-
-
-
Add LDAP authentication servers
-
View recommendations and manage your ADCs and applications efficiently
-
-
Use ADM log messages for managing and monitoring your infrastructure
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Add LDAP authentication server
When you integrate LDAP protocol with RADIUS and TACAS authentication servers, you can use ADM to search and authenticate user credentials from distributed directories.
-
Navigate to Settings > Authentication.
-
Select the LDAP tab and then click Add.
-
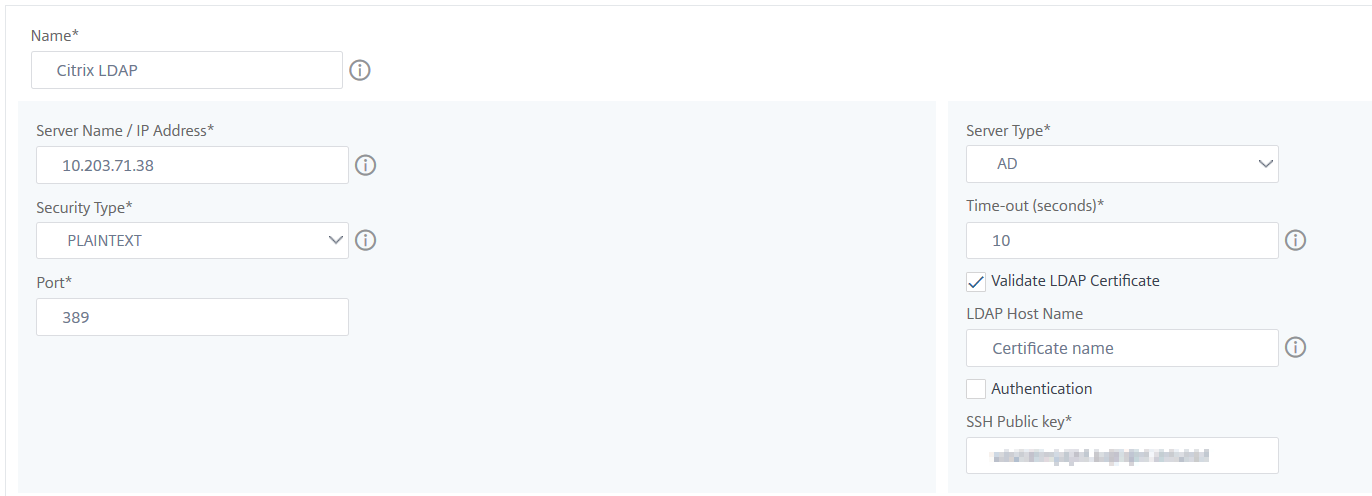
On the Create LDAP Server page, specify the following parameters:
-
Name – Specify the LDAP server name
-
Server Name/IP address – Specify the LDAP IP address or server name
-
Security Type – Type of communication required between the system and the LDAP server. Select from the list. If plain text communication is inadequate, you can choose encrypted communication by selecting either Transport Layer Security (TLS) or SSL
-
Port – By default, port 389 is used for PLAINTEXT. You can also specify port 636 for SSL/TLS
-
Server Type – Select Active Directory (AD) or Novell Directory Service (NDS) as the type of LDAP server
-
Time-out (seconds) – Time in seconds for which the NetScaler® ADM system waits for a response from the LDAP server
-
LDAP Host Name – Select Validate LDAP Certificate check box and specifying the host name to be entered on the certificate
Clear the Authentication option and specify the SSH Public Key. With key-based authentication, you can now fetch the list of public keys that are stored on the user object in LDAP server through SSH.
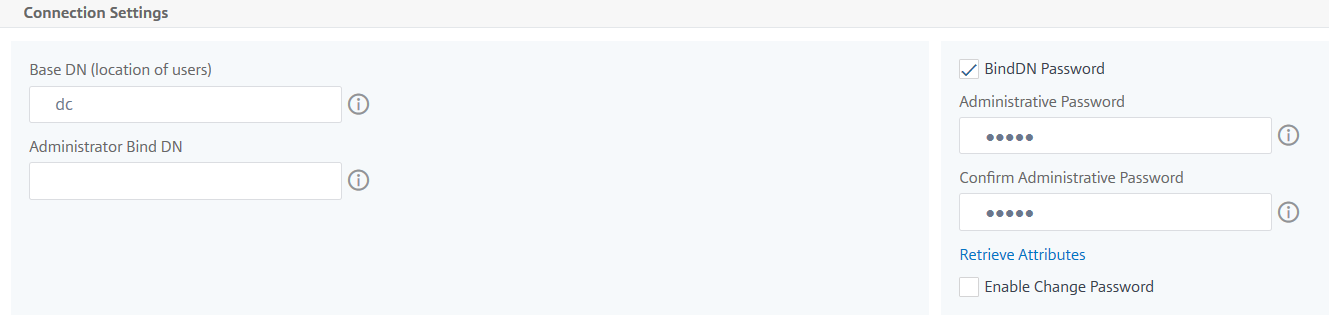
Under Connection Settings, specify the following parameters:
-
Base DN – The base node for LDAP server to start the search
-
Administrator Bind DN – User name to it bind to LDAP server. For example, admin@aaa.local.
-
Bind DN password – Select this option to provide a password for authentication
-
Enable Change Password – Select this option to enable password change
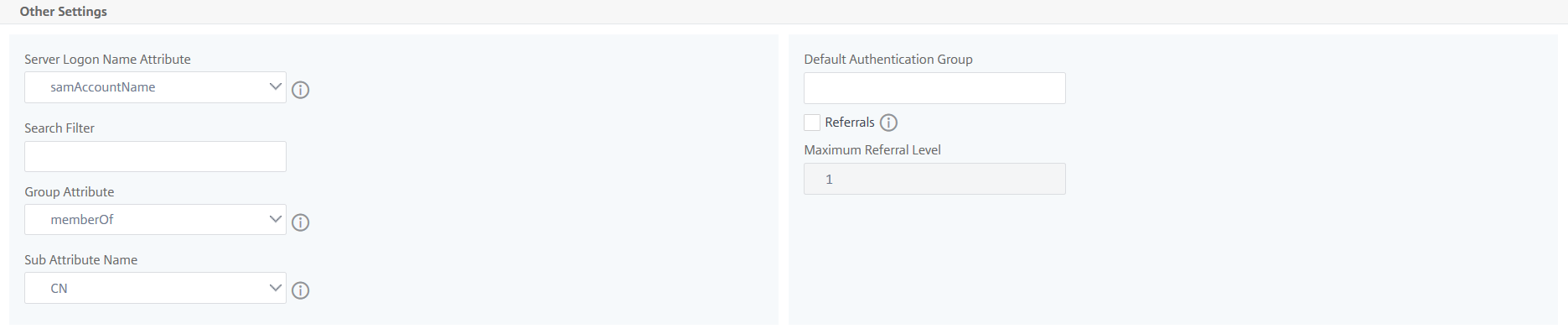
Under Other Settings, specify the following parameters
-
Server Log on Name Attribute – Name attribute used by the system to query the external LDAP server or an Active Directory. Select samAccountname from the list.
-
Search Filter – Configure external users for two-factor authentication according to the search filter configured in LDAP server. For example, vpnallowed=true with ldaploginame
samaccountand the user-supplied user name bob would yield an LDAP search string of:&(vpnallowed=true)(samaccount=bob).Note
By default, the values in the search filter are enclosed in brackets.
-
Group Attribute – Select memberOf from the list.
-
Sub Attribute Name – The Sub attribute name for group extraction from the LDAP server.
-
Default Authentication Group – Default group to choose when the authentication succeeds in addition to extracted groups.
-
-
-
Click Create.
The LDAP server is now configured.
Note:
If the users are Active Directory group members, the group and the users’ names on NetScaler ADM must have the same names of Active Directory group members.
-
Enable the external authentication servers.
For more information about enabling external authentication servers, see Enable external authentication servers and fallback options.
Share
Share
In this article
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.