Configure HA-INC nodes by using the NetScaler® high availability template for internet-facing applications
You can quickly and efficiently deploy a pair of VPX instances in HA-INC mode by using the standard template for internet-facing applications. The Azure load balancer (ALB) uses a public IP address for the front end. The template creates two nodes, with three subnets and six NICs. The subnets are for management, client, and server-side traffic. Each subnet has two NICs for both the VPX instances.
You can get the NetScaler HA pair template for internet-facing applications at the Azure Marketplace.
Complete the following steps to launch the template and deploy a high availability VPX pair by using Azure availability sets or availability zone.
- From the Azure Marketplace, search NetScaler.
-
Click GET IT NOW.
-
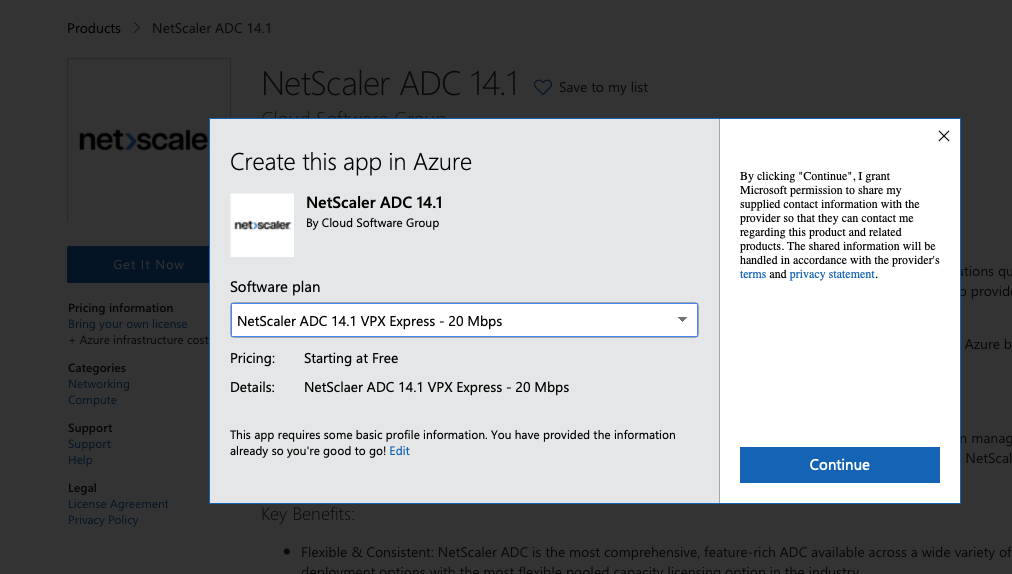
Select the required HA deployment along with license, and click Continue.
-
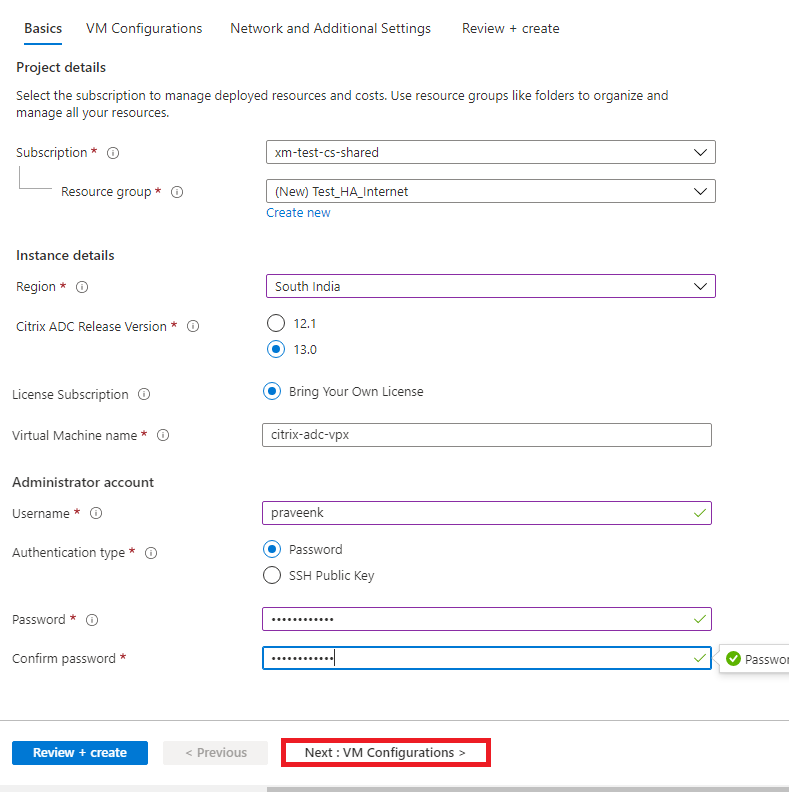
The Basics page appears. Create a Resource Group. Under the Parameters tab, enter details for the Region, Admin user name, Admin Password, license type (VM SKU), and other fields.
