Manage global lists to bypass WAF or deny requests
An application can receive requests from trusted and untrusted sources. You might want to bypass the NetScaler Web App Firewall for the requests from a trusted source. And, when the requests come from certain untrusted sources, you want to strictly block those requests.
In a NetScaler Web App Firewall profile, you can configure global lists to bypass Web App Firewall or deny requests. If the incoming requests match the global bypass list, they skip the Web App Firewall in NetScaler. If the incoming requests match the global deny list, NetScaler Web App Firewall blocks those requests and applies the defined action.
The bypass and deny lists support URL, IPv4, and IPv6 addresses. You can specify them using literals, PCRE, and expressions.
Configure the global bypass and deny list using the CLI
Before you begin, create a Web App Firewall profile and enable bypass and deny lists in the profile settings.
-
Create a Web App Firewall profile.
add appfw profile <profile-name> <!--NeedCopy-->Example
add appfw profile example-profile <!--NeedCopy-->Note
By default, bypass list and deny list are disabled. To view profile settings, run the following command:
sh appfw profile <profile-name> -
Run the following command to enable bypass list and deny list.
set appfw profile <profile-name> -bypasslist on -denylist on <!--NeedCopy-->
Bind the Web App Firewall profile with a global bypass list
Run the following command to bind the rules to a global bypass list:
bind appfw profile <profile-name> -bypasslist <String|PCRE|Expression|IP-address> -valuetype <literal|PCRE|expression> -ruleaction log -location <url|ipv4|ipv6>
<!--NeedCopy-->
-
Example-1:
bind appfw profile example-profile -bypasslist http://www.example.com -valuetype literal -ruleaction log -location url <!--NeedCopy-->This example uses a literal value. When the incoming request URL contains
http://www.example.com, the request bypasses the WAF checks and logs an event in the NetScaler appliance. -
Example-2:
bind appfw profile example-profile -bypasslist http://www.example[n] -valuetype PCRE -ruleaction log -location url <!--NeedCopy-->This example uses a PCRE value. When the incoming request URL contains
http://www.exampleand followed by the lettern, the request bypasses the WAF checks and logs an event in the NetScaler appliance. -
Example-3:
bind appfw profile example-profile -bypasslist http.req.url.contains("example") -valuetype expression -ruleaction log <!--NeedCopy-->This example uses an expression. When the incoming request URL contains
exampleanywhere in the URL, the request bypasses the WAF checks and logs an event in the NetScaler appliance.Important
Do not enter the location value when you specify the expression value type.
-
Example-4:
bind appfw profile example-profile -bypasslist 10.10.10.10 -valuetype expression -ruleaction log -location ipv4 <!--NeedCopy-->This example uses an IPv4 address. When the incoming request URL contains an IP address
10.10.10.10, the request bypasses the WAF checks and logs an event in the NetScaler appliance.Similarly, you can specify the IPv6 address. To do so, set the location value to
ipv6in this command. -
Example-5:
bind appfw profile example-profile -bypasslist cookie -valuetype literal -ruleaction log -location headervalue <!--NeedCopy-->This example uses a header value. When the incoming request contains an header value as
cookie, the request bypasses the Web App Firewall checks and logs an event in NetScaler. -
Example-6:
bind appfw profile example-profile -bypasslist token -valuetype literal -ruleaction log -location headername <!--NeedCopy-->This example uses a header name. When the incoming request URL contains an header name as
token, the request bypasses the Web App Firewall checks and logs an event in NetScaler.
Bind the Web App Firewall profile with a global deny list
Run the following command to bind the rules to a global deny list:
bind appfw profile <profile-name> -bypasslist <String|PCRE|Expression|IP-address> -valuetype <literal|PCRE|expression> -ruleaction <log|none|REDIRECT|RESET> -location <url|ipv4|ipv6>
<!--NeedCopy-->
-
Example-1:
bind appfw profile example-profile -denylist http://www.example.com -valuetype literal -ruleaction log -location url <!--NeedCopy-->This example uses a literal value. When the incoming request URL contains
http://www.example.com, the NetScaler Web App Firewall blocks the request and logs an event in the NetScaler appliance. -
Example-2:
bind appfw profile example-profile -denylist http://www.example[n] -valuetype PCRE -ruleaction none -location url <!--NeedCopy-->This example uses a PCRE value. When the incoming request URL contains
http://www.exampleand followed by the lettern, the NetScaler Web App Firewall blocks the request.Note:
When you specify the
-ruleactionasnone, NetScaler Web App Firewall performs the default action. The default action for bypass and deny list is allow.For more information on rule action, see Overview of security checks.
-
Example-3:
bind appfw profile example-profile -denylist http.req.url.contains("example") -valuetype expression -ruleaction REDIRECT <!--NeedCopy-->This example uses an expression. When the incoming request URL contains
exampleanywhere in the URL, the NetScaler Web App Firewall blocks and redirects the request. -
Example-4:
bind appfw profile example-profile -denylist 10.10.10.10 -valuetype expression -ruleaction RESET -location ipv4 <!--NeedCopy-->This example uses an IPv4 address. When the incoming request URL contains an IP address
10.10.10.10, the NetScaler Web App Firewall blocks the request and resets the connection.Similarly, you can specify the IPv6 address. To do so, set the location value to
ipv6in this command. -
Example-5:
bind appfw profile example-profile -denylist cookie -valuetype literal -ruleaction log -location headervalue <!--NeedCopy-->This example uses a header value. When the incoming request contains an header value as
cookie, NetScaler Web App Firewall blocks request. -
Example-6:
bind appfw profile example-profile -denylist token -valuetype literal -ruleaction log -location headername <!--NeedCopy-->This example uses a header name. When the incoming request contains an header name as
token, NetScaler Web App Firewall blocks request.
