-
Getting Started with Citrix ADC
-
Deploy a Citrix ADC VPX instance
-
Install a Citrix ADC VPX instance on Microsoft Hyper-V servers
-
Install a Citrix ADC VPX instance on Linux-KVM platform
-
Prerequisites for Installing Citrix ADC VPX Virtual Appliances on Linux-KVM Platform
-
Provisioning the Citrix ADC Virtual Appliance by using OpenStack
-
Provisioning the Citrix ADC Virtual Appliance by using the Virtual Machine Manager
-
Configuring Citrix ADC Virtual Appliances to Use SR-IOV Network Interface
-
Configuring Citrix ADC Virtual Appliances to use PCI Passthrough Network Interface
-
Provisioning the Citrix ADC Virtual Appliance by using the virsh Program
-
Provisioning the Citrix ADC Virtual Appliance with SR-IOV, on OpenStack
-
Configuring a Citrix ADC VPX Instance on KVM to Use OVS DPDK-Based Host Interfaces
-
-
Deploy a Citrix ADC VPX instance on Microsoft Azure
-
Network architecture for Citrix ADC VPX instances on Microsoft Azure
-
Configure multiple IP addresses for a Citrix ADC VPX standalone instance
-
Configure a high-availability setup with multiple IP addresses and NICs
-
Configure a high-availability setup with multiple IP addresses and NICs by using PowerShell commands
-
Configure HA-INC nodes by using the Citrix high availability template with Azure ILB
-
Configure address pools (IIP) for a Citrix Gateway appliance
-
Configure multiple IP addresses for a Citrix ADC VPX instance in standalone mode by using PowerShell commands
-
-
Upgrade and downgrade a Citrix ADC appliance
-
Solutions for Telecom Service Providers
-
Load Balance Control-Plane Traffic that is based on Diameter, SIP, and SMPP Protocols
-
Provide Subscriber Load Distribution Using GSLB Across Core-Networks of a Telecom Service Provider
-
Authentication, authorization, and auditing application traffic
-
Configuring authentication, authorization, and auditing policies
-
Configuring Authentication, authorization, and auditing with commonly used protocols
-
Use an on-premises Citrix Gateway as the identity provider for Citrix Cloud™
-
Troubleshoot authentication issues in Citrix ADC and Citrix Gateway with aaad.debug module
-
-
-
-
-
-
Persistence and persistent connections
-
Advanced load balancing settings
-
Gradually stepping up the load on a new service with virtual server–level slow start
-
Protect applications on protected servers against traffic surges
-
Retrieve location details from user IP address using geolocation database
-
Use source IP address of the client when connecting to the server
-
Use client source IP address for backend communication in a v4-v6 load balancing configuration
-
Set a limit on number of requests per connection to the server
-
Configure automatic state transition based on percentage health of bound services
-
-
Use case 2: Configure rule based persistence based on a name-value pair in a TCP byte stream
-
Use case 3: Configure load balancing in direct server return mode
-
Use case 6: Configure load balancing in DSR mode for IPv6 networks by using the TOS field
-
Use case 7: Configure load balancing in DSR mode by using IP Over IP
-
Use case 10: Load balancing of intrusion detection system servers
-
Use case 11: Isolating network traffic using listen policies
-
Use case 12: Configure Citrix Virtual Desktops for load balancing
-
Use case 13: Configure Citrix Virtual Apps™ for load balancing
-
Use case 14: ShareFile wizard for load balancing Citrix ShareFile
-
-
-
-
-
Authentication and authorization
-
-
Configuring a CloudBridge Connector Tunnel between two Datacenters
-
Configuring CloudBridge Connector between Datacenter and AWS Cloud
-
Configuring a CloudBridge Connector Tunnel Between a Datacenter and Azure Cloud
-
Configuring CloudBridge Connector Tunnel between Datacenter and SoftLayer Enterprise Cloud
-
Configuring a CloudBridge Connector Tunnel Between a Citrix ADC Appliance and Cisco IOS Device
-
CloudBridge Connector Tunnel Diagnostics and Troubleshooting
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Configure multiple IP addresses for a Citrix® ADC VPX standalone instance by using PowerShell commands
In an Azure environment, a Citrix ADC VPX virtual appliance can be deployed with multiple NICs. Each NIC can have multiple IP addresses. This section describes how to deploy a Citrix ADC VPX instance with a single NIC and multiple IP addresses, by using PowerShell commands. You can use the same script for multi-NIC and multi-IP deployment.
Note
In this document, IP-Config refers to a pair of IP addresses, public IP and private IP, that is associated with an inidivual NIC. For more information, see the Azure terminology section.
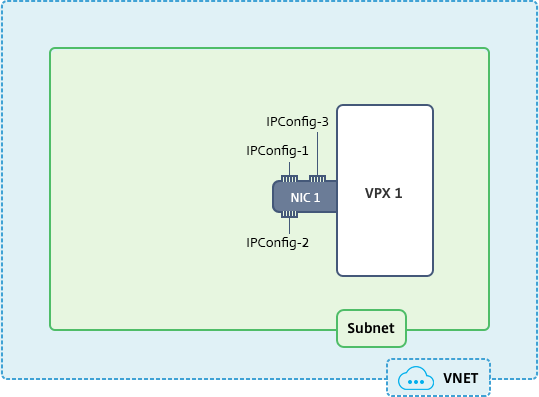
Use case
In this use case, a single NIC is connected to a virtual network (VNET). The NIC is associated with three IP configurations, as shown in the following table.
| IPConfig | Assocaited with |
|---|---|
| IPConfig-1 | Static public IP address; static private IP address |
| IPConfig-2 | Static public IP address; static private address |
| IPConfig-3 | Static private IP addres |
Note
IPConfig-3 is not associated with any public IP address.