-
Click Next : VM Configurations >.
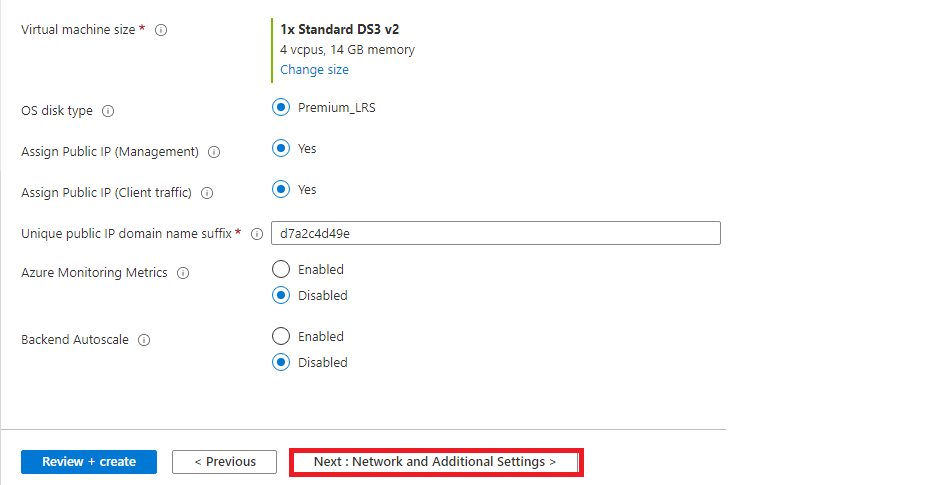
- On the VM Configurations page, perform the following:
- Configure public IP domain name suffix
- Enable or disable Azure Monitoring Metrics
- Enable or disable Backend Autoscale™
-
Click Next: Network and Additional settings >
-
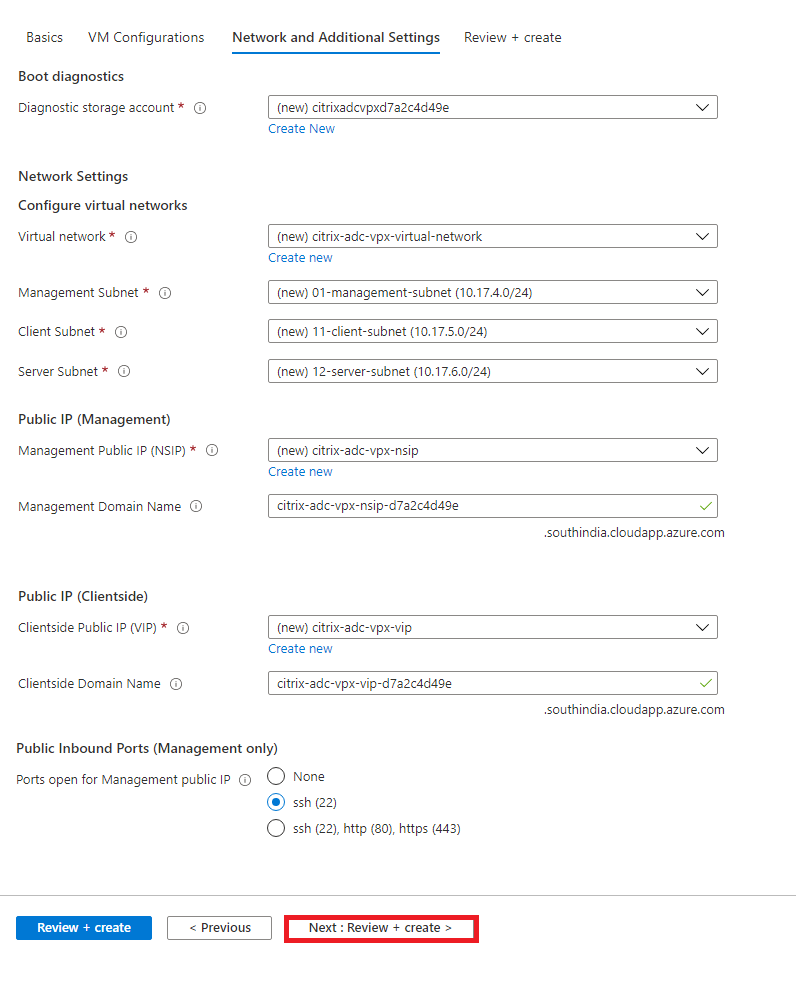
On Network and Additional Settings page, create Boot diagnostics account and configure the network settings.
-
Click Next: Review + create >.
-
