-
Install and configure the NetScaler Gateway appliance
-
Maintain and monitor NetScaler Gateway systems
-
Configure DTLS VPN virtual server using SSL VPN virtual server
-
Integrate NetScaler Gateway with Citrix products
-
Integrate NetScaler Gateway with Citrix Virtual Apps and Desktops™
-
Configure settings for your Citrix Endpoint Management Environment
-
Configure load balancing servers for Citrix Endpoint Management
-
Configure load balancing servers for Microsoft Exchange with Email Security Filtering
-
Configure Citrix Endpoint Management NetScaler Connector (XNC) ActiveSync Filtering
-
Allow Access from mobile devices with Citrix Mobile Productivity Apps
-
Configure domain and security token authentication for Citrix Endpoint Management
-
Configure client certificate or client certificate and domain authentication
-
-
NetScaler Gateway Enabled PCoIP Proxy Support for VMware Horizon View
-
Proxy Auto Configuration for Outbound Proxy support for NetScaler Gateway
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
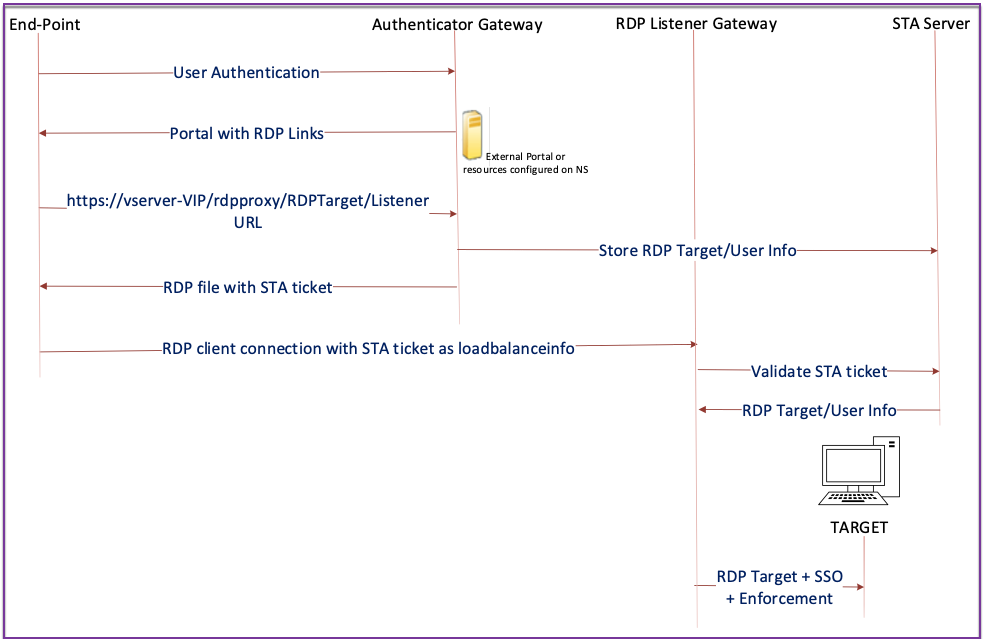
Stateless RDP Proxy
The Stateless RDP Proxy accesses an RDP host. Access is granted through the RDPListener on NetScaler Gateway when the user authenticates on a separate NetScaler Gateway Authenticator. The information required by the RDPListener for NetScaler Gateway is securely stored on a STA server. A STA server can be placed anywhere as long as the NetScaler Gateway and application enumeration servers can reach it. For details see, https://support.citrix.com/article/CTX101997.
Connection flow
There are two connections involved in the RDP Proxy flow. The first connection is the user’s SSL VPN connection to the NetScaler Gateway VIP, and enumeration of the RDP resources.
The second connection is the native RDP client connection to the RDP listener (configured using rdpIP and rdpPort) on the NetScaler Gateway, and subsequent proxying of the RDP client to server packets securely.
-
The User connects to the Authenticator Gateway VIP and provides the credentials.
-
After successful login to the gateway, the user is redirected to the homepage/external portal which enumerates the remote desktop resources that the user can access.
-
Once the user selects an RDP resource, a request is received by the Authenticator Gateway VIP, in the format
https://AGVIP/rdpproxy/ip:port/rdptargetproxyindicating the published resource that the user clicked. This request has the information about the IP and port of the RDP server that the user has selected. -
The authenticator gateway processes the /rdpproxy/ request. Because the user is already authenticated, this request comes with a valid gateway cookie.