Configure the global bypass and deny list using the GUI
Before you begin, create a Web App Firewall profile and enable bypass and deny lists in the profile settings.
- Navigate to Security > NetScaler Web App Firewall > Profiles.
- Select the profile for which you want to add the global bypass and deny lists.
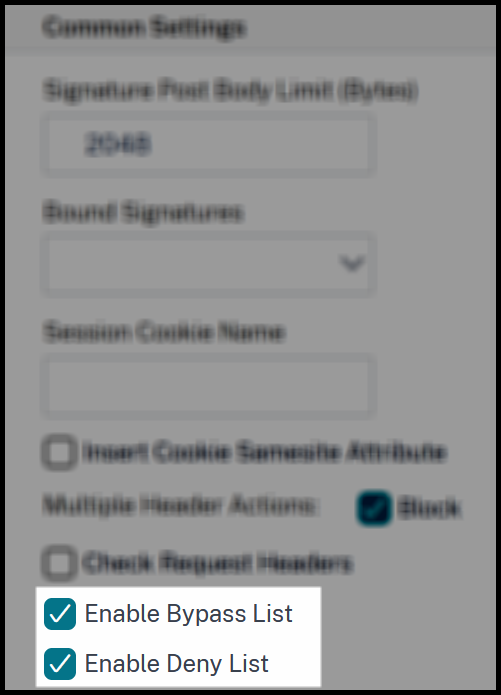
- In the NetScaler Web App Firewall Profile page, click Profile Settings under Advanced Settings.
-
In Common Settings, select the following options:
- Enable Bypass List
- Enable Deny List
- Click OK and Done.
Add a global bypass list
Complete the following steps to add a global bypass list:
- Navigate to Security > NetScaler Web App Firewall > Profiles.
- Select the profile for which you want to add a global bypass list.
- In the NetScaler Web App Firewall Profile page, click Global Bypass/Deny list under Advanced Settings.
- In Global Bypass List, click Add.
-
Specify the following in the Create AppFirewall Bypass List Binding page:
- Bypass List Value Type: It supports literals, PCREs, and expressions.
- Bypass List Value: Specify a value depending on the value type.
- Bypass List Action: After the request bypasses the WAF checks, the defined action applies for the request. If the action is set to Log, it logs an event in the NetScaler appliance.
- Bypass List Location: Set the location value. If you specify IPv4, the profile looks for the IPv4 address in the incoming request.
- Click Create.
Add a global deny list
Complete the following steps to add a global deny list:
- Navigate to Security > NetScaler Web App Firewall > Profiles.
- Select the profile for which you want to add a global deny list.
- In the NetScaler Web App Firewall Profile page, click Global Bypass/Deny list under Advanced Settings.
- In Global Deny List, click Add.
-
Specify the following in the Create AppFirewall Deny List Binding page:
- Deny List Value Type: It supports literals, PCREs, and expressions.
- Deny List Value: Specify a value depending on the value type.
- Deny List Action: After the NetScaler Web App Firewall blocks the request, the defined action applies for the request. If the action is set to Reset, the Web App Firewall resets the connection.
- Log: It logs an event in the NetScaler appliance whenever the NetScaler Web App Firewall blocks the request.
- Deny List Location: Set the location value. If you specify IPv4, the profile looks for the IPv4 address in the incoming request.
- Click Create.
Support for Global Deny List
The Global Deny Lists feature improves your security by stopping malicious traffic that existing security methods do not block. Traditional methods, like responder policies, needed manual updates and lacked universal application. The feature provides a system-wide defense, making sure that all traffic is checked against threat rules.
Some of the benefits are:
- Achieves global coverage: The system-wide application eliminates the need for individual virtual server binding, ensuring comprehensive coverage for all traffic passing through NetScaler.
- Secures rule delivery: Rules are delivered through NetScaler Console, using the existing encrypted signature delivery process. This approach ensures that delivery is secure and protected from tampering.
- Ensures unconditional evaluation: Traffic is evaluated regardless of the Web App Firewall for NetScaler Gateway profile or API specification settings.
- Supports rule specialization: You can customize rules using new PI expressions for specific virtual server or traffic types, which helps minimize the impact on legitimate traffic.
Note:
If a CVE is mitigated by using deny rules, the rules are to be shared using the encrypted signature delivery process.
Manage Global Deny lists status
Pre-requisites
To use the Global Deny Lists feature, ensure that you meet the following requirements:
- NetScaler firmware version 14.1-60.X or later.
- The Web App Firewall for authentication, authorization, and auditing or VPN feature is enabled.
- Opt in to receive signatures through NetScaler Console.
The Global Deny Lists feature is enabled by default to provide immediate protection.
Notes:
The Global Deny Lists feature is only available to customers using NetScaler Console on-prem or NetScaler Console service.
We recommend enabling the feature for security reasons.
To disable the Global Deny Lists feature by using CLI
At command prompt, type:
set system parameter -DenyList OFF
Note:
The system displays a warning message that disabling the deny list protection is not recommended for security reasons.
To view the effectiveness and statistics for the Global Deny Lists feature, run the following command:
stat denylist global
To disable the Global Deny Lists feature using the GUI:
-
Navigate to Configurations > System > Settings > Change Global System Settings.
-
In the Change Global System Settings page, clear the checkbox.