-
Getting Started with Citrix ADC
-
Deploy a Citrix ADC VPX instance
-
Install a Citrix ADC VPX instance on Microsoft Hyper-V servers
-
Install a Citrix ADC VPX instance on Linux-KVM platform
-
Prerequisites for Installing Citrix ADC VPX Virtual Appliances on Linux-KVM Platform
-
Provisioning the Citrix ADC Virtual Appliance by using OpenStack
-
Provisioning the Citrix ADC Virtual Appliance by using the Virtual Machine Manager
-
Configuring Citrix ADC Virtual Appliances to Use SR-IOV Network Interface
-
Configuring Citrix ADC Virtual Appliances to use PCI Passthrough Network Interface
-
Provisioning the Citrix ADC Virtual Appliance by using the virsh Program
-
Provisioning the Citrix ADC Virtual Appliance with SR-IOV, on OpenStack
-
Configuring a Citrix ADC VPX Instance on KVM to Use OVS DPDK-Based Host Interfaces
-
-
Deploy a Citrix ADC VPX instance on Microsoft Azure
-
Network architecture for Citrix ADC VPX instances on Microsoft Azure
-
Configure multiple IP addresses for a Citrix ADC VPX standalone instance
-
Configure a high-availability setup with multiple IP addresses and NICs
-
Configure a high-availability setup with multiple IP addresses and NICs by using PowerShell commands
-
Configure HA-INC nodes by using the Citrix high availability template with Azure ILB
-
Configure address pools (IIP) for a Citrix Gateway appliance
-
-
Deploy a Citrix ADC VPX instance on Google Cloud Platform
-
Upgrade and downgrade a Citrix ADC appliance
-
Solutions for Telecom Service Providers
-
Load Balance Control-Plane Traffic that is based on Diameter, SIP, and SMPP Protocols
-
Provide Subscriber Load Distribution Using GSLB Across Core-Networks of a Telecom Service Provider
-
Authentication, authorization, and auditing application traffic
-
Configuring authentication, authorization, and auditing policies
-
Configuring Authentication, authorization, and auditing with commonly used protocols
-
Use an on-premises Citrix Gateway as the identity provider for Citrix Cloud™
-
Troubleshoot authentication issues in Citrix ADC and Citrix Gateway with aaad.debug module
-
-
-
-
-
-
Persistence and persistent connections
-
Advanced load balancing settings
-
Gradually stepping up the load on a new service with virtual server–level slow start
-
Protect applications on protected servers against traffic surges
-
Retrieve location details from user IP address using geolocation database
-
Use source IP address of the client when connecting to the server
-
Use client source IP address for backend communication in a v4-v6 load balancing configuration
-
Set a limit on number of requests per connection to the server
-
Configure automatic state transition based on percentage health of bound services
-
-
Use case 2: Configure rule based persistence based on a name-value pair in a TCP byte stream
-
Use case 3: Configure load balancing in direct server return mode
-
Use case 6: Configure load balancing in DSR mode for IPv6 networks by using the TOS field
-
Use case 7: Configure load balancing in DSR mode by using IP Over IP
-
Use case 10: Load balancing of intrusion detection system servers
-
Use case 11: Isolating network traffic using listen policies
-
Use case 12: Configure Citrix Virtual Desktops for load balancing
-
Use case 13: Configure Citrix Virtual Apps™ for load balancing
-
Use case 14: ShareFile wizard for load balancing Citrix ShareFile
-
-
-
-
-
Authentication and authorization
-
-
Configuring a CloudBridge Connector Tunnel between two Datacenters
-
Configuring CloudBridge Connector between Datacenter and AWS Cloud
-
Configuring a CloudBridge Connector Tunnel Between a Datacenter and Azure Cloud
-
Configuring CloudBridge Connector Tunnel between Datacenter and SoftLayer Enterprise Cloud
-
Configuring a CloudBridge Connector Tunnel Between a Citrix ADC Appliance and Cisco IOS Device
-
CloudBridge Connector Tunnel Diagnostics and Troubleshooting
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Deploy a Citrix® ADC VPX instance on Google Cloud Platform
You can deploy a Citrix ADC VPX instance on Google Cloud Platform (GCP). A VPX instance in GCP enables you to take advantage of GCP cloud computing capabilities and use Citrix load balancing and traffic management features for your business needs. You can deploy VPX instances in GCP as standalone instances. Both single NIC and multi NIC configurations are supported.
Note: VPX high availability deployment is not yet supported on GCP.
Supported features
A VPX instance running in GCP supports the following features:
- Load Balancing
- ICA® Proxy
- Content Switching
- AAA
- Rewrite
- Responder
- RDP Proxy
- nFactor
- LDAP
- VPN (CVPN/Full)
- GSLB
Limitation
- IPv6 is not supported
Hardware requirements
VPX instance in GCP must have minimum of 2 vCPUs and 4 GB RAM.
Prerequisites
-
Install the “gcloud” utility on your device. You can find the utility at this link: https://cloud.google.com/sdk/install
-
Download the NSVPX-GCP image from the Citrix download site.
-
Upload the file(for example, NSVPX-GCP-12.1-50.9_nc_64.tar.gz) to a storage bucket on Google by following the steps given at https://cloud.google.com/storage/docs/uploading-objects.
-
Run the following command on the gcloud utility to create an image.
gcloud compute images create <IMAGE_NAME> --source-uri=gs://<STORAGE_BUCKET_NAME>/<FILE_NAME>.tar.gz --guest-os-features=MULTI_IP_SUBNET
<!--NeedCopy-->
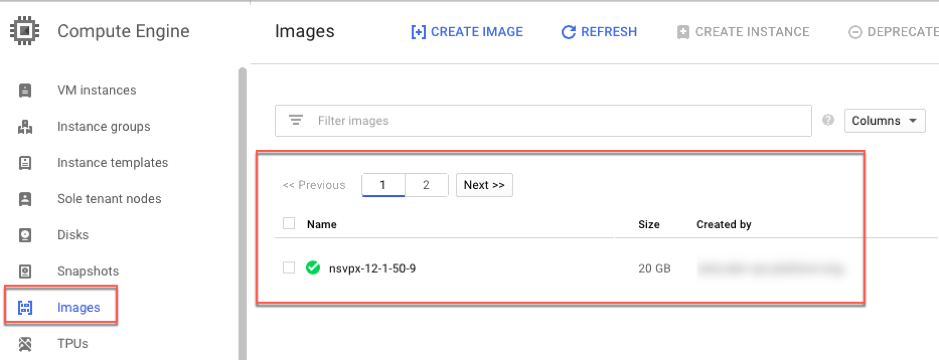
It might take a moment for the image to be created. After the image is created, it appears under Compute > Compute Engine in the GCP console.
Points to note
Consider the following GCP-specific points before you begin your deployment.
- After creating the instance, you cannot add or remove any network interfaces.
- For a multi-NIC deployment, create separate VPC networks for each NIC. One NIC can be associated with only one network.
- For a single-NIC instance the GCP console creates a network by default.
- Minimum 4 VPCUs are required for an instance with more than two network interfaces.
- If IP forwarding is required, you must enable IP forwarding while creating the instance and configuring the NIC.
Scenario: deploy a multi-NIC, multi-IP standalone VPX instance
This scenario illustrates how to deploy a Citrix VPX standalone instance in GCP. In this scenario, you create a standalone VPX instance with multiple NICs. The instance communicates with back-end servers (the server farm).
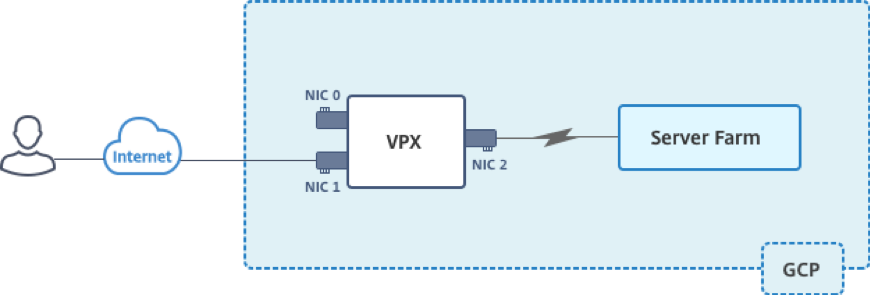
Create three NICs to serve the following purposes.
| NIC | Purpose | Associated with VPC network |
|---|---|---|
| NIC 0 | Serves management traffic (Citrix ADC IP) | Management network |
| NIC 1 | Serves client-side traffic (VIP) | Client network |
| NIC 2 | Communicates with back-end servers (SNIP) | Back-end server network |
Also, set up the required communication routes between the instance and the back-end servers, and between the instance and the external hosts on the public internet.
Summary of deployment steps
- Create three VPC networks for three different NICs.
- Create firewall rules for ports 22, 80, and 443
- Create an instance with three NICs
Note: Create instance in the same region where you’ve created the VPC networks.
Create VPC Networks
Create three VPC networks that will be associated with management NIC, client NIC, and server NIC. To create a VPC network, log on the Google console > Networking > VPC network > Create VPC Network. Complete the required fields, as shown in the screen capture, and click Create.
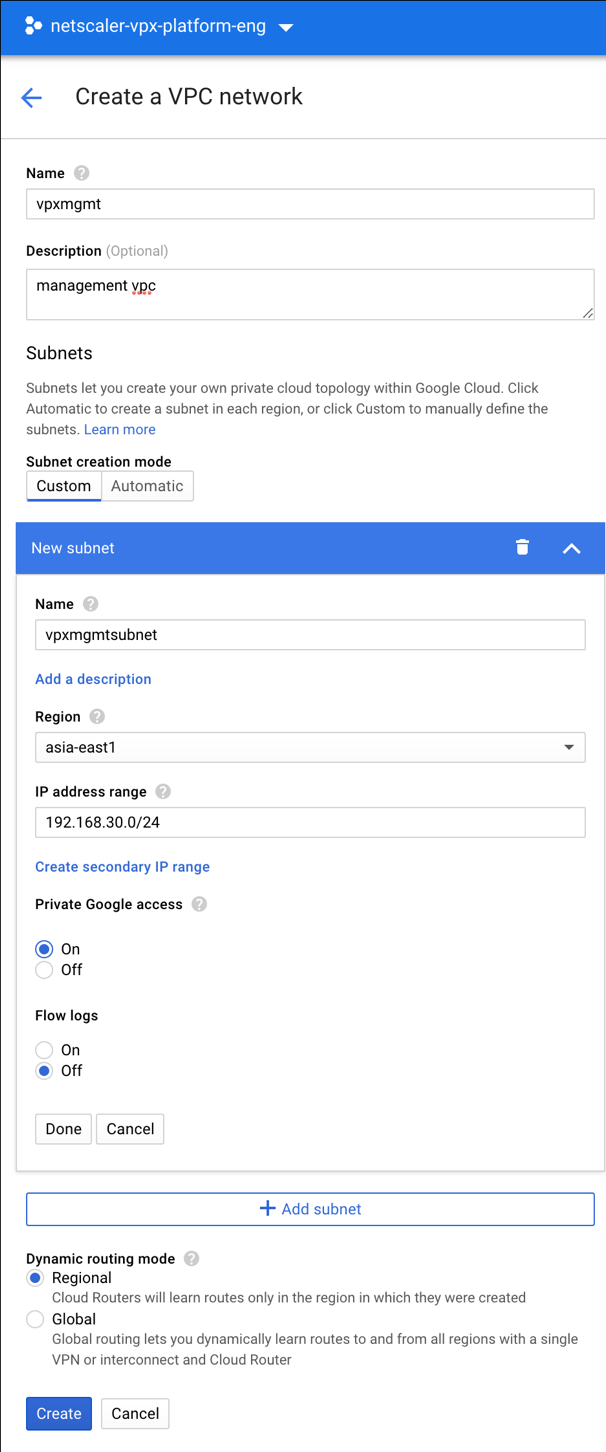
Similarly, create VPC networks for client and server-side NICs.
Note: All three VPC networks should be in the same region, which is asia-east1 in this scenario.
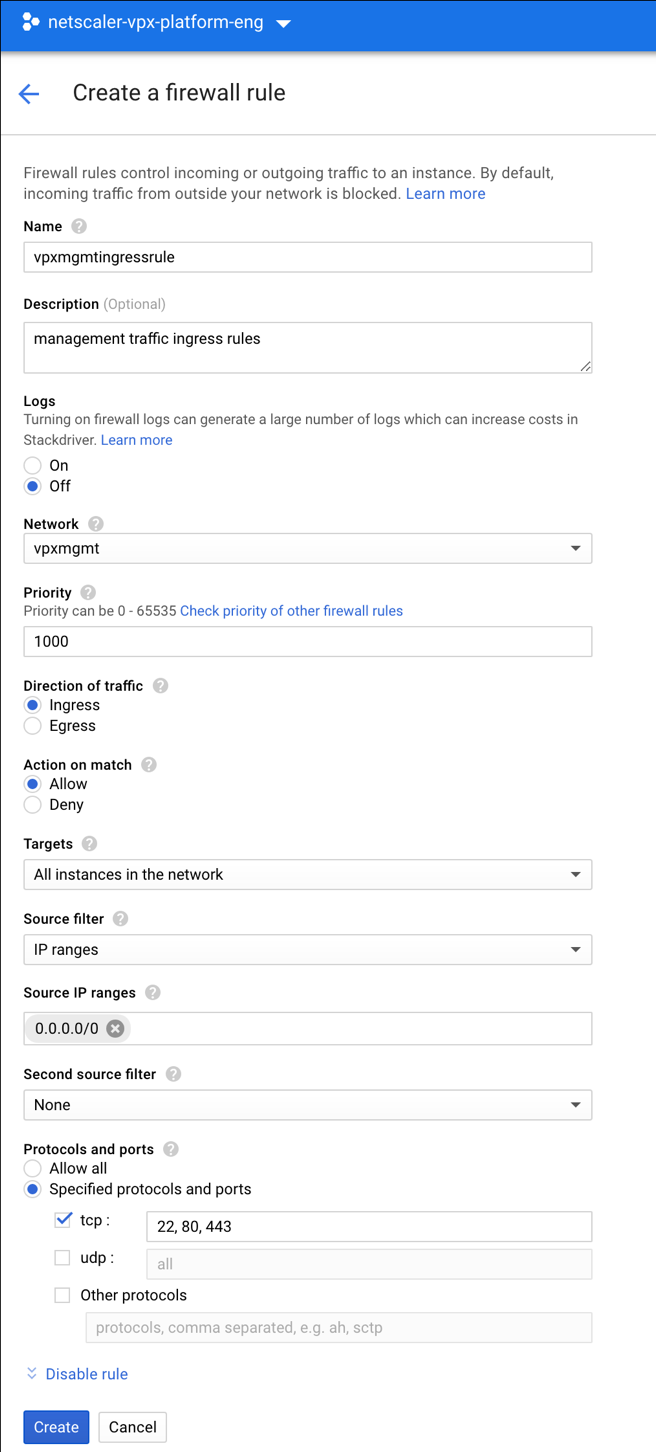
Create firewall rules for ports 22, 80, and 443
Create rules for SSH (port 22), HTTP (port 80), and HTTPS (port 443) for each VPC networks. For more information about firewall rules, see Firewall Rules Overview.
Create the VPX instance
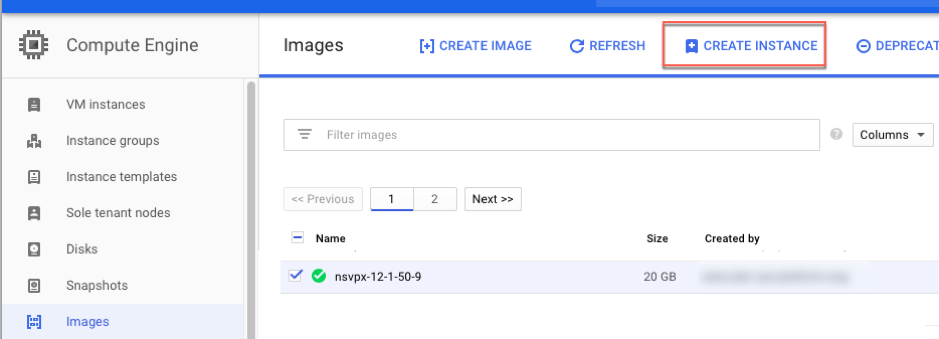
- Log on to the GCP console.
- Under Compute, hover over Compute Engine, and select Images.
-
Select the image, and click Create Instance.
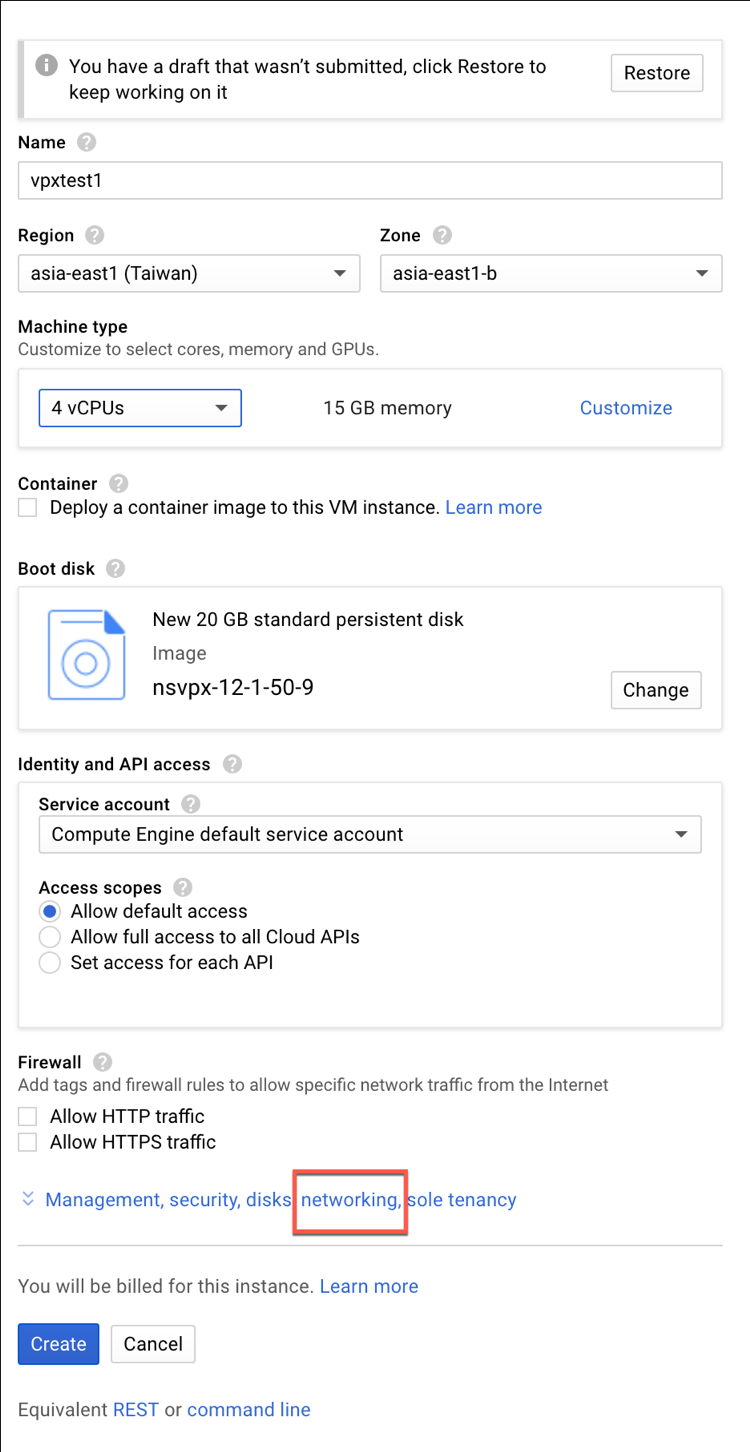
- Select an instance with 4 VPCUs, to support multiple NICs.
-
Click the networking option from Management, security, disks, networking, sole tenancy to add the additional NICs.
Note: Container image is not supported on VPX instances on GCP.
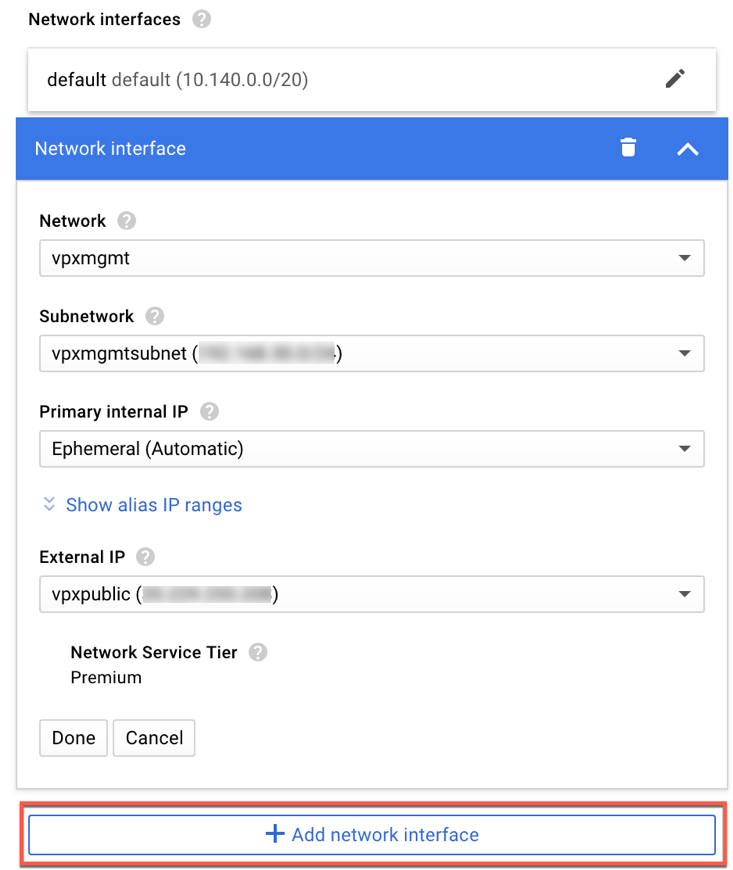
- Under Networking interfaces, click the edit icon to edit the default NIC. This NIC is the management NIC.
-
In the Network interfaces window, under Network, select the VPC network you created for management NIC.
-
For the management NIC, create a static external IP address. Under the External IP list, click Create IP address.
-
In the Reserve a new static IP address window, add a name and description and click Reserve.
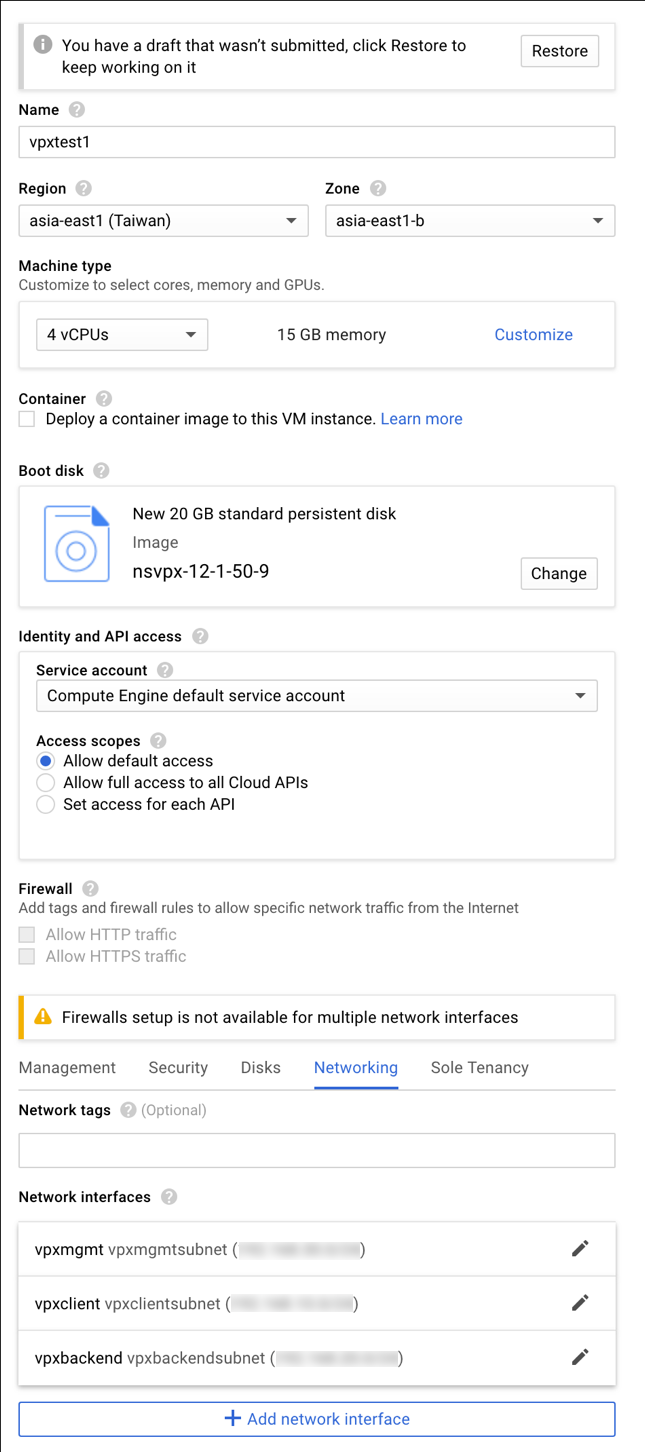
- Click Add network interface to create NICs for client and server-side traffic.
After you’ve created all the NICs, click Create to create the VPX instance.
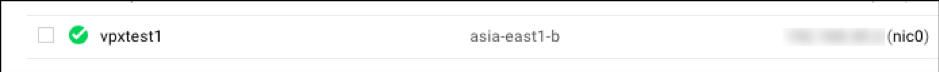
The instance appears under VM instances.
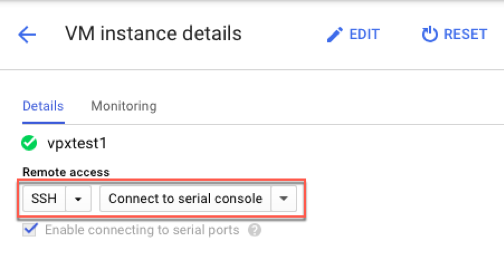
Use the GCP SSH or the serial console to configure and manage the VPX instance.
Points to note after you’ve deployed the VPX instance on GCP.
-
Log on to the VPX with user name
nsrootand instance ID as password. -
After first logon, change the default password.
-
For collecting tech support bundle, run the command shell /netscaler/showtech_cloud.pl instead of the customary show techsupport.
GDM templates to deploy a Citrix ADC VPX instance
You can use a Citrix ADC VPX Google Deployment Manager (GDM) template to deploy a VPX instance on GCP. For details, see Citrix ADC GDM Templates.
Resources
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.