Configure firewall segmentation
Virtual Route Forwarding (VRF) firewall segmentation provides multiple routing domains accesses to the internet through a common interface, with each domain’s traffic isolated from that of the others. For example, employees and guests can access the internet through the same interface, without any access to each other’s traffic.
- Local guest-user Internet access
- Employee-user Internet access for defined applications
- Employee-users may continue hairpin all other traffic to the MCN
- Allow the user to add specific routes for specific routing domains.
- When enabled, this feature applies to all routing domains.
You can also create multiple access interfaces to accommodate separate public facing IP addresses. Either option provides the required security necessary for each user group.
Enabling Internet Access on Routing Domain(s)
You can enable Internet access on a routing domain through Citrix SD-WAN Orchestrator service. This option auto-creates a DEFAULT route (0.0.0.0/0) on all the routing tables of the respective routing domains. You can enable Internet access for all the routing domains, or none. It avoids the need for creating exclusive static route across all the routing domains if the Internet access is required.
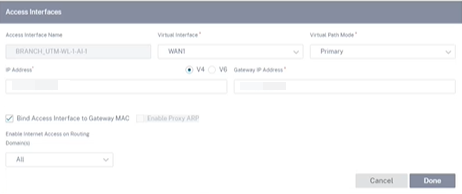
For more information, see Access interface.
Use Cases
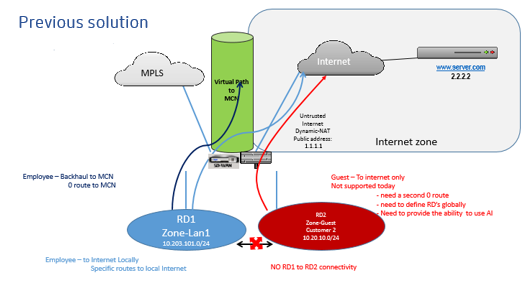
The following are the supported use cases for firewall segmentation:
- Customers have multiple routing domains at a branch site without the requirement to include all domains at the data center (MCN). They need the ability to isolate different customers’ traffic in a secure manner
- Customers must be able to have a single accessible firewalled Public IP address for multiple routing domains to access the internet at a site (extend beyond VRF lite).
- Customers need an Internet route for each routing domain supporting different services.
- Multiple routing domains at a branch site.
- Internet Access for different routing domains.
Multiple routing domains at a branch site
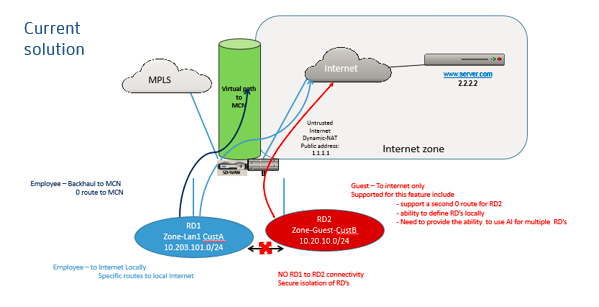
With the Virtual Forwarding and Routing Firewall segmentation enhancements, you can:
- Provide an infrastructure, at the branch site, that supports secure connectivity for at least two user groups, such as employees and guests. The infrastructure can support up to 254 routing domains.
- Isolate each routing domain’s traffic from the traffic of any other routing domain.
-
Provide Internet access for each routing domain,
-
A common Access Interface is required and acceptable
-
An Access Interface for each group with separate Public facing IP addresses
-
- Traffic for the employee can be routed directly out to the local internet (specific applications)
- Traffic for the employee can be routed or backhauled to the MCN for extensive filtering (0 route)
- Traffic for the routing domain can be routed directly out to the local internet (0 route)
- Supports specific routes per routing domain, if necessary
- Routing domains are VLAN based
- Removes the requirement for the RD to have to reside at the MCN
- Routing Domain can now be configured at a branch site only
- Allows you to assign multiple RD to an access interface (once enabled)
- Each RD is assigned a 0.0.0.0 route
- Allows specific routes to be added for an RD
- Allows traffic from different RD to exit to the internet using the same access interface
- Allows you to configure a different access interface for each RD
- Must be unique subnets (RD are assigned to a VLAN)
- Each RD can use the same FW default Zone
- The traffic is isolated through the Routing Domain
- Outbound flows have the RD as a component of the flow header. Allows SD-WAN to map return flows to correct Routing domain.
Prerequisites to configure multiple routing domains:
- Internet access is configured and assigned to a WAN Link.
- Firewall configured for NAT and correct policies applied.
- Second routing domain added globally.
- Each routing domain added to a site.
- For information about configuring Internet services on the routing domains, see WAN links.
Deployment scenarios
Limitations
-
The internet service must be added to the WAN link before you can enable Internet access for all Routing Domains. (Until you do, the check box for enabling this option is grayed out).
After enabling Internet access for all routing domains, auto add a dynamic-NAT rule.
- Access Interface (AI): Single AI per subnet.
- Multiple AIs require a separate VLAN for each AI.
-
If you have two routing domains at a site and have a single WAN Link, both domains use the same public IP address.
-
If Internet access for all routing domains is enabled, all sites can route to Internet. (If one routing domain does not require internet access, you can use the firewall to block its traffic.)
- The WAN links are shared for Internet access.
- No QOS per routing domain; first come first serve.