Install a NetScaler VPX instance on Google Cloud VMware Engine
Google Cloud VMware Engine (GCVE) provides you with private clouds that contain vSphere clusters, built from dedicated bare-metal Google Cloud Platform infrastructure. The minimum initial deployment is three hosts, but additional hosts can be added one at a time. All provisioned private clouds have vCenter Server, vSAN, vSphere, and NSX-T.
GCVE enables you to create cloud software-defined data centers (SDDC) on Google Cloud Platform with the desired number of ESX hosts. GCVE supports NetScaler VPX deployments. GCVE provides a user interface same as on-prem vCenter. It functions identical to the ESX-based NetScaler VPX deployments.
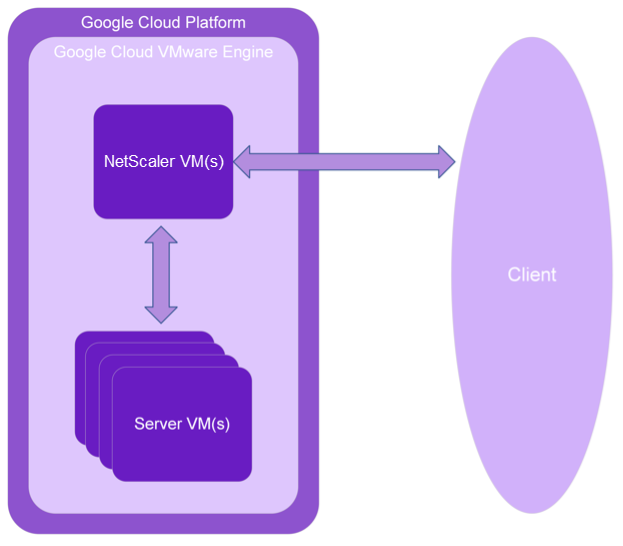
The following diagram shows the GCVE on the Google Cloud Platform that an administrator or a client can access over the internet. An administrator can create, manage, and configure workload or server VMs using GCVE. The admin can access the GCVE’s web-based vCenter and NSX-T Manager using an OpenVPN connection. You can create the NetScaler VPX instances (standalone or HA pair) and server VMs within GCVE using vCenter, and manage the corresponding networking using NSX-T manager. The NetScaler VPX instance on GCVE works similar to the On-prem VMware cluster of hosts. GCVE can be managed using OpenVPN connection to the management infrastructure.
Prerequisites
Before you begin installing a virtual appliance, do the following:
- For more information on Google Cloud VMware Engine and its prerequisites, see Google Cloud VMware Engine documentation.
- For more information on deploying Google Cloud VMware Engine, see Deploy a Google Cloud VMware Engine private cloud.
- For more information on connecting to your private cloud using a point-to-site VPN gateway to access and manage Google Cloud VMware Engine, see Access an Google Cloud VMware Engine private cloud.
- On VPN client machine, download the NetScaler VPX appliance setup files.
- Create appropriate NSX-T network segments on VMware SDDC to which the virtual machines connect. For more information, see Add a network segment in Google Cloud VMware Engine.
- Obtain VPX license files. For more information about NetScaler VPX instance licenses, see Licensing overview.
- Virtual machines (VMs) created or migrated to the GCVE private cloud must be attached to a network segment.
VMware cloud hardware requirements
The following table lists the virtual computing resources that the VMware SDDC must provide for each VPX nCore virtual appliance.
Table 1. Minimum virtual computing resources required for running a NetScaler VPX instance
| Component | Requirement |
|---|---|
| Memory | 2 GB |
| Virtual CPU (vCPU) | 2 |
| Virtual network interfaces | In VMware SDDC, you can install a maximum of 10 virtual network interfaces if the VPX hardware is upgraded to version 7 or higher. |
| Disk space | 20 GB |
Note:
This is in addition to any disk requirements for the hypervisor.
For production use of the VPX virtual appliance, the full memory allocation must be reserved.
OVF Tool 1.0 system requirements
OVF Tool is a client application that can run on Windows and Linux systems. The following table describes the minimum system requirements for installing OVF tool.
Table 2. Minimum system requirements for OVF tool installation
| Component | Requirement |
|---|---|
| Operating system | For detailed requirements from VMware, search for the “OVF Tool User Guide” PDF file at http://kb.vmware.com/. |
| CPU | 750 MHz minimum, 1 GHz or faster recommended |
| RAM | 1 GB Minimum, 2 GB recommended |
| NIC | 100 Mbps or faster NIC |
For information about installing OVF, search for the “OVF Tool User Guide” PDF file at http://kb.vmware.com/.
Downloading the NetScaler VPX setup files
The NetScaler VPX instance setup package for VMware ESX follows the Open Virtual Machine (OVF) format standard. You can download the files from the Citrix website. You need a Citrix account to log on. If you do not have a Citrix account, access the home page at http://www.citrix.com. Click the New Users link, and follow the instructions to create a new Citrix account.
Once logged on, navigate the following path from the Citrix® home page:
Citrix.com > Downloads > NetScaler > Virtual Appliances.
Copy the following files to a workstation on the same network as the ESX server. Copy all three files into the same folder.
