Protect AWS API Gateway using the NetScaler Web App Firewall
You can deploy a NetScaler appliance in front of your AWS API Gateway and secure the API gateway from external threats. NetScaler Web App Firewall (WAF) can defend your API against OWASP top 10 threats and zero-day attacks. NetScaler Web App Firewall uses a single code base across all ADC form factors. Hence, you can consistently apply and enforce security policies across any environment. NetScaler Web App Firewall is easy to deploy and is available as a single license. The NetScaler Web App Firewall provides you the following features:
- Simplified configuration
- Bot management
- Holistic visibility
- Collate data from multiple sources and display the data in a unified screen
In addition to API gateway protection, you can also use the other NetScaler features. For more information, see NetScaler documentation. Besides to avoid data center failovers and minimizing shutdown time, you can place ADC in high availability within or across availability zones. You can also use or configure clustering with Autoscale feature.
Earlier, AWS API Gateway did not support the protections needed to secure the applications behind it. Without the Web Application Firewall (WAF) protections, APIs were prone to security threats.
Deploy NetScaler appliance in front of AWS API gateway
In the following example, a NetScaler appliance is deployed in front of the AWS API gateway.
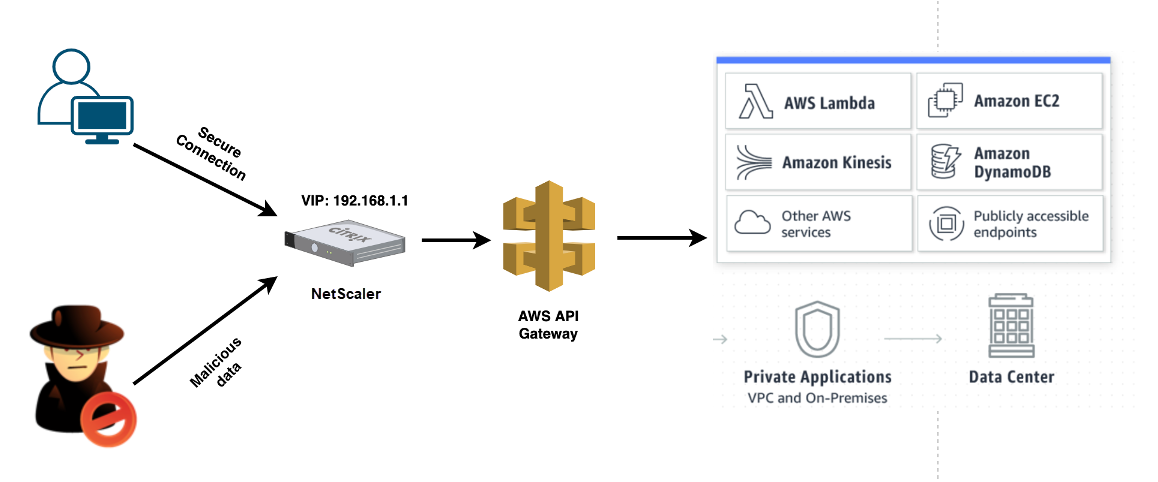
Let’s assume there’s a genuine API request for AWS Lambda service. This request can be for any of the API services as mentioned in Amazon API Gateway documentation. As shown in the preceding diagram, the traffic flow is as follows:
- Client sends a request to the AWS Lambda Function (XYZ). This client request is sent to the NetScaler virtual server (192.168.1.1).
- The virtual server inspects the packet and checks for any malicious content.
- The NetScaler appliance triggers a Rewrite policy to change the host name and URL in a client request. For example, you want to change
https://restapi.citrix.com/default/LamdaFunctionXYZtohttps://citrix.execute-api.<region>.amazonaws.com/default/LambdaFunctionXYZ. - The NetScaler appliance forwards this request to the AWS API gateway.
- The AWS API Gateway further sends the request to the Lambda service and calls the Lambda function “XYZ”.
- At the same time, if an attacker sends an API request with malicious content, the malicious request lands on the NetScaler appliance.