Review the basic settings, VM configuration, network and additional settings, and click Create.
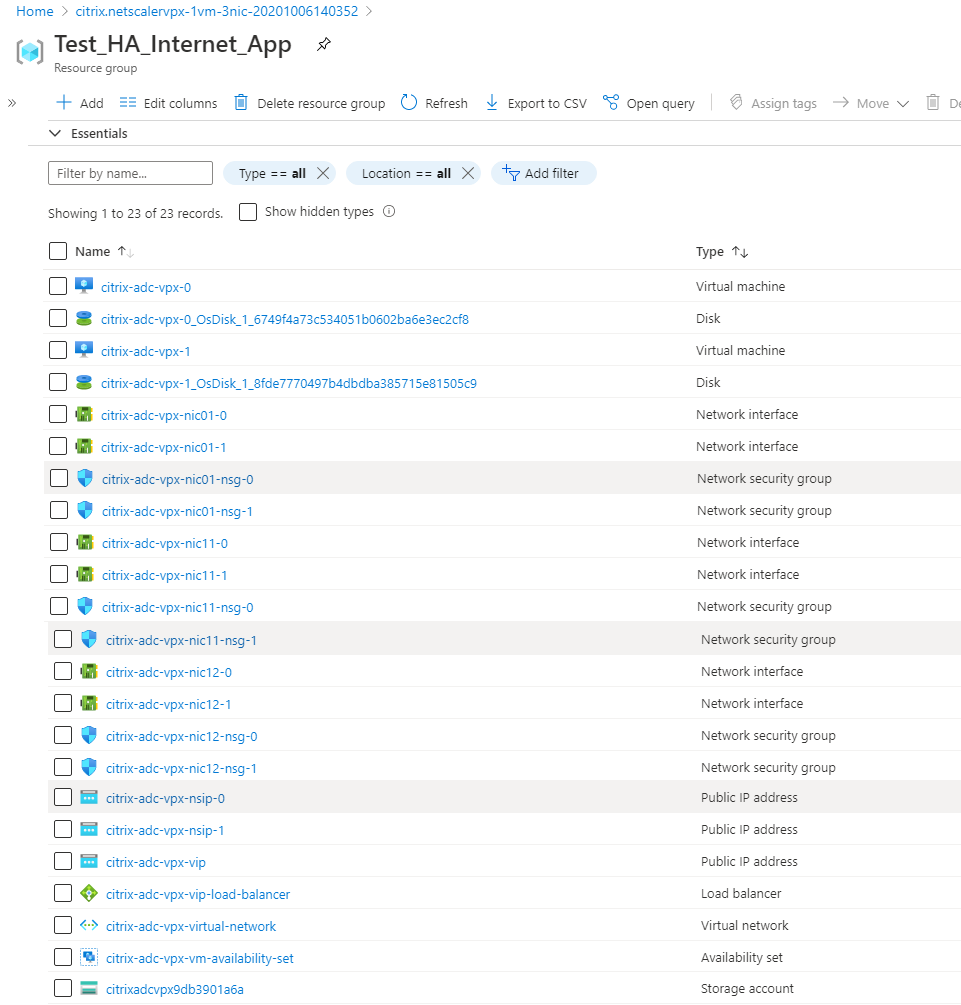
It might take a moment for the Azure Resource Group to be created with the required configurations. After completion, select the Resource Group in the Azure portal to see the configuration details, such as LB rules, back-end pools, and health probes. The high availability pair appears as citrix-adc-vpx-0 and citrix-adc-vpx-1.