-
The
RDPTargetandRDPUserinformation is stored on the STA server and a STA Ticket is generated. The information is stored as an XML blob which is optionally encrypted using the configured pre-shared key. If encrypted, the blob is base64 encoded and stored. The Authenticator Gateway uses one of the STA servers that is configured on the Gateway virtual server. -
The XML blob is in the following format
<Value name=”IPAddress”>ipaddr</Value>\n<Value name=”Port”>port</Value\>n <Value name=”`Username`”>username</Value\>\n<Value name=”Password”>pwd\</Value\> <!--NeedCopy--> -
The
rdptargetproxyobtained in the /rdpproxy/ request is put as the ‘fulladdress’ and the STA ticket (pre-pended with the STA AuthID) is put as theloadbalanceinfoin the.rdp file. -
The
.rdpfile is sent back to the client end-point. -
The native RDP client launches and connects to the
RDPListener Gateway. It sends the STA ticket in the initial x.224 packet. -
The
RDPListener Gatewayvalidates the STA ticket and obtains theRDPTargetandRDPUserinformation. The STA server to be used is retrieved using the ‘AuthID’ present in theloadbalanceinfo. -
A Gateway session is created for storing authorization/auditing policies. If a session exists for the user, it is reused.
-
The
RDPListener Gatewayconnects to theRDPTargetand single signs on using CREDSSP.
Prerequisites
-
User is authenticated on the NetScaler Gateway authenticator.
-
The initial /rdpproxy URL and RDP Client are connected to a different
RDPListener NetScaler Gateway. -
The Authenticator Gateway using a STA Server securely passes the
RDPListener Gatewayinformation.
Configure stateless RDP Proxy by using the CLI
-
Add a
rdpServerprofile. The server profile is configured on theRDPListener Gateway.Note:
- Once the rdpServer Profile is configured on the VPN virtual server, it cannot be modified. Also, the same serverProfile cannot be reused on another VPN virtual server.
add rdpServer Profile [profilename] -rdpIP [IPV4 address of the RDP listener] -rdpPort [port for terminating RDP client connections] -psk [key to decrypt RDPTarget/RDPUser information, needed while using STA]. <!--NeedCopy-->Configure the RDP server profile on the VPN virtual server using the following command:
add vpn vserver v1 SSL [publicIP] [portforterminatingvpnconnections] -rdpServerProfile [rdpServer Profile] <!--NeedCopy-->Example
add vpn vserver v1 SSL 1.1.1.1 443 -rdpServerProfile rdp_server_prof <!--NeedCopy-->Important:
-
The same STA server must be bound to both RDP authenticator gateway and listener gateway.
-
For stateless RDP proxy, the STA Server validates the STA ticket that is sent by the RDP client to obtain the RDP Target server and RDP user’s information. You must bind the STA server in addition to the VPN virtual server. In the following example, the RDP target server is 1.1.1.0 and the RDP listener gateway virtual server 1.1.1.2.
add vpn url url4 RDP2 "rdp://1.1.1.0/1.1.1.2:443" <!--NeedCopy-->
Configure the client profile on the authenticator Gateway using the following command:
add rdpClient profile <name> -rdpHost <optional FQDN that will be put in the RDP file as ‘fulladdress’> [-rdpUrlOverride ( ENABLE | DISABLE )] [-redirectClipboard ( ENABLE | DISABLE )] [-redirectDrives ( ENABLE | DISABLE )]
[-redirectPrinters ( ENABLE | DISABLE )] [-keyboardHook <keyboardHook>] [-audioCaptureMode ( ENABLE | DISABLE )] [-videoPlaybackMode ( ENABLE | DISABLE )]
[-rdpCookieValidity <positive_integer>][-multiMonitorSupport ( ENABLE | DISABLE )] [-rdpCustomParams <string>]
<!--NeedCopy-->
The –rdpHost configuration is used in a single Gateway deployment. Only psk is a mandatory argument and it must be the same PSK that is added in the RDP server profile in the RDP listener gateway.
- Associate the RDP Profile with the VPN virtual server.
You can associate an RDP profile either by configuring a sessionAction+sessionPolicy or by setting the global VPN parameter.
Example:
add vpn sessionaction <actname> -rdpClientprofile <rdpprofilename>
add vpn sessionpolicy <polname> NS_TRUE <actname>
bind vpn vserver <vservername> -policy <polname> -priority <prioritynumber>
<!--NeedCopy-->
OR
set vpn parameter –rdpClientprofile <name>
<!--NeedCopy-->
Configure stateless RDP proxy by using the GUI
The following high-level steps are involved in the stateless RDP proxy configuration. For the detailed steps, see RDP Proxy configuration.
- Create an RDP server profile
- Create an RDP client profile
- Create a virtual server
- Create a bookmark
- Create or edit a session profile or policy
- Bind a bookmark
Important:
For stateless RDP proxy, you must bind a STA server in addition to the VPN virtual server.
Connection counter
A new connection counter ns_rdp_tot_curr_active_conn was added, which keeps the record of the number of active connections in use. It can be viewed as a part of the nsconmsg command on the NetScaler shell. CLI command to view these counters is planned to be added later.
Upgrade notes
The rdpIP and rdpPort, which were previously configured on the VPN virtual server is part of the rdpServerProfile. The rdp Profile is renamed as rdp ClientProfile and the parameter clientSSL is removed. Therefore, the earlier configuration does not work.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.