- NSVPX-ESX-<release number>-<build number>-disk1.vmdk (for example, NSVPX-ESX-13.0-79.64-disk1.vmdk)
- NSVPX-ESX-<release number>-<build number>.ovf (for example, NSVPX-ESX-13.0-79.64.ovf)
- NSVPX-ESX-<release number>-<build number>.mf (for example, NSVPX-ESX-13.0-79.64.mf)
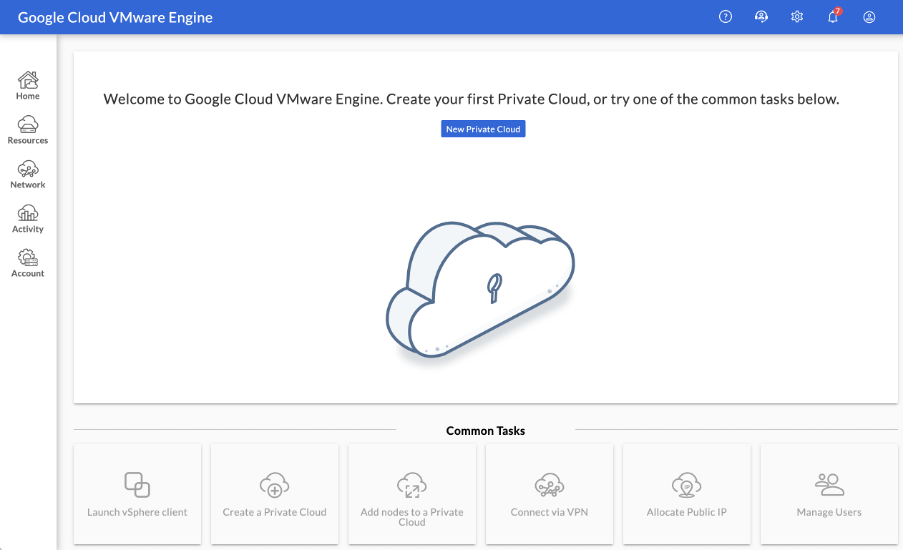
Deploy Google Cloud VMware Engine
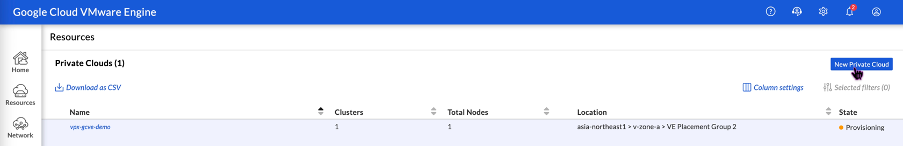
-
Log in to your GCVE portal, and navigate to Home.
-
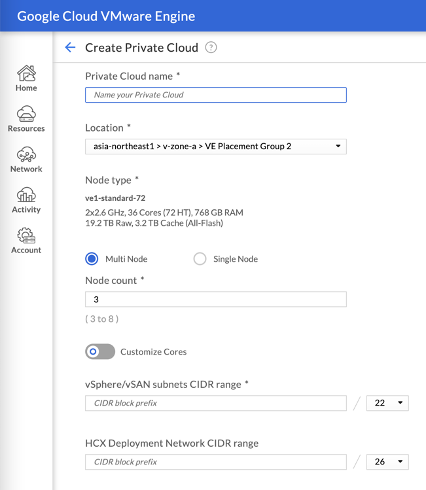
In the New Private Cloud page, enter the following details:
- Select a minimum of 3 ESXi hosts to create the default cluster of your private cloud.
- For the vSphere/vSan subnet CIDR range field, use /22 address space.
- For the HCX Deployment Network CIDR range field, use /26 address space.
- For the virtual network, make sure that the CIDR range doesn’t overlap with any of your on-premises or other GCP subnets (virtual networks).
-
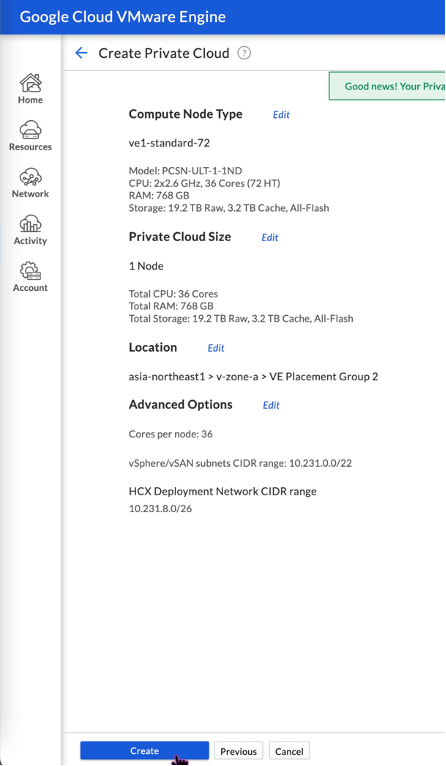
Click Review and Create.
-
Review the settings. If you need to change any settings, click Previous.
-
Click Create. Private Cloud provisioning process starts. It can take up to two hours for the Private Cloud to be provisioned.
-
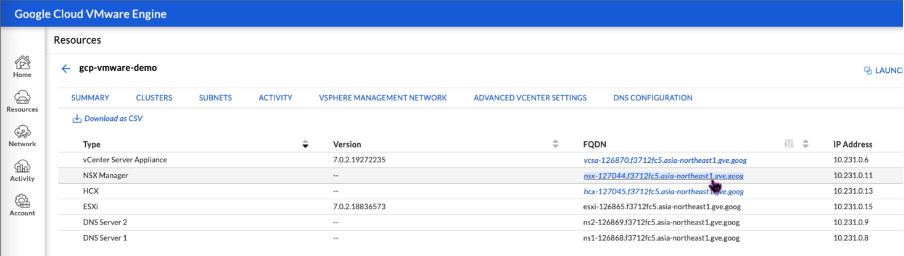
Go to Resources to verify the private cloud that is created.