If further modifications are required for your HA setup, such as creating more security rules and ports, you can do that from the Azure portal.
Once the required configuration is complete, the following resources are created.
-
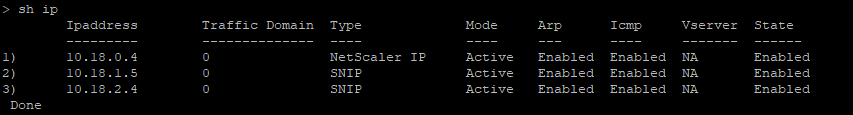
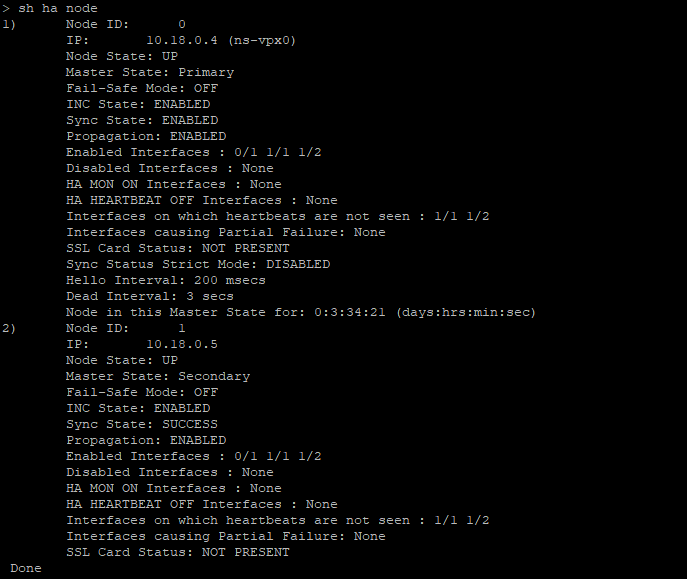
You must log on to citrix-adc-vpx-0 and citrix-adc-vpx-1 nodes to validate the following configuration:
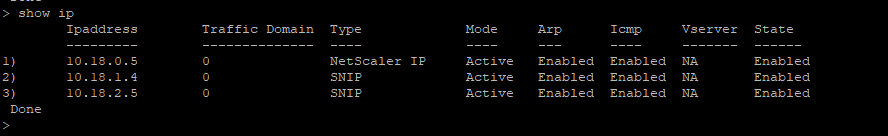
- NSIP addresses for both nodes must be in the management subnet.
