Deploy a VPX high-availability pair with private IP addresses across different AWS zones
You can configure two NetScaler VPX instances on two different subnets or two different AWS availability zones using private IP addresses in the INC mode. This solution can be easily integrated with the existing multizone VPX high-availability pair with elastic IP addresses. Therefore, you can use both the solutions together.
For more information about high availability, see High availability. For more information about INC, see Configuring high availability nodes in different subnets.
Note:
This deployment is supported from NetScaler release 13.0 build 67.39 onwards. This deployment is compatible with AWS Transit Gateway.
High availability pair with private IP addresses using AWS non-shared VPC
Prerequisites
Ensure that the IAM role associated with your AWS account has the following IAM permissions:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"ec2:DescribeInstances",
"ec2:DescribeAddresses",
"ec2:AssociateAddress",
"ec2:DisassociateAddress",
"ec2:DescribeRouteTables",
"ec2:DeleteRoute",
"ec2:CreateRoute",
"ec2:ModifyNetworkInterfaceAttribute",
"iam:SimulatePrincipalPolicy",
"iam:GetRole"
],
"Resource": "*",
"Effect": "Allow"
}
]
}
<!--NeedCopy-->
Deploy a VPX HA pair with private IP addresses using AWS non-shared VPC
The following is the summary of steps for deploying a VPX pair on two different subnets or two different AWS availability zones using private IP addresses.
- Create an Amazon virtual private cloud.
- Deploy two VPX instances in two different availability zones.
- Configure high availability
- Set up high availability in INC mode in both the instances.
- Add the respective route tables in the VPC that points to the client interface.
- Add a virtual server in the primary instance.
For steps 1, 2, and 3b, use the AWS console. For steps 3a and 3c, use the NetScaler VPX GUI or the CLI.
Step 1. Create an Amazon virtual private cloud (VPC).
Step 2. Deploy two VPX instance in two different availability zones with the same number of ENI (Network Interface).
For more information about how to create a VPC and deploy a VPX instance on AWS, see Deploy a NetScaler VPX standalone instance on AWS and Scenario: standalone instance
Step 3. Configure the ADC VIP addresses by choosing a subnet that does not overlap with the Amazon VPC subnets. If your VPC is 192.168.0.0/16, then to configure ADC VIP addresses, you can choose any subnet from these IP address ranges:
- 0.0.0.0 - 192.167.0.0
- 192.169.0.0 - 254.255.255.0
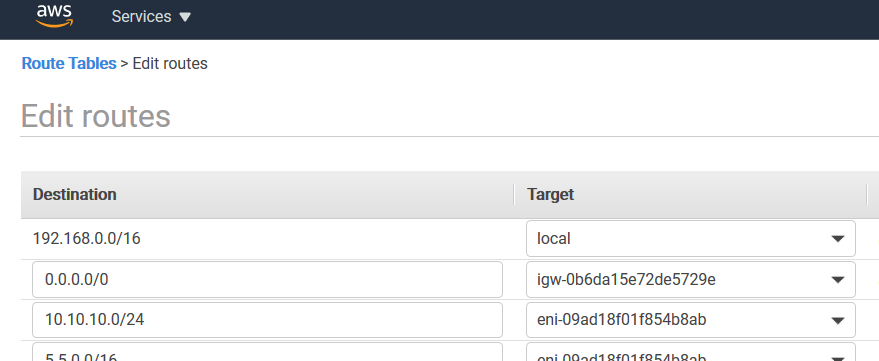
In this example, the chosen 10.10.10.0/24 subnet and created VIPs in this subnet. You can choose any subnet other than the VPC subnet (192.168.0.0/16).
Step 4. Add a route that points to the client interface (VIP) of the primary node from the VPC route table.
From the AWS CLI, type the following command:
aws ec2 create-route --route-table-id rtb-2272532 --destination-cidr-block 10.10.10.0/24 --gateway-id <eni-client-primary>
<!--NeedCopy-->
From the AWS GUI, perform the following steps to add a route:
- Open the Amazon EC2 console.
- In the navigation pane, choose Route Tables, and select the route table.
- Choose Actions, and click Edit routes.
- To add a route, choose Add route. For Destination, enter the destination CIDR block, a single IP address, or the ID of a prefix list. For gateway ID, select the ENI of a client interface of the primary node.
Note:
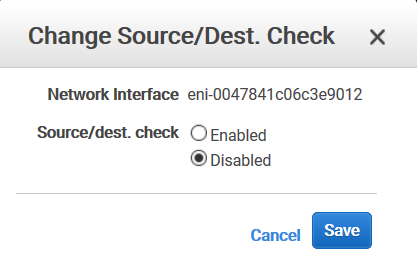
You must disable Source/Dest Check on the client ENI of the primary instance.
To disable the source/destination checking for a network interface using the console, perform the following steps:
- Open the Amazon EC2 console.
- In the navigation pane, choose Network Interfaces.
- Select the network interface of a primary client interface, and choose Actions, and click Change Source/Dest. Check.
- In the dialog box, choose Disabled, click Save.
Step 5. Configure high availability. You can use the NetScaler VPX CLI or the GUI to set up high availability.
Configure high availability by using the CLI
-
Set up high availability in INC mode in both the instances.
On the primary node:
add ha node 1 \<sec\_ip\> -inc ENABLED <!--NeedCopy-->On the secondary node:
add ha node 1 \<prim\_ip\> -inc ENABLED <!--NeedCopy--><sec_ip> refers to the private IP address of the management NIC of the secondary node.
<prim_ip> refers to the private IP address of the management NIC of the primary node.
-
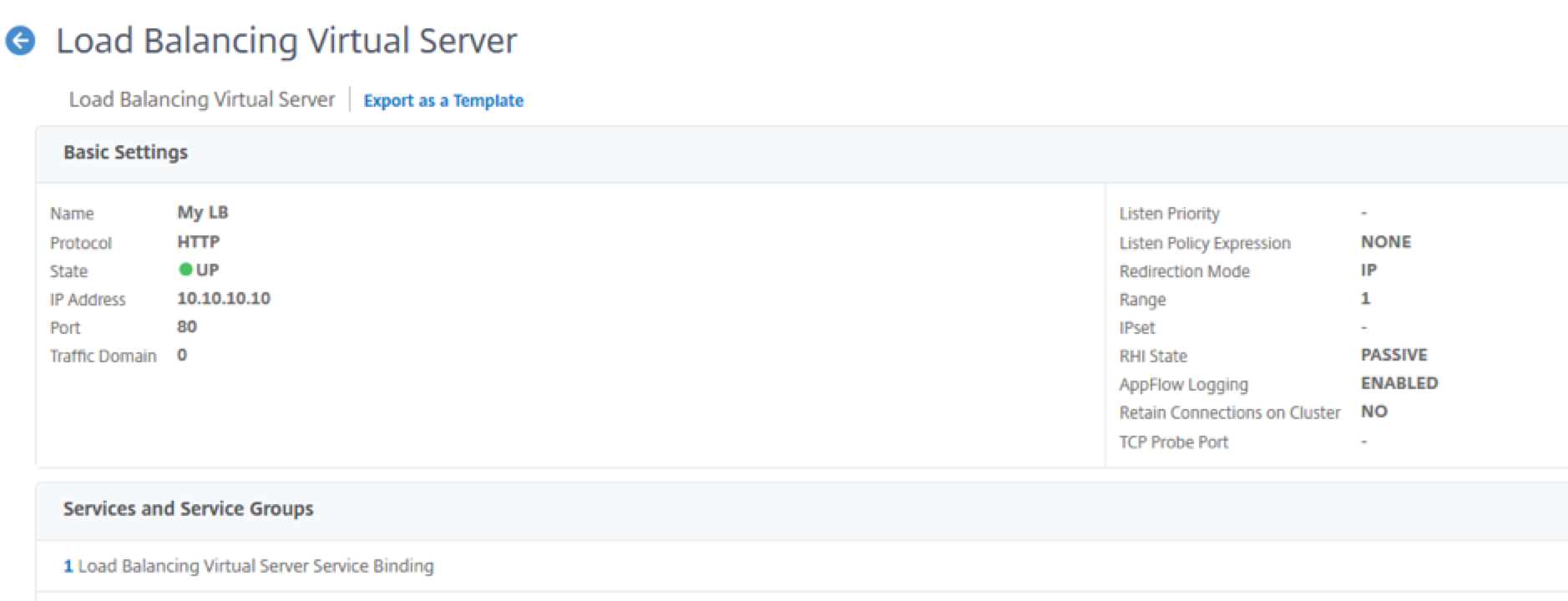
Add a virtual server on the primary instance. You must add it from the chosen subnet, for example, 10.10.10.0/24.
Type the following command:
add \<server\_type\> vserver \<vserver\_name\> \<protocol\> \<primary\_vip\> \<port\> <!--NeedCopy-->
Configure high availability by using the GUI
-
Set up high availability in INC mode on both the instances
-
Log on to the primary node with user name
nsrootand instance ID as password. -
Navigate to Configuration > System > High Availability, and click Add.
-
At the Remote Node IP address field, add the private IP address of the management NIC of the secondary node.
-
Select Turn on NIC (Independent Network Configuration) mode on self-node.
-
Under Remote System Login Credential, add the user name and password for the secondary node and click Create.
-
Repeat the steps in the secondary node.
-
Add a virtual server in the primary instance
Navigate to Configuration > Traffic Management > Virtual Servers > Add.
Deploy a VPX HA pair with private IP addresses using AWS shared VPC
In an AWS shared VPC model, the account that owns the VPC (owner) shares one or more subnets with other accounts (participants). Therefore, you have a VPC owner account and a participant account. After a subnet is shared, the participants can view, create, modify, and delete their application resources in the subnets shared with them. Participants cannot view, modify, or delete resources that belong to other participants or the VPC owner.
For information on AWS shared VPC, see the AWS documentation.
Note:
The configuration steps for deploying a VPX HA pair with private IP addresses using AWS shared VPC is the same as the Deploy a VPX HA pair with private IP addresses using AWS non-shared VPC with the following exception:
- The route tables in the VPC that points to the client interface must be added from the VPC owner account.
Prerequisites
-
Ensure that the IAM role associated with NetScaler VPX instance in the AWS participant account has the following IAM permissions:
"Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Allow", "Action": [ "ec2:DisassociateAddress", "iam:GetRole", "iam:SimulatePrincipalPolicy", "ec2:DescribeInstances", "ec2:DescribeAddresses", "ec2:ModifyNetworkInterfaceAttribute", “ec2:AssociateAddress”, "sts:AssumeRole" ], "Resource": "*" } ] } <!--NeedCopy-->Note:
The AssumeRole allows NetScaler VPX instance to assume the cross-account IAM role, which is created by the VPC owner account.
-
Ensure that the VPC owner account provides the following IAM permissions to the participant account using cross-account IAM role:
{ "Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Allow", "Action": [ "ec2:CreateRoute", "ec2:DeleteRoute", "ec2:DescribeRouteTables" ], "Resource": "*" } ] } <!--NeedCopy-->
Create cross-account IAM role
- Log in to the AWS web console.
- In the IAM tab, navigate to Roles and then choose Create Role.
-
Choose Another AWS account.
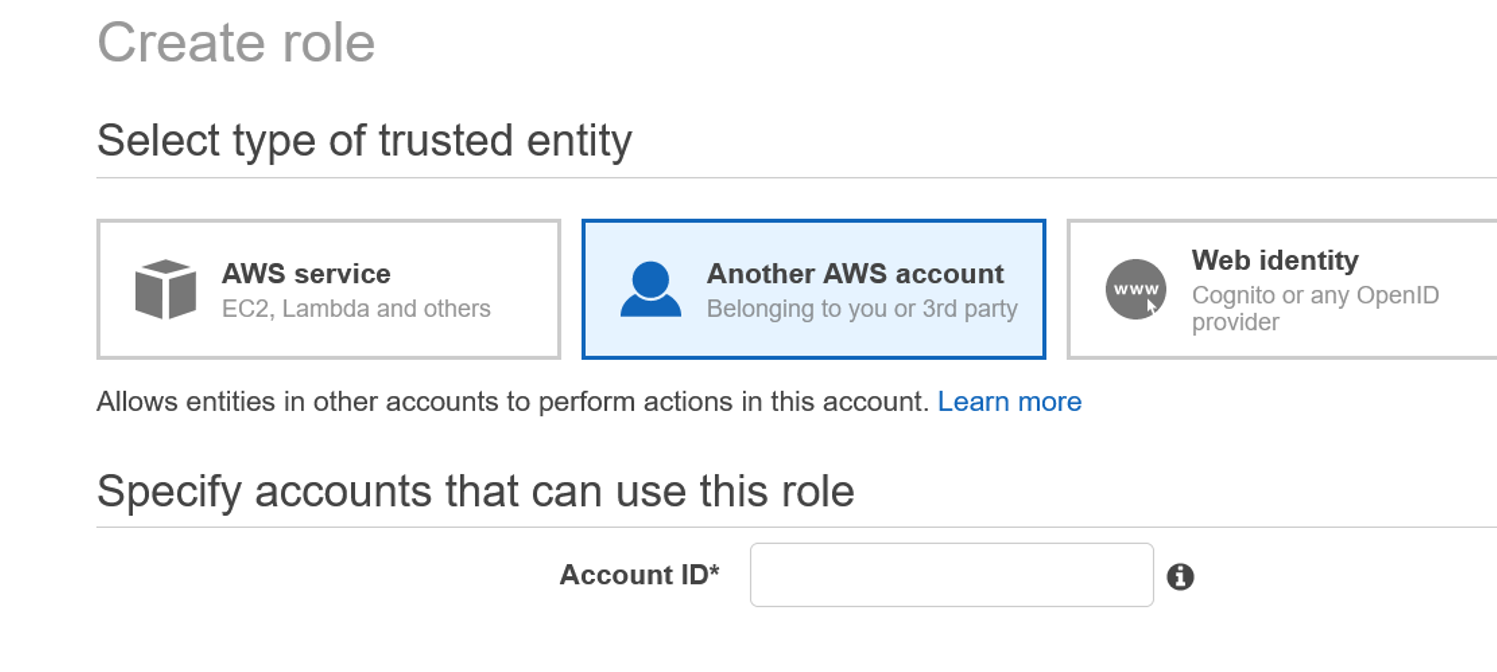
- Enter the 12-digit account ID number of the participant account that you want to grant administrator access to.
Set cross-account IAM role by using the NetScaler CLI
The following command enables NetScaler VPX instance to assume the cross-account IAM role that exists in the VPC owner account.
set cloud awsParam -roleARN <string>
<!--NeedCopy-->
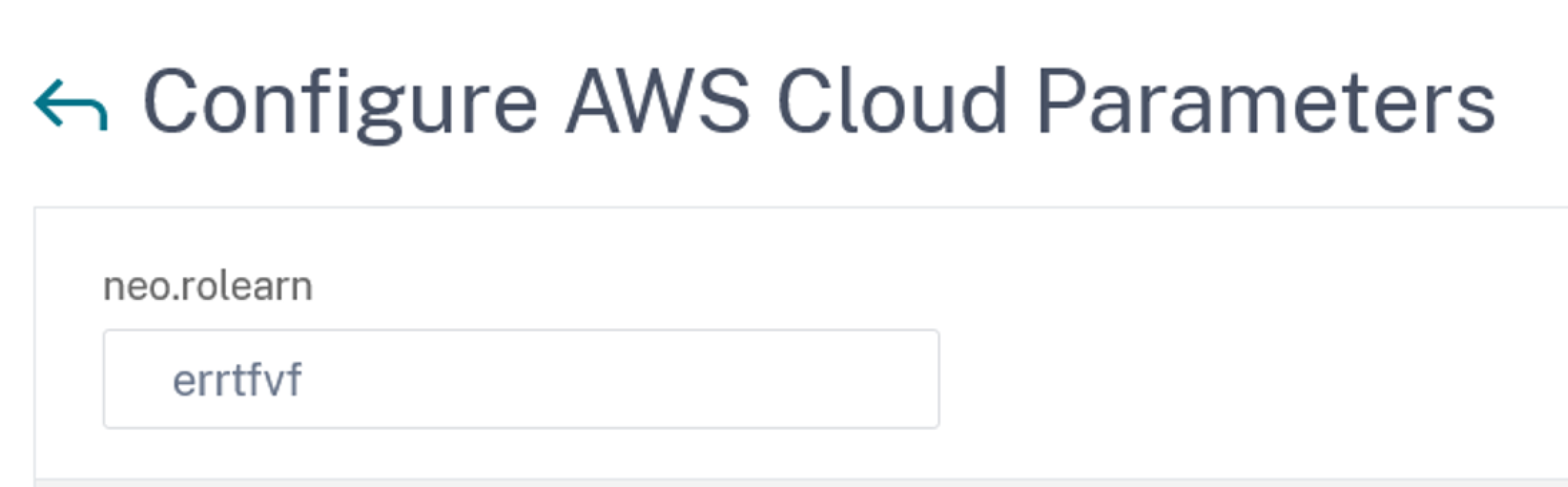
Set cross-account IAM role by using the NetScaler GUI
-
Sign into NetScaler appliance and navigate to Configuration > AWS > Change cloud parameters.
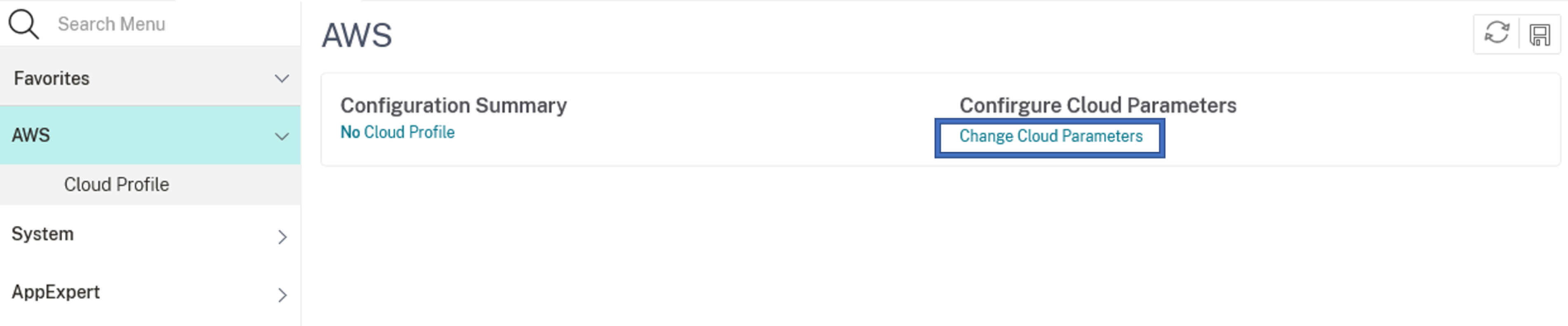
-
In the Configure AWS Cloud Parameters page, enter the value for the RoleARN field.
Scenario
In this scenario, a single VPC is created. In that VPC, two VPX instances are created in two availability zones. Each instance has three subnets - one for management, one for client, and one for back-end server.
The following diagrams illustrate the NetScaler VPX high availability setup in INC mode, on AWS. The custom subnet 10.10.10.10, which is not part of the VPC is used as VIP. Therefore, the 10.10.10.10 subnet can be used across availability zones.
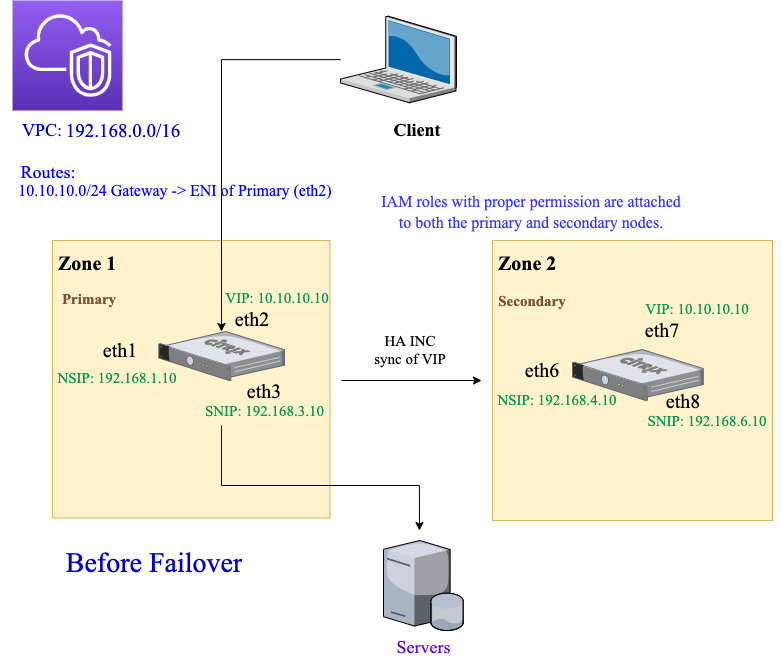
For this scenario, use CLI to configure high availability.
-
Set up high availability in INC mode on both the instances.
Type the following commands on the primary and the secondary nodes.
On the primary node:
add ha node 1 192.168.4.10 -inc enabled <!--NeedCopy-->Here, 192.168.4.10 refers to the private IP address of the management NIC of the secondary node.
On the secondary node:
add ha node 1 192.168.1.10 -inc enabled <!--NeedCopy-->Here, 192.168.1.10 refers to the private IP address of the management NIC of the primary node.
-
Add a virtual server on the primary instance.
Type the following command:
add lbvserver vserver1 http 10.10.10.10 80 <!--NeedCopy--> -
Save the configuration.
-
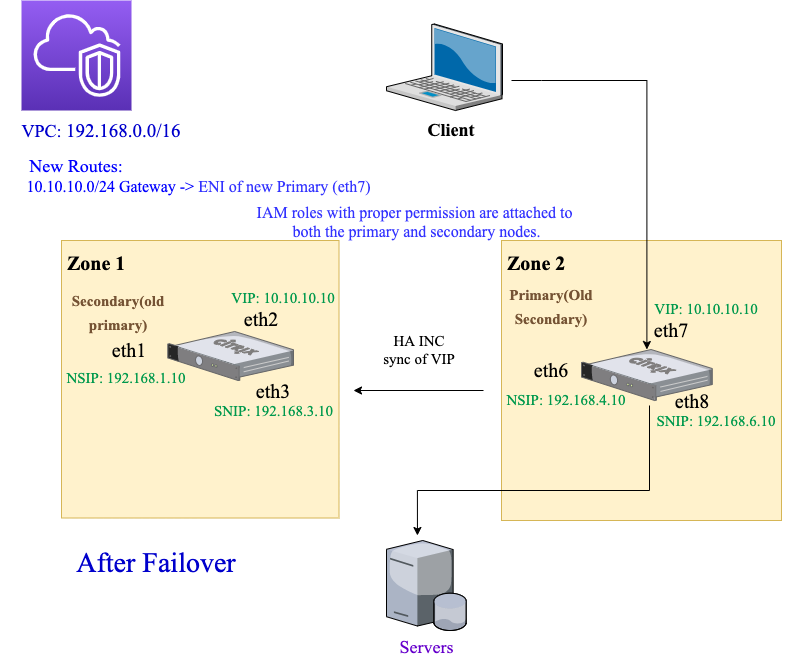
After a forced failover:
- The secondary instance becomes the new primary instance.
- The VPC route pointing to the primary ENI migrates to the secondary client ENI.
- Client traffic resumes to the new primary instance.
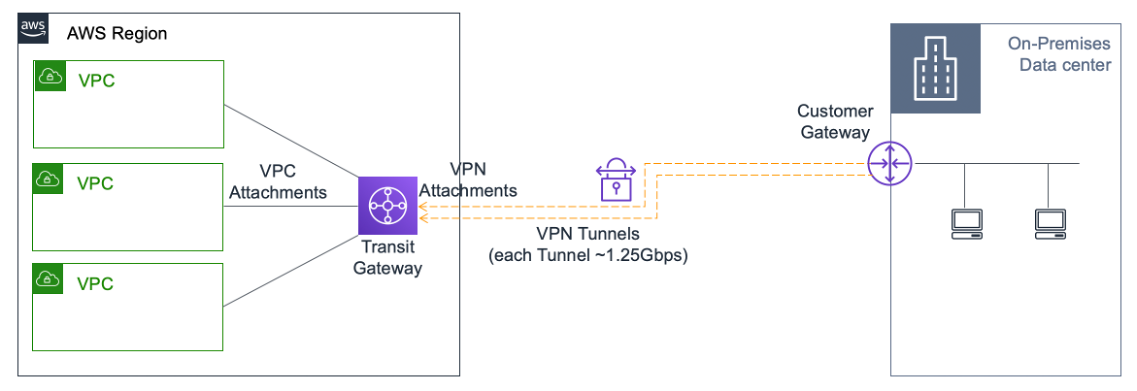
AWS Transit Gateway configuration for HA private IP solution
You need AWS Transit Gateway to make the private VIP subnet routable within the internal network, across AWS VPCs, regions, and On-premises networks. The VPC must connect to AWS Transit Gateway. A static route for the VIP subnet or IP pool inside the AWS Transit Gateway route table is created and pointed towards the VPC.
To configure AWS Transit Gateway, follow these steps:
- Open the Amazon VPC console.
- On the navigation pane, choose Transit Gateway Route Tables.
-
Choose the Routes tab, and click Create static route.
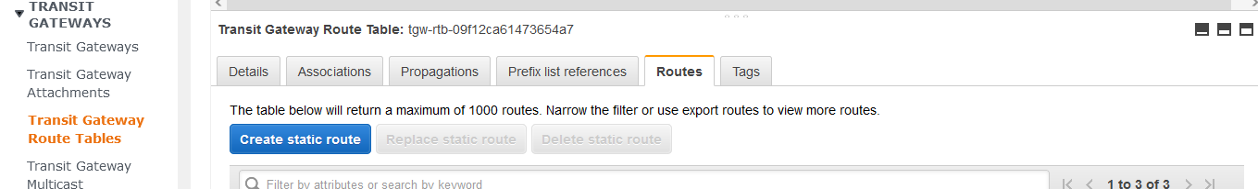
-
Create a static route where CIDR points to your private VIPS subnet and attachment points to the VPC having NetScaler VPX.
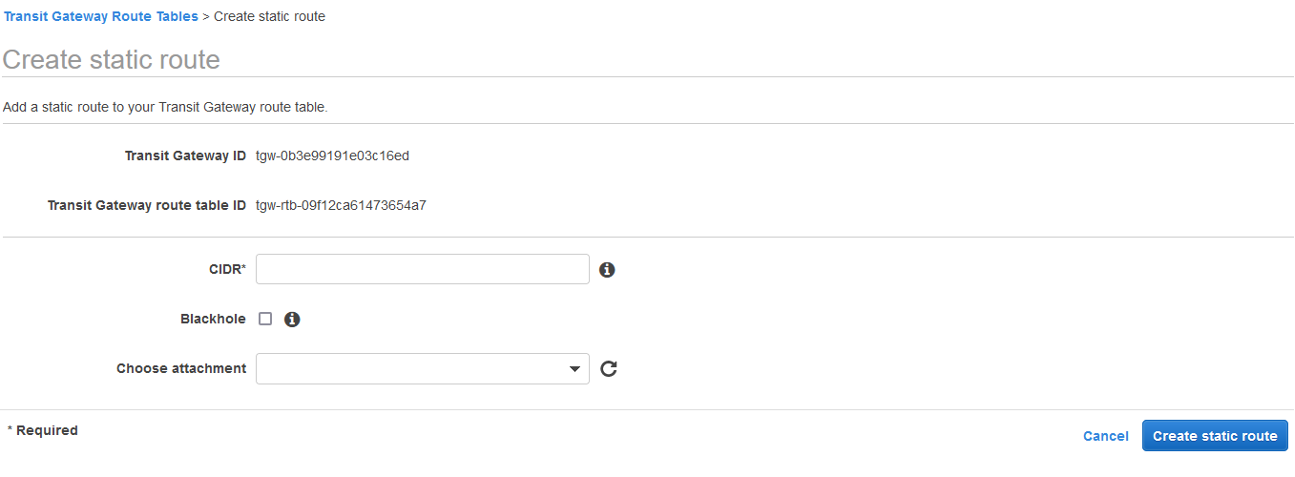
- Click Create static route, then choose Close.
Troubleshooting
If you face any issues while configuring HA private IP solution across multizone HA, check the following key points for troubleshooting:
- Both primary and secondary nodes have the same set of IAM permissions.
- INC mode is enabled on both the primary and secondary nodes.
- Both primary and secondary nodes have the same number of interfaces.
- While creating an instance, follow the same sequence of attaching interfaces on both primary and secondary nodes based on the device index number. Let’s say on a primary node, the client interface is attached first and the server interface is attached second. Follow the same sequence on the secondary node as well. If there is any mismatch, detach and reattach the interfaces in the correct order.
- You can verify the sequence of interfaces by following this navigation path: AWS console > Network & Security > ENI > Device Index number.
By default, the following device index numbers are assigned to these interfaces:
- Management interface – 0
- Client interface – 1
- Server interface – 2
-
If the sequence of device index numbers on primary ENI is: 0, 1, 2. The secondary ENI must also follow the same sequence of device index numbers: 0, 1, 2.
If there is a mismatch in the device index number sequence, all the mismatched routes are transferred to index 0, the management interface, to avoid any loss of routes. But you must still detach the interfaces and attach them again in the correct sequence to avoid the movement of routes to the Management interface because it can cause traffic congestion.
- If traffic does not flow, make sure the “Source/dest. Check” is disabled on the client interface of the primary node for the first time.
- Make sure the
cloudhadaemoncommand (ps -aux | grep cloudha) is running in Shell. - Make sure that the NetScaler firmware version is 13.0 build 70.x or later.
- For issues with the failover process, check the log file available at:
/var/log/cloud-ha-daemon.log