-
To access this resource, you must connect to GCVE using point-to-site VPN. For more information, see the following documentation:
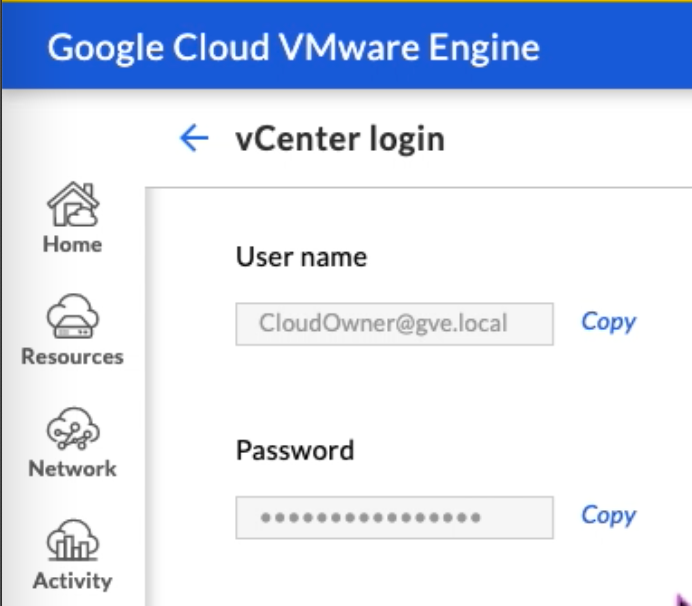
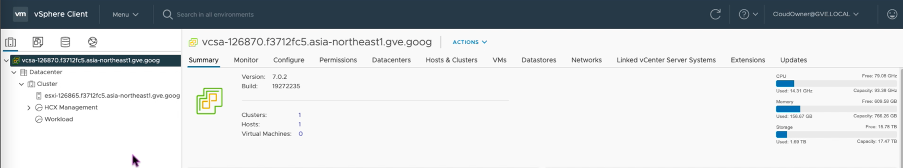
Access your Private Cloud vCenter portal
-
Navigate to your Google Cloud VMware Engine private cloud. In the SUMMARY tab, under vCenter Login Info, click View.
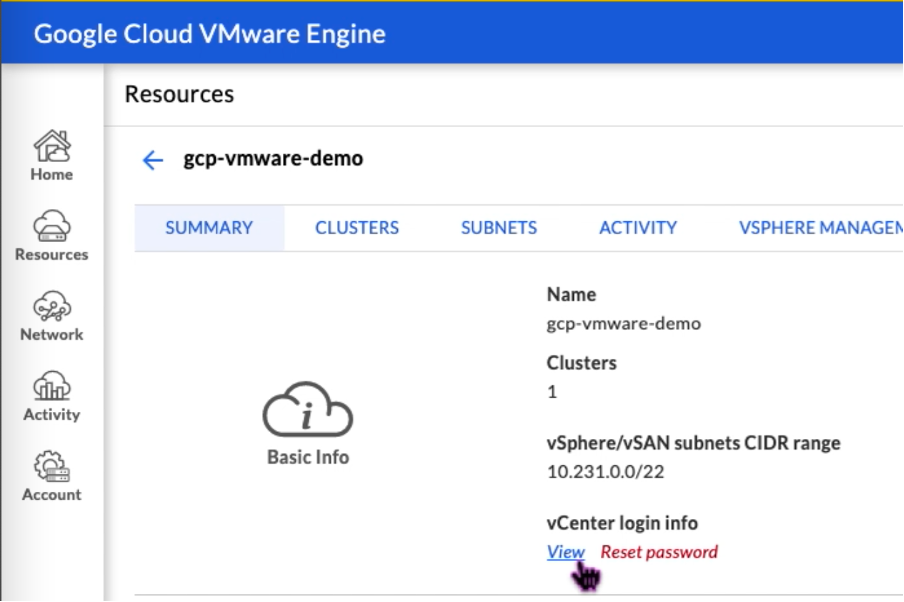
-
Make note of the vCenter credentials.
-
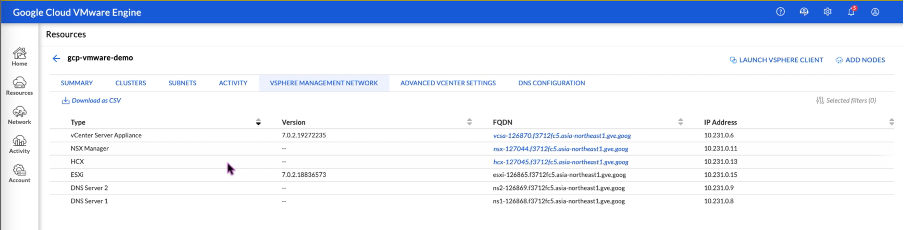
Launch the vSphere client by clicking LAUNCH VSPHERE CLIENT or navigate to VSPHERE MANAGEMENT NETWORK and click the vCenter Server Appliance FQDN.
-
Log in to VMware vSphere using vCenter credentials noted in Step 2 of this procedure.
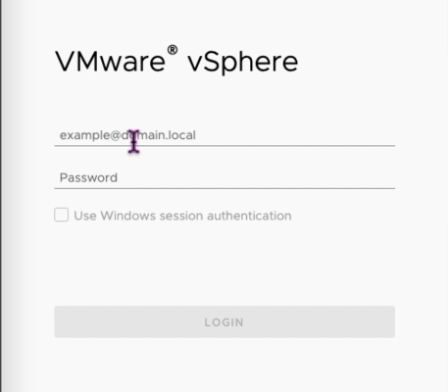
-
In vSphere client, you can verify the ESXi hosts that you created in GCVE portal.