- On the primary (citrix-adc-vpx-0) and secondary (citrix-adc-vpx-1) nodes, you must see two SNIP addresses. One SNIP (client subnet) is used for responding to the ALB probes and the other SNIP (server subnet) is used for back-end server communication.
Note:
In the HA-INC mode, the SNIP addresses of the citrix-adc-vpx-0 and citrix-adc-vpx-1 VMs are different, unlike with the classic on-premises ADC high availability deployment where both are the same.
On the primary node (citrix-adc-vpx-0)
On the secondary node (citrix-adc-vpx-1)
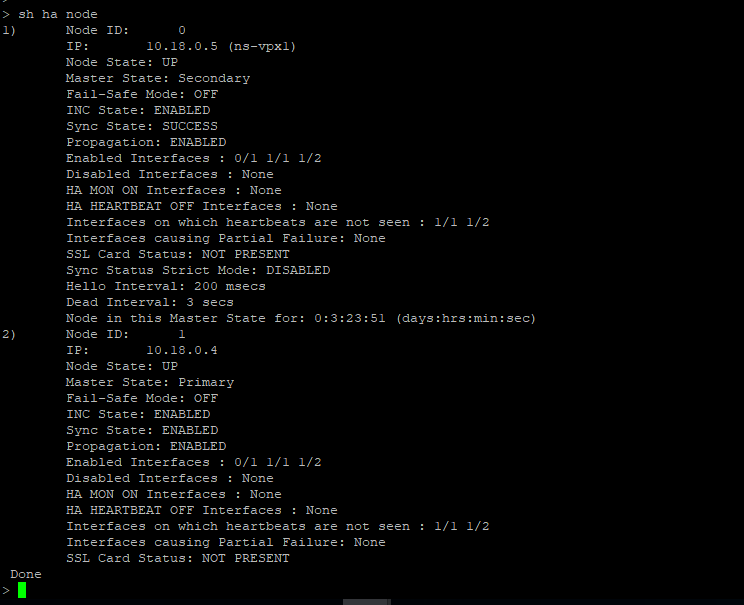
-
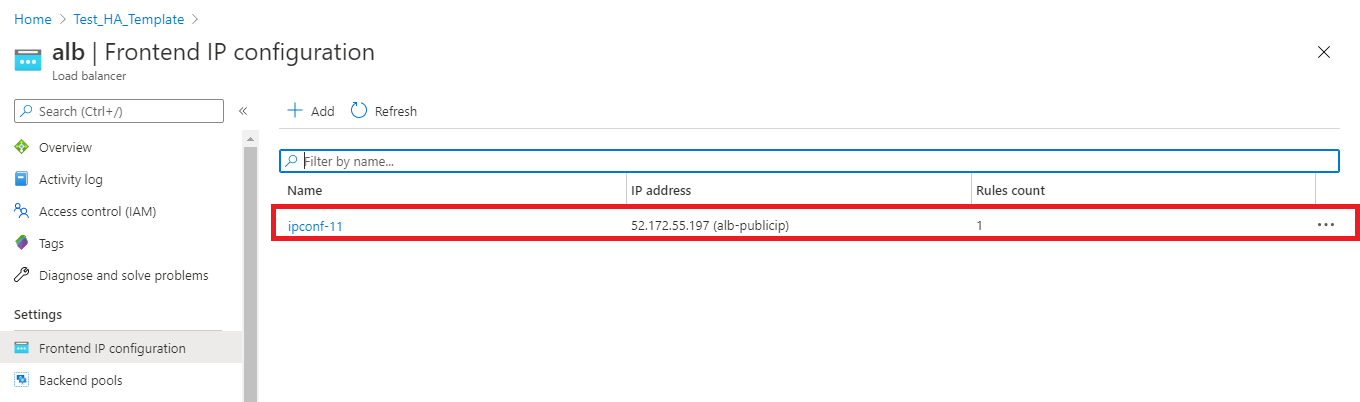
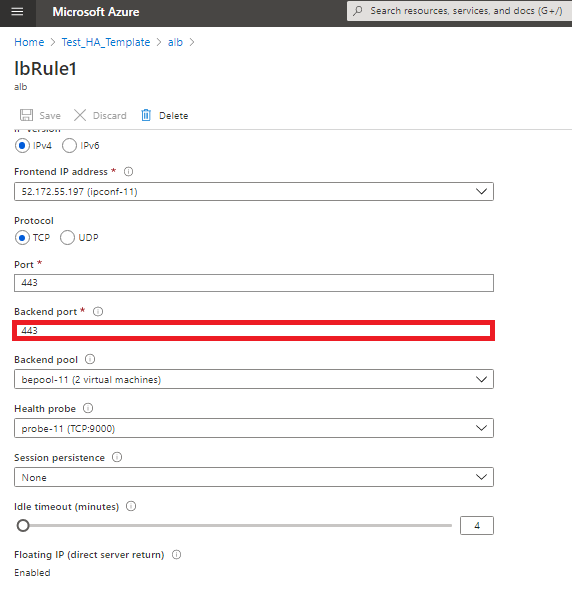
After the primary and secondary nodes are UP and the Synchronization status is SUCCESS, you must configure the load balancing virtual server or the gateway virtual server on the primary node (citrix-adc-vpx-0) with the public IP address of the ALB virtual server. For more information, see the Sample configuration section.
