Custom keyword support for HTML payload
Starting from NetScaler release 13.1 build 27.xx, you can add keywords of your choice and check if these configured keywords are present in the HTML payload.
SQL injection and command injection have a predefined set of keywords or patterns that they look for in the incoming requests. These predefined sets of keywords might not cover all the keywords as per your requirement and might lead to an increase in the number of false positives. With this feature, you can add keywords that are not covered in the SQL injection and command injection checks and therefore reduce the false positives.
After adding the keywords, you can configure the NetScaler appliance to check if the added keywords are detected in the incoming requests. You can then configure the NetScaler appliance to do one of the following actions:
- None – No action is taken. This action is the default.
- Log - Log all requests that match the URL and have the configured keywords.
- Block – Block all requests that match the URL and have the configured keywords.
- Stats – Increment the log counter for each request that matches the URL and has the configured keywords.
Add custom keywords using the CLI
Adding a custom keyword using the CLI involves the following steps:
-
Configure a web application firewall profile and define an action when the custom keyword is detected in the incoming request.
set appfw profile <profile-name> –blockKeywordAction (block | log | stats | none) <!--NeedCopy-->By default, the -blockKeywordAction is set to none.
Example:
set appfw profile test_profile -blockKeywordAction none <!--NeedCopy--> -
Bind the web application firewall profile with your custom keywords.
bind appfw profile <profile_name> -blockKeyword <keyword_name> -BlockKeywordType <literal|PCRE > -fieldName <field_name> -formURL <URL> -isFieldNameRegex <REGEX|NOTREGEX> -state <enable/disable> -comment <text> <!--NeedCopy-->Example:
To add blockword as the custom keyword and bind it to test_profile, run the following command:
bind appfw profile test_profile -blockKeyword "blockword" BlockKeywordType literal -fieldName "firstname" -formURL "/signup.php" -state enable <!--NeedCopy-->Note:
You can enter an URL or an FQDN in the URL parameter. The FQDN supports both HTTP and HTTPS protocol.
Add custom keywords using the GUI
- Navigate to Security > NetScaler Web App Firewall Profile > Profiles.
- Select a profile and click Edit.
- Go to the Advanced Settings section and click Deny Rules.
- Select Block Keyword and click Edit.
- Click Add and set the following parameters:
- Enable
- Block Keyword
- Block Keyword Type
- Field Name
- URL
- Is Regex
- Comments
- Resource ID
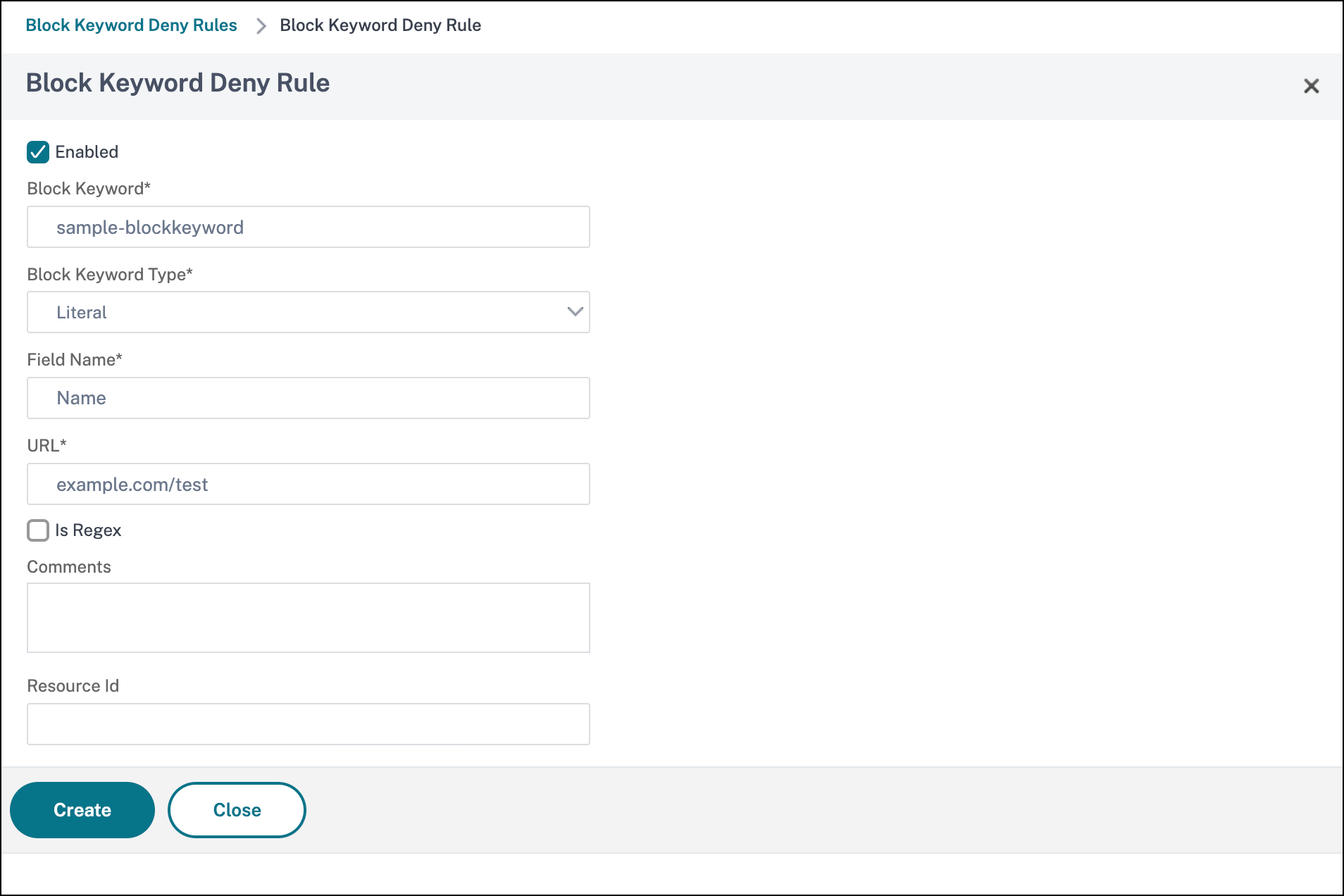
- Click Create. The custom keyword that you added is listed in the Block Keyword Deny Rules page.
- Go to the Advanced Settings section and click Security Checks.
- Select Block Keyword and click Action Settings.
- Select the required actions and click OK.
View custom keyword statistics using the CLI
To view the custom keyword statistics, type the following command at the command prompt:
stat appfw profile <profile name>
<!--NeedCopy-->
Example
stat appfw profile test_profile
<!--NeedCopy-->
View custom keyword statistics the GUI
-
Navigate to Security > NetScaler Web App Firewall > Profiles.
-
In the details pane, select a Web App Firewall profile and click Statistics. The NetScaler Web App Firewall Statistics page displays the custom keyword traffic and violation details.
-
You can select Tabular View or switch to Graphical View to display the data in a tabular or graphical format.