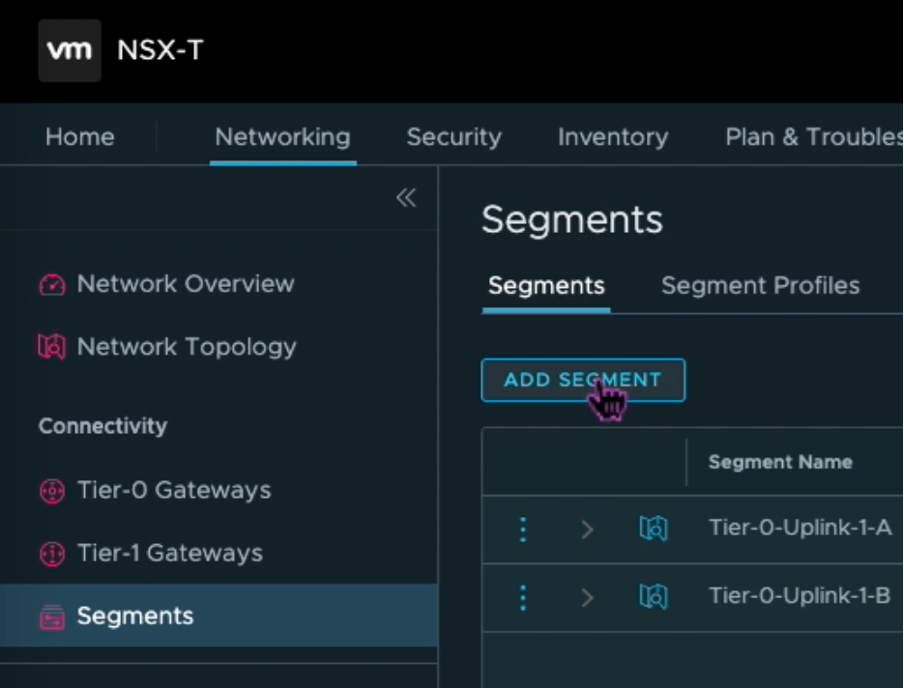
Create an NSX-T segment in the GCVE NSX-T portal
You can create and configure an NSX-T segment from the NSX Manager in the Google Cloud VMware Engine console. These segments are connected to the default Tier-1 gateway, and the workloads on these segments get East-West and North-South connectivity. Once you create the segment, it displays in vCenter.
-
In your GCVE private cloud, under Summary -> NSX-T login info, select View.
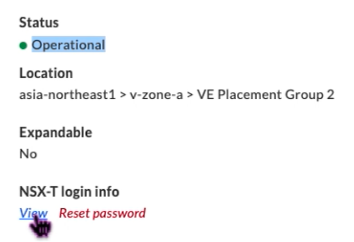
-
Make note of the NSX-T credentials.
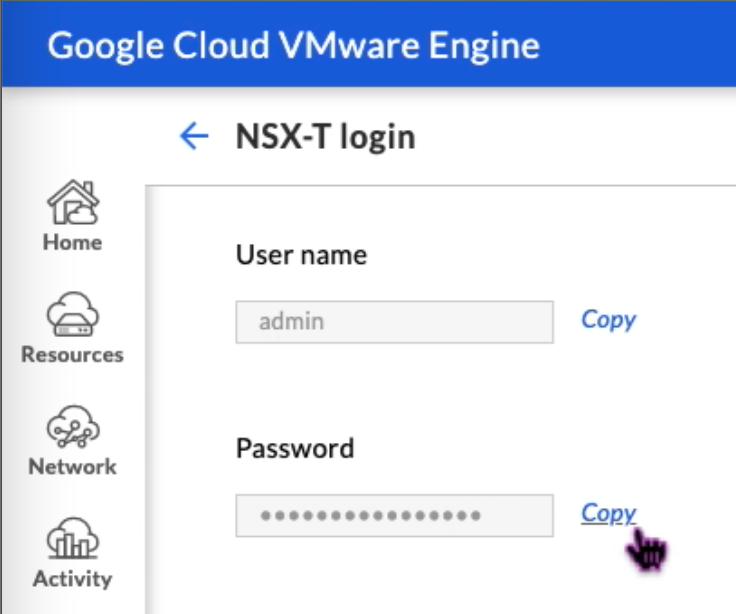
-
Launch the NSX Manager by navigating to VSPHERE MANAGEMENT NETWORK and click the NSX Manager FQDN.
-
Log in to the NSX Manager using the credentials noted in Step 2 of this procedure.