- The NetScaler appliance inspects the packets and drops the packets based on the configured action.
Configure NetScaler appliance with WAF enabled
To enable WAF on a NetScaler appliance, do the following steps:
- Add a content switching or a load balancing virtual server. Let’s say the IP address of the virtual server is 192.168.1.1, which resolves to a domain name (restapi.citrix.com).
- Enable WAF policy on NetScaler virtual server. For more information, see Configuring the Web App Firewall.
- Enable Rewrite policy to change the domain name. Let’s say, you want to change the incoming request to load balancer at “restapi.citrix.com” domain name to be rewritten to the back-end AWS API Gateway at “citrix.execute-api.
<region>.amazonaws” domain name. -
Enable L3 mode on the NetScaler appliance to make it act as a proxy. Use the following command:
enable ns mode L3 <!--NeedCopy-->
In Step 3 of the preceding example, let’s say the website administrator wants the NetScaler appliance to replace the “restapi.citrix.com” domain name with “citrix.execute-api.<region>.amazonaws.com” and the URL with “default/lambda/XYZ”.
The following procedure describes how to change the host name and URL in a client request using rewrite feature:
- Log on to the NetScaler appliance using SSH.
-
Add rewrite actions.
add rewrite action rewrite_host_hdr_act replace "HTTP.REQ.HEADER(\"Host\")" "\"citrix.execute-api.<region>.amazonaws.com\"" add rewrite action rewrite_url_act replace HTTP.REQ.URL.PATH_AND_QUERY "\"/default/lambda/XYZ\"" <!--NeedCopy--> -
Add rewrite policies for the rewrite actions.
add rewrite policy rewrite_host_hdr_pol "HTTP.REQ.HEADER(\"Host\").CONTAINS(\"restapi.citrix.com\") "rewrite_host_hdr_act add rewrite policy rewrite_url_pol "HTTP.REQ.HEADER(\"Host\").CONTAINS(\"restapi.citrix.com\") "rewrite_url_act <!--NeedCopy--> -
Bind the rewrite policies to a virtual server.
bind lb vserver LB_API_Gateway -policyName rewrite_host_hdr_pol -priority 10 -gotoPriorityExpression 20 -type REQUEST bind lb vserver LB_API_Gateway -policyName rewrite_url_pol -priority 20 -gotoPriorityExpression END -type REQUEST <!--NeedCopy-->
For more information, see Configure rewrite to change the host name and URL in client request on NetScaler appliance.
NetScaler features and capabilities
The NetScaler appliance besides securing the deployment can also enhance the request based on the user requirement. The NetScaler appliance provides the following key features.
-
Load balance the API gateway: If you have more than one API gateway, you can load balance multiple API gateways using the NetScaler appliance and define the behavior of the API request.
-
Different load balancing methods are available. For example, the Least connection method avoids overloading of API Gateway limit, the Custom load method maintains a specific load on a particular API gateway, and so on. For more information, see Load balancing algorithms.
- SSL offloading is configured without interrupting the traffic.
- Use Source IP (USIP) mode is enabled to preserve the client IP address.
- User-defined SSL settings: You can have your own SSL virtual server with your own-signed certificates and algorithms.
- Backup virtual server: If the API gateway is not reachable, you can send the request to a backup virtual server for further actions.
- Many other load balancing features are available. For more information, see Load balance traffic on a NetScaler appliance.
-
-
Authentication, Authorization and Auditing: You can define your own authentication methods like LDAP, SAML, RADIUS, and authorize and audit the API requests.
-
Responder: You can redirect API requests to some other API Gateway during the shutdown time.
-
Rate limiting: You can configure the rate limiting feature to avoid overloading of an API gateway.
-
Better Availablity: You can configure a NetScaler appliance in a high availability setup or a cluster setup to give better availability to your AWS API traffics.
-
REST API: Supports the REST API, which can be used for automating the work in cloud production environments.
-
Monitor data: Monitors and logs the data for reference.
The NetScaler appliance provides a lot more features, which can be integrated with the AWS API gateway. For more information, see NetScaler documentation.