location $locName -AllocationMethod Dynamic
Get-AzureRmLoadBalancer -Name \$lbName -ResourceGroupName \$rgName | Add-AzureRmLoadBalancerFrontendIpConfig -Name \$frontEndConfigName2 -PublicIpAddress \$pip4 | Set-AzureRmLoadBalancer
Step 2. Create LB rules and update the existing ALB.
$alb = get-AzureRmLoadBalancer -Name $lbName -ResourceGroupName $rgName
$frontendipconfig2=Get-AzureRmLoadBalancerFrontendIpConfig -LoadBalancer $alb -Name $frontEndConfigName2
$backendPool=Get-AzureRmLoadBalancerBackendAddressPoolConfig -LoadBalancer $alb -Name $backendPoolName1
$healthprobe=Get-AzureRmLoadBalancerProbeConfig -LoadBalancer $alb -Name $healthProbeName
\$alb | Add-AzureRmLoadBalancerRuleConfig -Name \$lbRuleName2 -BackendAddressPool \$backendPool -FrontendIPConfiguration \$frontendipconfig2 -Protocol \"Tcp\" -FrontendPort 3009 -BackendPort 3009 -Probe \$healthprobe -EnableFloatingIP | Set-AzureRmLoadBalancer
\$alb | Add-AzureRmLoadBalancerRuleConfig -Name \$lbRuleName3 -BackendAddressPool \$backendPool -FrontendIPConfiguration \$frontendipconfig2 -Protocol \"Tcp\" -FrontendPort 3008 -BackendPort 3008 -Probe \$healthprobe -EnableFloatingIP | Set-AzureRmLoadBalancer
\$alb | Add-AzureRmLoadBalancerRuleConfig -Name \$lbRuleName4 -BackendAddressPool \$backendPool -FrontendIPConfiguration \$frontendipconfig2 -Protocol \"Udp\" -FrontendPort 53 -BackendPort 53 -Probe \$healthprobe -EnableFloatingIP | Set-AzureRmLoadBalancer
Enable GSLB on each high availability pair
Now you’ve two front-end IP addresses for each ALB: ALB 1 and ALB 2. One IP address is for the LB virtual server and the other for the GSLB site IP.
HA 1 has the following front-end IP addresses:
- FrontEndIPofALB1 (for LB virtual server)
- PIPFORGSLB1 (GSLB IP)
HA 2 has the following front-end IP addresses:
- FrontEndIPofALB2 (for LB virtual server)
- PIPFORGSLB2 (GSLB IP)
The following commands are used for this scenario.
enable ns feature LB GSLB
add service dnssvc PIPFORGSLB1 ADNS 53
add gslb site site1 PIPFORGSLB1 -publicIP PIPFORGSLB1
add gslb site site2 PIPFORGSLB2 -publicIP PIPFORGSLB2
add gslb service site1_gslb_http_svc1 FrontEndIPofALB1 HTTP 80 -publicIP FrontEndIPofALB1 -publicPort 80 -siteName site1
add gslb service site2_gslb_http_svc1 FrontEndIPofALB2 HTTP 80 -publicIP FrontEndIPofALB2 -publicPort 80 -siteName site2
add gslb vserver gslb_http_vip1 HTTP
bind gslb vserver gslb_http_vip1 -serviceName site2_gslb_http_svc1
bind gslb vserver gslb_http_vip1 -serviceName site1_gslb_http_svc1
bind gslb vserver gslb_http_vip1 -domainName www.gslbindia.com -TTL 5
Related resources: