-
Configuring the VPN User Experience
-
How to Configure Full VPN Setup on a Citrix Gateway Appliance
-
Integrating the Citrix Gateway plug-in with Citrix Receiver™
-
AlwaysOn VPN before Windows logon (Formally AlwaysOn service)
-
-
Communication Flow in a Double-Hop DMZ Deployment
-
Installing and Configuring Citrix Gateway in a Double-Hop DMZ
-
Maintaining and Monitoring the System
-
Deploying with Citrix Endpoint Management, Citrix Virtual Apps, and Citrix Virtual Desktops™
-
Accessing Citrix Virtual Apps and Desktops™ Resources with the Web Interface
-
Integrating Citrix Gateway with Citrix Virtual Apps and Desktops
-
Configuring Additional Web Interface Settings on Citrix Gateway
-
Configuring Access to Applications and Virtual Desktops in the Web Interface
-
-
Integrate Citrix Gateway with Citrix Virtual Apps and Desktops
-
Configuring Settings for Your Citrix Endpoint Management Environment
-
Configuring Load Balancing Servers for Citrix Endpoint Management
-
Configuring Load Balancing Servers for Microsoft Exchange with Email Security Filtering
-
Configuring Citrix Endpoint Management NetScaler® Connector (XNC) ActiveSync Filtering
-
Allowing Access from Mobile Devices with Citrix Mobile Productivity Apps
-
Configuring Domain and Security Token Authentication for Citrix Endpoint Management
-
Configuring Client Certificate or Client Certificate and Domain Authentication
-
-
Citrix Gateway Enabled PCoIP Proxy Support for VMware Horizon View
-
Proxy Auto Configuration for Outbound Proxy support for Citrix Gateway
-
Integrate Citrix Gateway with Citrix Virtual Apps and Desktops
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Communication flow in a double-hop DMZ deployment
To understand the configuration issues involved in a double-hop DMZ deployment, you must have a basic understanding of how the various Citrix® Gateway and Citrix Virtual Apps™ components in a double-hop DMZ deployment communicate to support a user connection. The connection process for StoreFront and the Web Interface is the same.
Although the user connection process occurs in one continuous flow, the following high-level steps are involved in the process.
- Authenticate users
- Create a session ticket
- Start the Citrix Workspace™ app
- Complete the connection
The following figure shows the steps that occur in the user connection process to either StoreFront™ or the Web Interface. In the secure network, computers running Citrix Virtual Apps are also running the Secure Ticket Authority (STA), XML Service, and published applications.
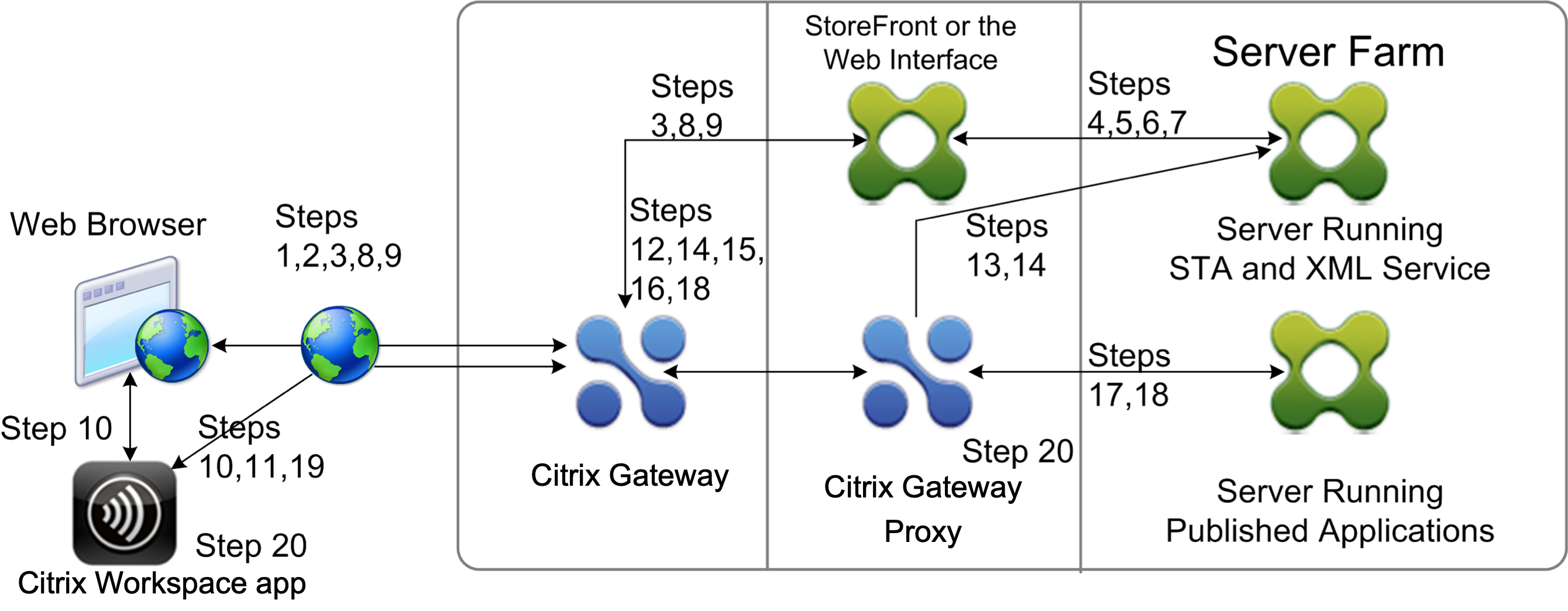
Connection process
Authenticating users is the first step of the user connection process in a double-hop DMZ deployment.
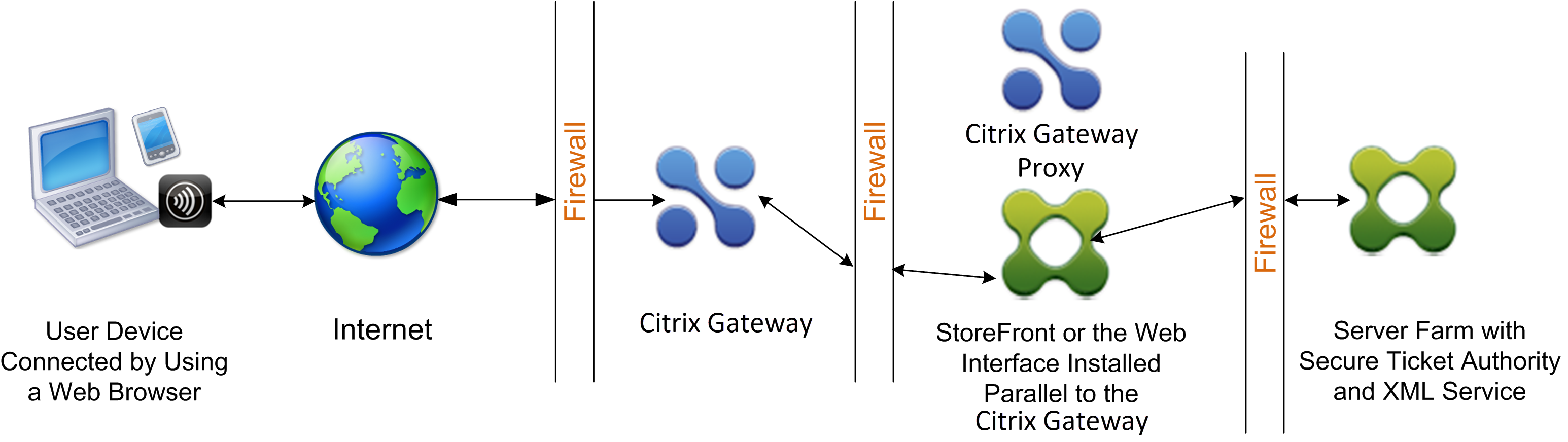
The following figure shows the user connection process in this deployment.
During the user authentication stage, the following basic process occurs:
- A user types the address of Citrix Gateway, such as https://www.ng.wxyco.com in a web browser to connect to Citrix Gateway in the first DMZ. If you enabled logon page authentication on Citrix Gateway, Citrix Gateway authenticates the user.
- Citrix Gateway in the first DMZ receives the request.
- Citrix Gateway redirects the web browser connection to the Web Interface.
- The Web Interface sends the user credentials to the Citrix XML service running in the server farm in the internal network.
- The Citrix XML Service authenticates the user.
-
The XML Service creates a list of the published applications that the user is authorized to access and sends this list to the Web Interface.
Note:
-
If you enable authentication on Citrix Gateway, the appliance sends the Citrix Gateway logon page to the user. The user enters authentication credentials on the logon page and the appliance authenticates the user. Citrix Gateway then returns the user credentials to the Web Interface.
-
If you do not enable authentication, Citrix Gateway does not perform authentication. The appliance connects to the Web Interface, retrieves the Web Interface logon page, and sends the Web Interface logon page to the user. The user enters authentication credentials on the Web Interface logon page and Citrix Gateway passes the user credentials back to the Web Interface.
Creating the session ticket is the second stage of the user connection process in a double-hop DMZ deployment.
During the session ticket creation stage, the following basic process occurs:
-
- The Web Interface communicates with both the XML Service and the Secure Ticket Authority (STA) in the internal network to produce session tickets for each of the published applications the user is authorized to access. The session ticket contains an alias address for the computer running Citrix Virtual Apps that hosts a published application.
- The STA saves the IP addresses of the servers that host the published applications. The STA then sends the requested session tickets to the Web Interface. Each session ticket includes an alias that represents the IP address of the server that hosts the published application, but not the actual IP address.
-
The Web Interface generates an ICA® file for each of the published applications. The ICA file contains the ticket issued by the STA. The Web Interface then creates and populates a webpage with a list of links to the published applications and sends this webpage to the web browser on the user device.
Starting Citrix Workspace app is the third stage of the user connection process in a double-hop DMZ deployment. The basic process is as follows:
-
The user clicks a link to a published application in the Web Interface. The Web Interface sends the ICA file for that published application to the browser for the user device.
The ICA file contains data instructing the web browser to start Receiver.
The ICA file also contains the fully qualified domain name (FQDN) or the Domain Name System (DNS) name of the Citrix Gateway in the first DMZ.
-
The web browser starts Receiver and the user connects to Citrix Gateway in the first DMZ by using the Citrix Gateway name in the ICA file. Initial SSL/TLS handshaking occurs to establish the identity of the server running Citrix Gateway.
Completing the connection is the fourth and last stage of the user connection process in a double-hop DMZ deployment.
During the connection completion stage, the following basic process occurs:
- The user clicks a link to a published application in the Web Interface.
- The web browser receives the ICA file generated by the Web Interface and starts Citrix Workspace app. Note: The ICA file contains code that instructs the web browser to start Citrix Workspace app.
- Citrix Workspace app initiates an ICA connection to Citrix Gateway in the first DMZ.
- Citrix Gateway in the first DMZ communicates with the Secure Ticket Authority (STA) in the internal network to resolve the alias address in the session ticket to the real IP address of a computer running Citrix Virtual Apps or StoreFront. This communication is proxied through the second DMZ by the Citrix Gateway proxy.
- Citrix Gateway in the first DMZ completes the ICA connection to Citrix Workspace app.
- Citrix Workspace app can now communicate through both Citrix Gateway appliances to the computer running Citrix Virtual Apps on the internal network.
The detailed steps for completing the user connection process are as follows:
- Citrix Workspace app sends the STA ticket for the published application to Citrix Gateway in the first DMZ.
- Citrix Gateway in the first DMZ contacts the STA in the internal network for ticket validation. To contact the STA, Citrix Gateway establishes a SOCKS or SOCKS with SSL connection to the Citrix Gateway proxy in the second DMZ.
- The Citrix Gateway proxy in the second DMZ passes the ticket validation request to the STA in the internal network. The STA validates the ticket and maps it to the computer running Citrix Virtual Apps that hosts the published application.
- The STA sends a response to the Citrix Gateway proxy in the second DMZ, which is passed to Citrix Gateway in the first DMZ. This response completes the ticket validation and includes the IP address of the computer that hosts the published application.
- Citrix Gateway in the first DMZ incorporates the address of the Citrix Virtual Apps server into the user connection packet and sends this packet to the Citrix Gateway proxy in the second DMZ.
- The Citrix Gateway proxy in the second DMZ makes a connection request to the server specified in the connection packet.
- The server responds to the Citrix Gateway proxy in the second DMZ. The Citrix Gateway proxy in the second DMZ passes this response to Citrix Gateway in the first DMZ to complete the connection between the server and Citrix Gateway in the first DMZ.
- Citrix Gateway in the first DMZ completes the SSL/TLS handshake with the user device by passing the final connection packet to the user device. The connection from the user device to the server is established.
- ICA traffic flows between the user device and the server through Citrix Gateway in the first DMZ and the Citrix Gateway proxy in the second DMZ.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.