Ease of troubleshooting with Web Application Firewall logs
When there is a security attack, it is important to capture detailed WAF logging on the appliance. For this, you can configure the “VerboseLogLevel” parameter on an Application Firewall profile.
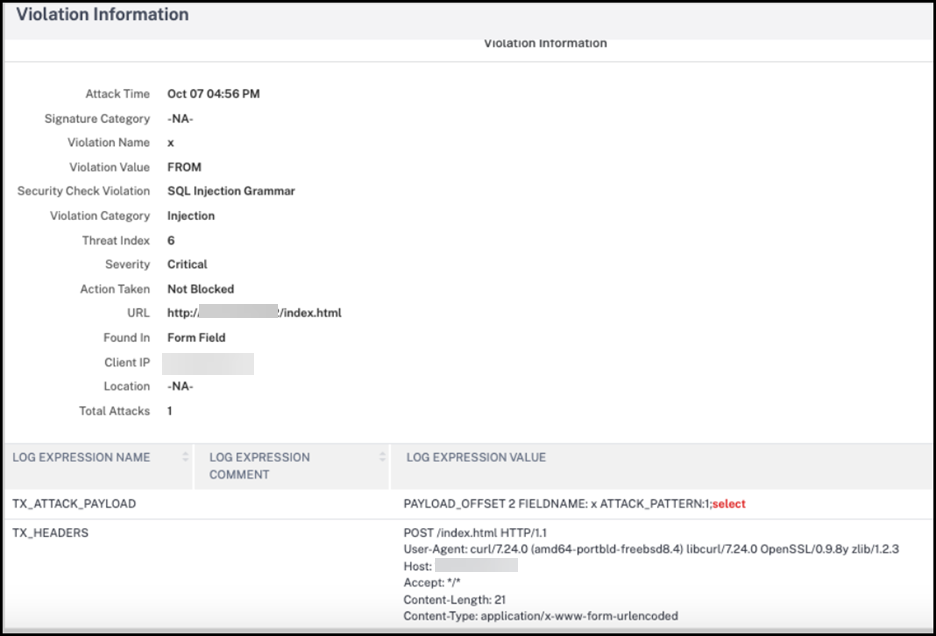
Consider a web traffic having a security attack. When the appliance receives the traffic, violation details such as HTTP header details, log pattern, and pattern payload information are logged and sent to the ADM server. The ADM server monitors the detailed logs and displays it on the Security Insight page for monitoring and tracking purpose.
Note:
To maximize the benefits of the verbose logging functionality, enable the
Enable Extend Loggingoption from NetScaler console. For more informaton on enabling the option, see View application security violation details.
Configuring verbose log level by using the command interface
To capture detailed WAF logs, configure the following command. At the command interface, type:
set appfw profile <profile_name> -VerboseLogLevel (pattern|patternPayload|patternPayloadHeader)
Example
set appfw profile profile1 –VerboseLogLevel patternPayloadHeader
The available log levels are:
- Pattern. Logs only violation pattern.
- Pattern payload. Logs violation pattern and 150 bytes of extra field element payload.
- Pattern payload header. Logs violation patter, 150 bytes of extra field element payload and HTTP header information.
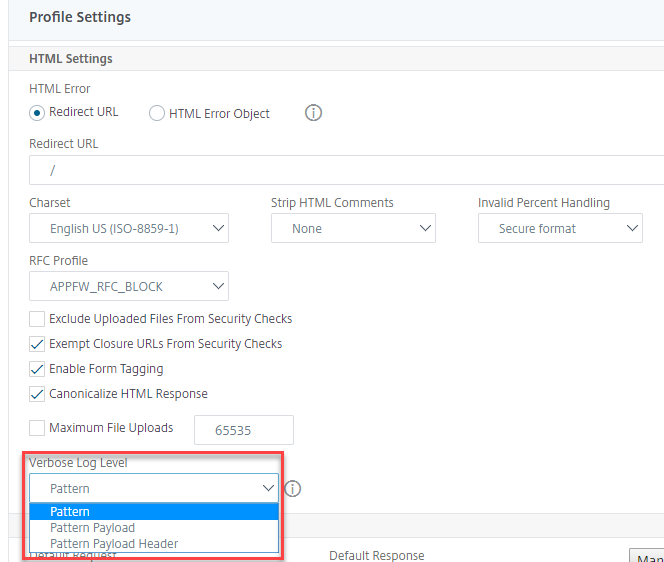
Configuring verbose log level by using the NetScaler GUI
Complete the following procedure to configure the verbose log level in the WAF profile.
- On the navigation pane, navigate to Security > Profiles.
- In the Profiles page, click Add.
- In the NetScaler Web App Firewall Profile page, click Profile Settings under Advanced Settings.
- In the Profile Settings section, select the detailed WAF log level in the Verbose Log Level field.
-
Click OK and Done.
Verbose logging for JSON security checks (SQL, CMD, and cross-site scripting)
When an incoming request type is of JSON, you can configure the verbose log level parameter to capture detailed violation logs such as pattern, pattern payload, and HTTP header information. The log details are then sent to the NetScaler Console server for monitoring and troubleshooting JSON violations. The verbose log message is not stored in the ns.log file. Verbose logging for JSON content type security protection can be configured for the following violation types:
- SQL Injection
- Cross-site scripting
- Command Injection
Configure verbose logging for JSON security protection by using the CLI
To capture detailed HTTP header information as logs, you can configure the verbose logging parameter in the Web App Firewall profile. At the command prompt, type:
set appfw profile <profile_name> -VerboseLogLevel ( pattern | patternPayload | patternPayloadHeader )
<!--NeedCopy-->
Example:
set appfw profile profile1 -VerboseLogLevel patternPayloadHeader
The available log levels are:
Pattern. Logs only violation pattern.
Pattern payload. Logs violation pattern and 150 bytes of extra JSON payload.
Pattern payload header. Logs violation patter, 150 bytes of extra JSON payload and HTTP header information.
Configuring verbose log level by using the NetScaler GUI
Follow the procedure below to configure the verbose log level for JSON security protection.
- On the navigation pane, navigate to Security > Profiles.
- In the Profiles page, click Add.
- In the NetScaler Web App Firewall Profile page, click Security Checks under Advanced Settings.
- In the Security Checks section, select JSON and click Action Settings.
- In the JSON Security Settings page, set the Verbose log level parameter.
- Click OK and Done.
Based on the details captured by NetScaler WAF JSON verbose logging, the following violation details can be inspected on the NetScaler Console server.