-
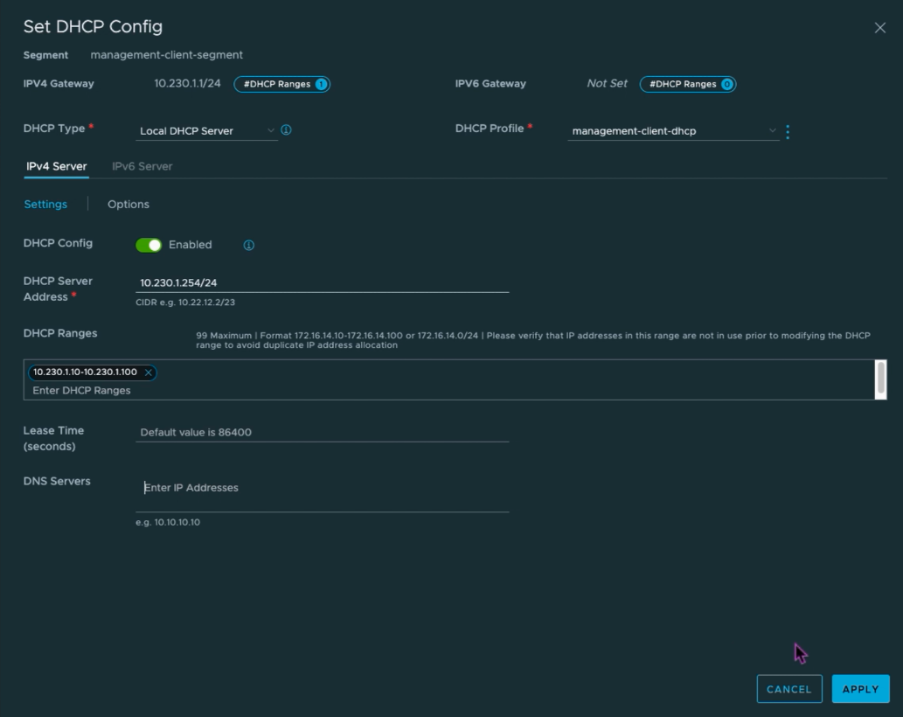
Set up DHCP service for the new segments or subnets.
-
Before you can create a subnet, set up a DHCP service.
-
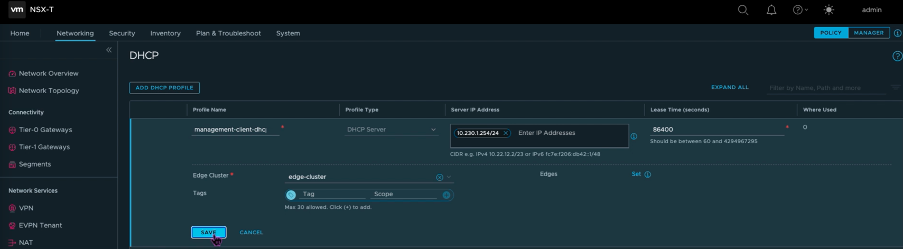
In NSX-T, go to Networking > DHCP. The networking dashboard shows that the service creates one tier-0 and one tier-1 gateway.
-
To begin provisioning a DHCP server, click Add DHCP Profile.
-
In the DHCP name field, enter a name for the Client-Management profile.
-
Select DHCP server as the Profile type.
-
In the Server IP address column, provide a DHCP service IP address range.
-
Select your Edge Cluster.
-
Click Save to create the DHCP service.
-
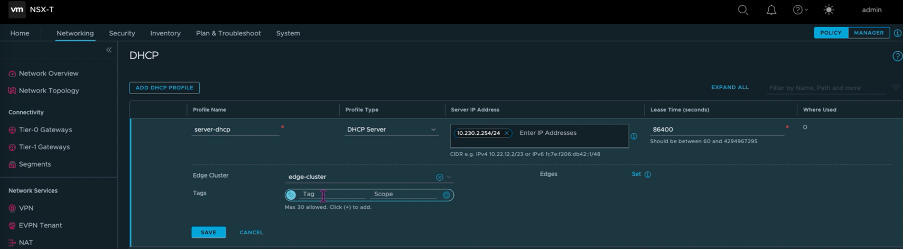
Repeat Steps 6 to 13 for Server DHCP range.
-
Create two separate segments: one for Client and Management interfaces, and another for Server interfaces.
-
In NSX-T, go to Networking > Segments.
-
Click Add Segment.
-
In the Segment Name field, enter a name for your Client Management segment.
-
In the Connected Gateway list, select Tier1 to connect to the tier-1 gateway.
-
In the Transport Zone list, select **TZ-OVERLAY Overlay**. -
In the Subnets column, enter the subnet range. Specify the subnet range with
.1as the last octet. For example, 10.12.2.1/24.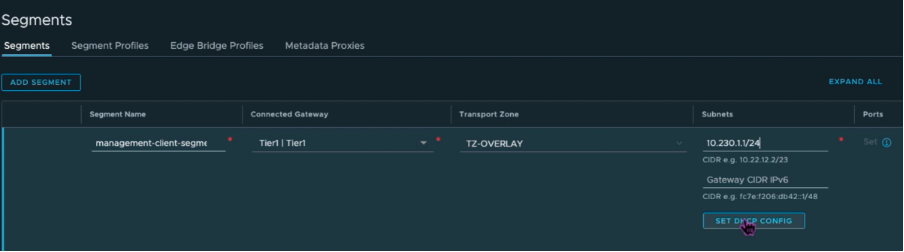
-
Click Set DHCP Config, and provide values for the DHCP Ranges field.
-
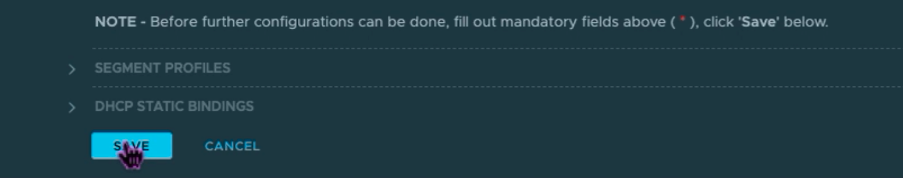
Click Apply to save your DHCP configuration.
-
Click Save.
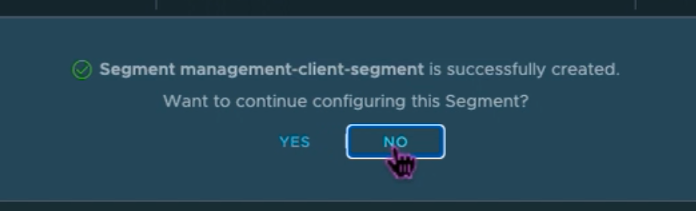
-
Repeat Steps 17 to 24 for Server segment as well.
- You can now select these network segments in vCenter when creating a VM.
For more information, see Creating your first subnet.
Install a NetScaler VPX instance on VMware cloud
After you have installed and configured Private Cloud on GCVE, you can use the vCenter to install virtual appliances on the VMware Engine. The number of virtual appliances that you can install depends on the amount of resource available on the Private Cloud.
To install NetScaler VPX instances on Private Cloud, perform these steps on a desktop connected to private cloud point-to-site VPN:
-
Download the NetScaler VPX instance setup files for ESXi host from the NetScaler downloads site.
-
Open VMware vCenter in a browser connected to your private cloud point-to-site VPN.
-
In the User Name and Password fields, type the administrator credentials, and then click Login.
-
On the File menu, click Deploy OVF Template.
-
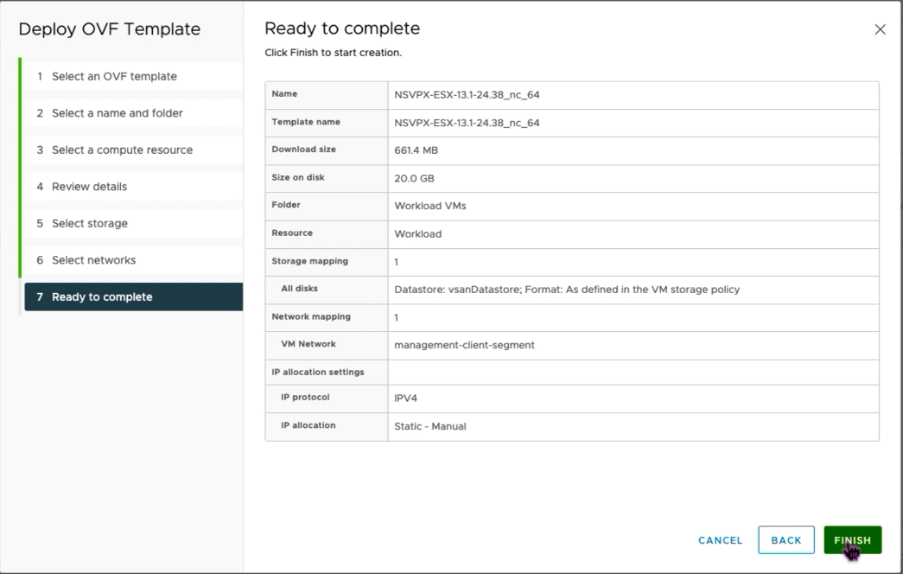
In the Deploy OVF Template dialog box, in Deploy from file field, browse to the location at which you saved the NetScaler VPX instance setup files, select the .ovf file, and click Next.
Note:
By default, the NetScaler VPX instance uses E1000 network interfaces. To deploy ADC with the VMXNET3 interface, modify the OVF to use VMXNET3 interface instead of E1000. Availability of VMXNET3 interface is limited by GCP infrastructure and might not be available in Google Cloud VMware Engine.
-
Map the networks shown in the virtual appliance OVF template to the networks that you configured on the NSX-T Manager. Click OK.
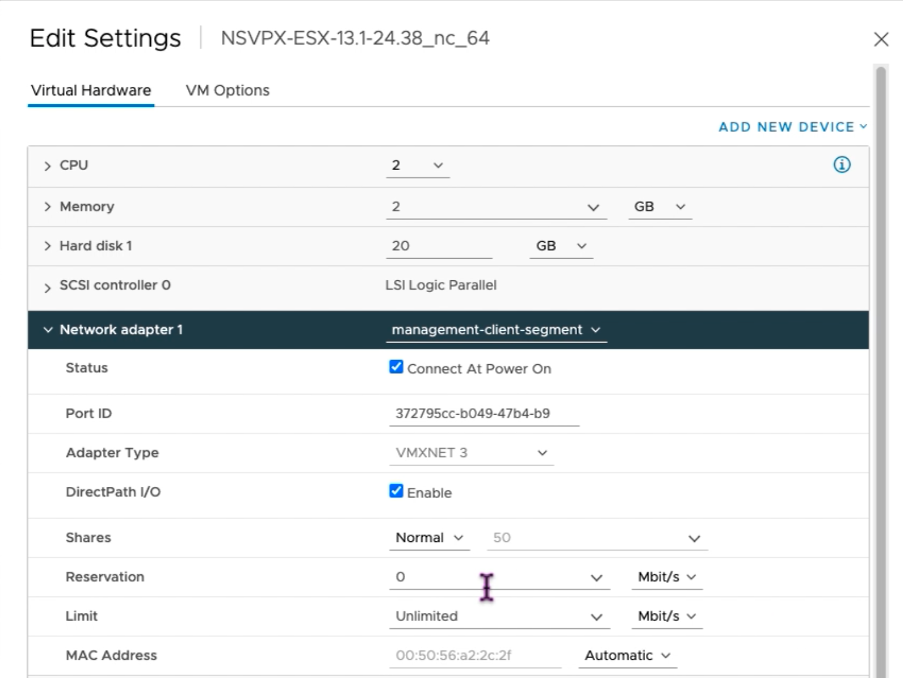
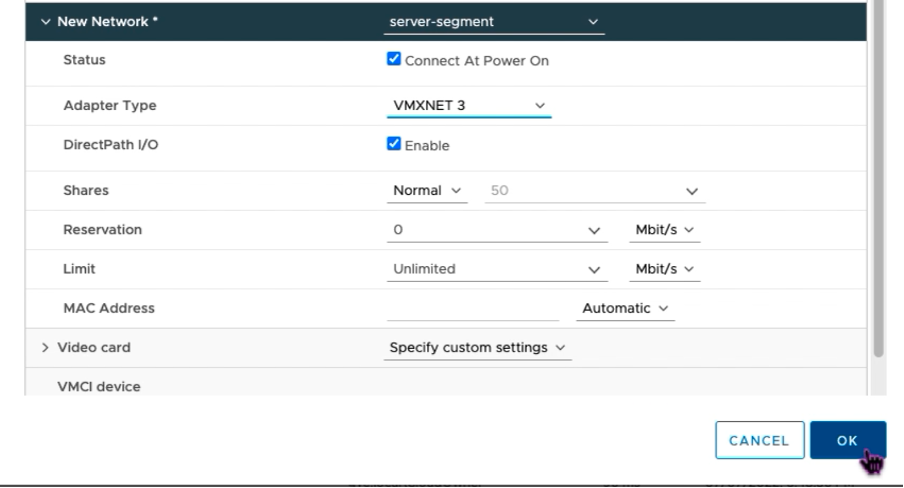
-
Click Finish to start installing a virtual appliance on VMware cloud.
-
You are now ready to start the NetScaler VPX instance. In the navigation pane, select the NetScaler VPX instance that you have installed and, from the right-click menu, select Power On. Click the Launch Web Console tab to emulate a console port.
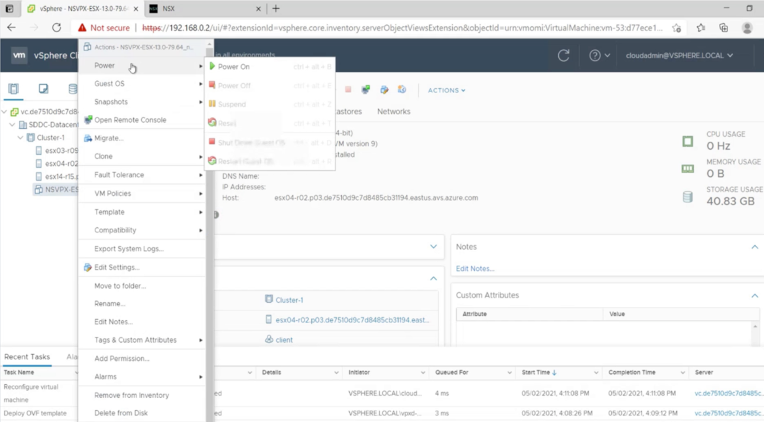
-
You are now connected to the NetScaler VM from the vSphere client.
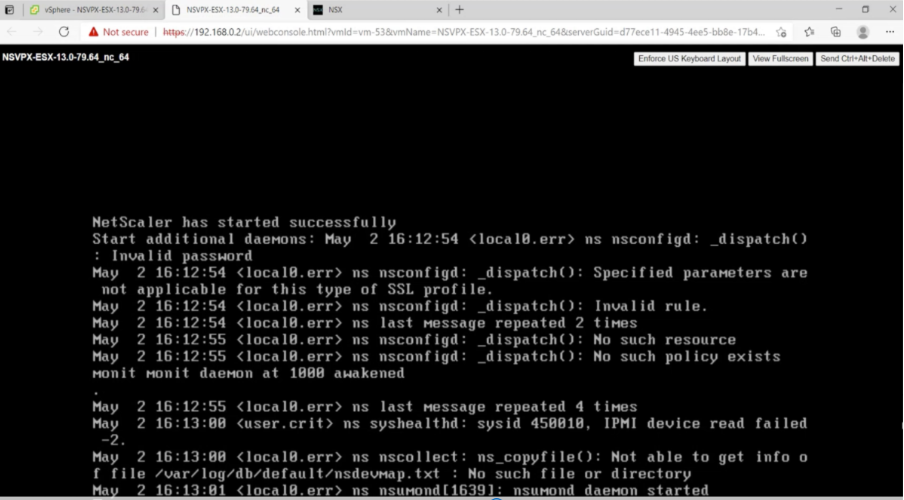
-
On first boot, set the management IP and gateway for the ADC instance.