-
To find the public IP address of ALB virtual server, navigate to Azure portal > Azure Load Balancer > Frontend IP configuration.
-
Add the inbound security rule for virtual server port 443 on the network security group of both the client interfaces.
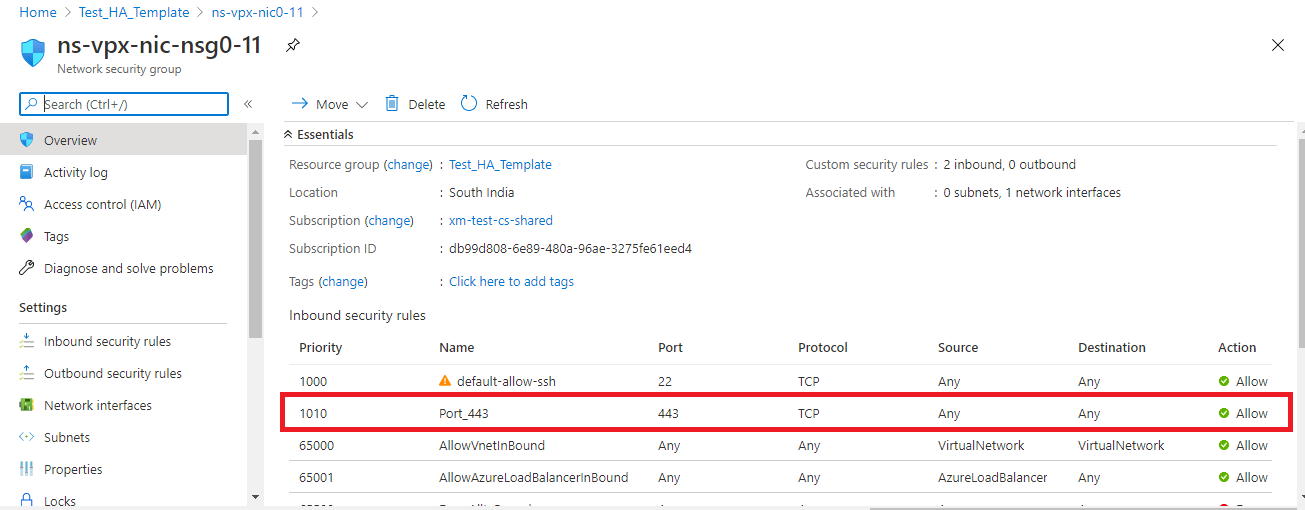
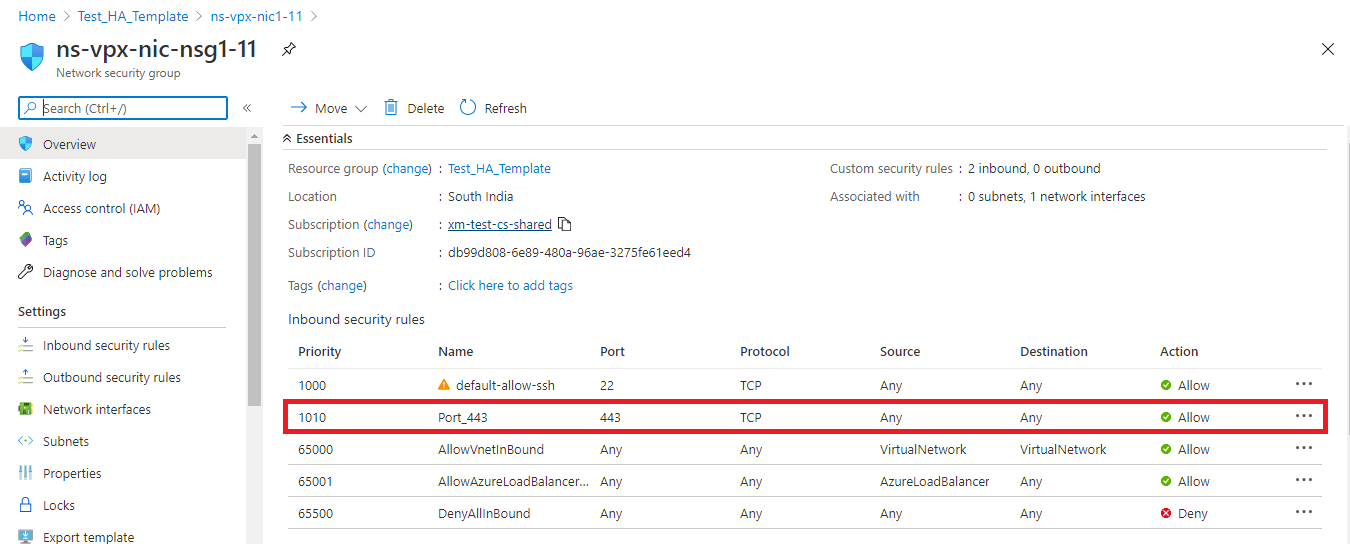
-
Configure the ALB port that you want to access, and create inbound security rule for the specified port. The Backend port is your load balancing virtual server port or the VPN virtual server port.
-
Now, you can access the load balancing virtual server or the VPN virtual server using the fully qualified domain name (FQDN) associated with the ALB public IP address.
Sample configuration
To configure a gateway VPN virtual server and load balancing virtual server, run the following commands on the primary node (ADC-VPX-0). The configuration auto synchronizes to the secondary node (ADC-VPX-1).
Gateway sample configuration
enable feature aaa LB SSL SSLVPN
add ip 52.172.55.197 255.255.255.0 -type VIP
add vpn vserver vpn_ssl SSL 52.172.55.197 443
add ssl certKey ckp -cert cgwsanity.cer -key cgwsanity.key
bind ssl vserver vpn_ssl -certkeyName ckp
<!--NeedCopy-->
Load balancing sample configuration
enable feature LB SSL
enable ns mode MBF
add lb vserver lb_vs1 SSL 52.172.55.197 443
bind ssl vserver lb_vs1 -certkeyName ckp
<!--NeedCopy-->
You can now access the load balancing or VPN virtual server using the FQDN associated with the public IP address of ALB.
See the Resources section for more information about how to configure the load balancing virtual server.
Resources:
The following links provide additional information related to HA deployment and virtual server configuration: