Configuration support for SameSite cookie attribute
The SameSite attribute indicates the browser whether the cookie can be used for cross-site context or only for same-site context. Also, if an application intends to be accessed in a cross-site context then it can do so only via the HTTPS connection. For details, see RFC6265.
Until Feb 2020, the SameSite attribute was not explicitly set in NetScaler. The browser took the default value (None). Not setting the SameSite attribute did not impact the NetScaler Gateway and authentication, authorization, and auditing deployments.
With certain browsers upgrade, such as Google Chrome 80, there is a change in the default cross-domain behavior of cookies. The SameSite attribute can be set to one of the following values. Default value for Google Chrome is set to Lax. For certain version of other browsers, the default value for the SameSite attribute might still be set to None.
- None: Indicates the browser to use a cookie in cross-site context only on secure connections.
- Lax: Indicates the browser to use a cookie for requests on the same domain and for cross-sites. For cross-site, only safe HTTP methods like GET request can use the cookie. For example, a GET request of a one subdomain abc.example.com can read the cookie of another subdomain xyz.example.com using a GET. For cross site, only safe HTTP methods are used because Safe HTTP methods do not alter the server state. For more details, see https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Set-Cookie/SameSite#lax
- Strict: Use the cookie only in the same site context.
If there is no SameSite attribute in the cookie, the Google Chrome assumes the functionality of SameSite = Lax. As a result, for deployments within an iframe with cross-site context that require cookies to be inserted by the browser, Google Chrome does not share cross-site cookies. As a result, the iframe within the website might not load.
Configure SameSite cookie attribute
A new cookie attribute named SameSite is added to the VPN and authentication, authorization, and auditing virtual servers. This attribute can be set at the global level and at the virtual server level.
To configure the SameSite attribute, you must do the following:
- Set the SameSite attribute for the virtual server
- Bind cookies to the patset (if the browser drops cross-site cookies)
Setting the SameSite attribute by using the CLI
To set the SameSite attribute at the virtual server level, use the following commands.
set vpn vserver VP1 -SameSite [STRICT | LAX | None]
set authentication vserver AV1 -SameSite [STRICT | LAX | None]
<!--NeedCopy-->
To set the SameSite attribute at the global level, use the following commands.
set aaa parameter -SameSite [STRICT | LAX | None]
set vpn parameter -SameSite [STRICT | LAX | None]
<!--NeedCopy-->
Note: The virtual server level setting takes preference over the global level setting. Citrix® recommends setting the SameSite cookie attribute at the virtual server level.
Binding cookies to the patset by using the CLI
If the browser drops cross-site cookies, you can bind that cookie string to the existing ns_cookies_SameSite patset so that the SameSite attribute is added to the cookie.
Example:
bind patset ns_cookies_SameSite "NSC_TASS"
bind patset ns_cookies_SameSite "NSC_TMAS"
<!--NeedCopy-->
Setting the SameSite attribute by using the GUI
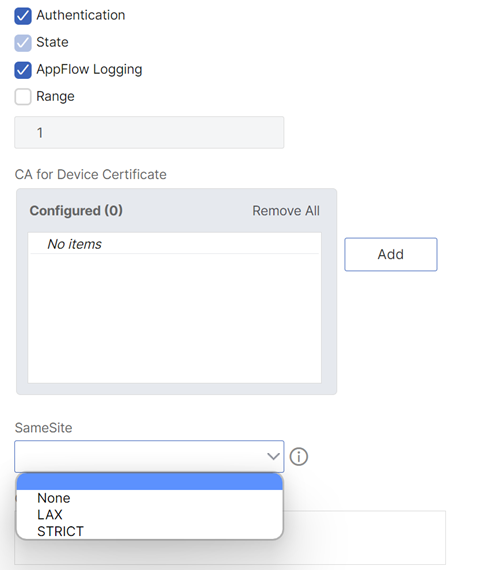
To set the SameSite attribute at the virtual server level:
- Navigate to Security > AAA – Application Traffic > Virtual Servers.
- Select a virtual server and click Edit.
- Click the edit icon in the Basic Settings section and click More.
- In SameSite, select the option as required.
To set the SameSite attribute at the global level:
-
Navigate to Security > AAA – Application Traffic > Change Authentication Settings.
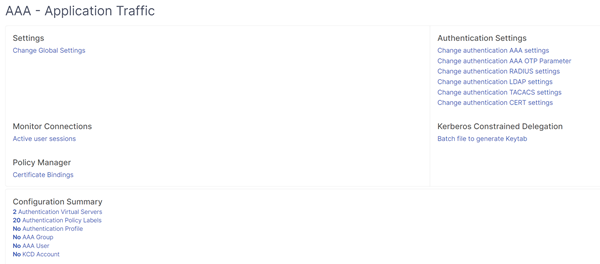
-
In the Configure AAA Parameter page, click the SameSite list, and select the option as required.