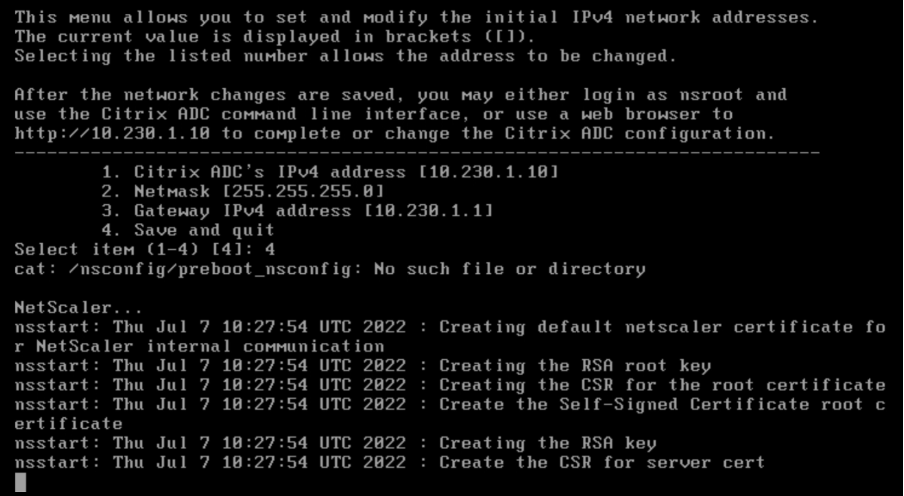
-
To access the NetScaler appliance by using the SSH keys, type the following command in the CLI:
ssh nsroot@<management IP address> <!--NeedCopy-->Example:
ssh nsroot@10.230.1.10 <!--NeedCopy--> -
You can verify the ADC configuration by using the
show ns ipcommand.
Assign a Public IP address to a NetScaler VPX instance on VMware cloud
After you have installed and configured NetScaler VPX instance on GCVE, you must assign a public IP address to the Client interface. Before assigning public IP addresses to your VMs, make sure that Public IP service is enabled for your Google Cloud region.
To enable Public IP service for a new region, follow these steps:
-
On GCVE console, navigate to Network > REGIONAL SETTINGS > Add Region.
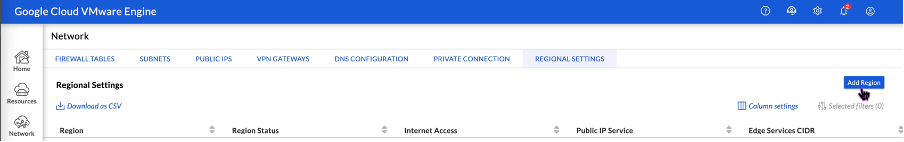
-
Select your region and enable Internet Access and Public IP Service.
-
Assign an Edge Services CIDR making sure that the CIDR range doesn’t overlap with any of your on-premises or other GCP/GCVE subnets (virtual networks).
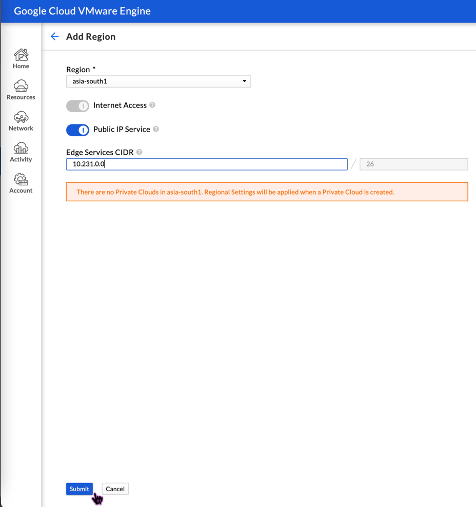
-
Public IP Service will be enabled for the selected region in a few minutes.
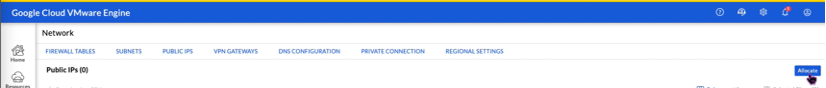
To assign public IP to the Client interface on the NetScaler VPX instance on GCVE, perform these steps on GCVE portal:
-
On GCVE console, navigate to Network > PUBLIC IPS > Allocate.
-
Enter a name for the public IP. Select your region, and select the private cloud where the IP will be used.
-
Provide the private IP for the interface to which you want the public IP to be mapped. This will be the private IP for your Client interface.
-
Click Submit.
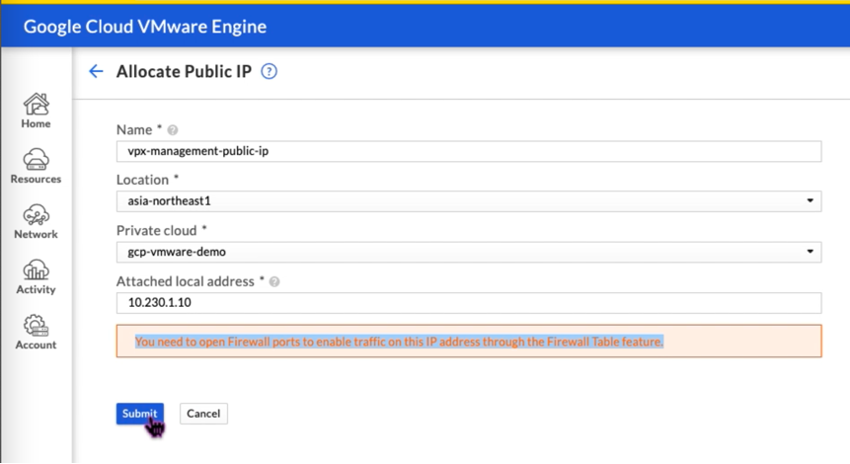
-
Public IP is ready to use in a few minutes.
-
You must add firewall rules to allow access to the public IP before you can use it. For more information, see Firewall rules.
In this article
- Prerequisites
- VMware cloud hardware requirements
- OVF Tool 1.0 system requirements
- Downloading the NetScaler VPX setup files
- Deploy Google Cloud VMware Engine
- Access your Private Cloud vCenter portal
- Create an NSX-T segment in the GCVE NSX-T portal
- Install a NetScaler VPX instance on VMware cloud
- Assign a Public IP address to a NetScaler VPX instance on VMware cloud