Diagram: Topology
Here is the visual representation of the use case.
Note
In a multi-NIC, multi-IP Azure Citrix ADC VPX deployment, the private IP address associated with the primary (first) IPConfig of the primary (first) NIC is automatically added as the management NSIP address of the appliance. The remaining private IP addresses associated with IPConfigs must be added in the VPX instance as VIPs or SNIPs by using the “add ns ip” command, as determined by your requirements.
Here is the summary of the steps required for configuring multiple IP addresses for a Citrix ADC VPX virtual appliance in standalone mode:
- Create Resource Group
- Create Storage Account
- Create Availability Set
- Create NSG
- Create Virtual Network
- Create Public IP Address
- Assign IP Configuration
- Create NIC
- Create Citrix ADC VPX Instance
- Check NIC Configurations
- Check VPX-side Configurations
Script
Parameters
Following are sample parameters settings for the use case in this document. You can use different settings if you wish.
$locName=”westcentralus”
$rgName=”Azure-MultiIP”
$nicName1=”VM1-NIC1”
$vNetName=”Azure-MultiIP-vnet”
$vNetAddressRange=”11.6.0.0/16”
$frontEndSubnetName=”frontEndSubnet”
$frontEndSubnetRange=”11.6.1.0/24”
$prmStorageAccountName=”multiipstorage”
$avSetName=”multiip-avSet”
$vmSize=”Standard_DS4_V2” (This parameter creates a VM with upto four NICs.)
Note: The minimum requirement for a VPX instance is 2 vCPUs and 2GB RAM.
$publisher=”citrix”
$offer=”netscalervpx110-6531” (You can use different offers.)
$sku=”netscalerbyol” (According to your offer, the SKU can be different.)
$version=”latest”
$pubIPName1=”PIP1”
$pubIPName2=”PIP2”
$domName1=”multiipvpx1”
$domName2=”multiipvpx2”
$vmNamePrefix=”VPXMultiIP”
$osDiskSuffix=”osmultiipalbdiskdb1”
Network Security Group (NSG)-related information:
$nsgName=”NSG-MultiIP”
$rule1Name=”Inbound-HTTP”
$rule2Name=”Inbound-HTTPS”
$rule3Name=”Inbound-SSH”
$IpConfigName1=”IPConfig1”
$IPConfigName2=”IPConfig-2”
$IPConfigName3=”IPConfig-3”
1. Create Resource Group
New-AzureRmResourceGroup -Name $rgName -Location $locName
2. Create Storage Account
$prmStorageAccount = New-AzureRMStorageAccount -Name $prmStorageAccountName -ResourceGroupName $rgName -Type Standard_LRS -Location $locName
3. Create Availability Set
$avSet = New-AzureRMAvailabilitySet -Name $avSetName -ResourceGroupName $rgName -Location $locName
4. Create Network Security Group (NSG)
1. Add rules. You must add a rule to the NSG for any port that serves traffic.
$rule1=New-AzureRmNetworkSecurityRuleConfig -Name $rule1Name -Description "Allow HTTP" -Access Allow -Protocol Tcp -Direction Inbound -Priority 101 -SourceAddressPrefix Internet -SourcePortRange * -DestinationAddressPrefix * -DestinationPortRange 80
$rule2=New-AzureRmNetworkSecurityRuleConfig -Name $rule2Name -Description "Allow HTTPS" -Access Allow -Protocol Tcp -Direction Inbound -Priority 110 -SourceAddressPrefix Internet -SourcePortRange * -DestinationAddressPrefix * -DestinationPortRange 443
$rule3=New-AzureRmNetworkSecurityRuleConfig -Name $rule3Name -Description "Allow SSH" -Access Allow -Protocol Tcp -Direction Inbound -Priority 120 -SourceAddressPrefix Internet -SourcePortRange * -DestinationAddressPrefix * -DestinationPortRange 22
2. Create NSG object.
$nsg=New-AzureRmNetworkSecurityGroup -ResourceGroupName $rgName -Location $locName -Name $nsgName -SecurityRules $rule1,$rule2,$rule3
5. Create Virtual Network
1. Add subnets.
$frontendSubnet=New-AzureRmVirtualNetworkSubnetConfig -Name $frontEndSubnetName -AddressPrefix $frontEndSubnetRange
2. Add virtual network object.
$vnet=New-AzureRmVirtualNetwork -Name $vNetName -ResourceGroupName $rgName -Location $locName -AddressPrefix $vNetAddressRange -Subnet $frontendSubnet
3. Retrieve subnets.
$subnetName="frontEndSubnet"
\$subnet1=\$vnet.Subnets|?{\$\_.Name -eq \$subnetName}
6. Create Public IP Address
$pip1=New-AzureRmPublicIpAddress -Name $pubIPName1 -ResourceGroupName $rgName -DomainNameLabel $domName1 -Location $locName -AllocationMethod Static
$pip2=New-AzureRmPublicIpAddress -Name $pubIPName2 -ResourceGroupName $rgName -DomainNameLabel $domName2 -Location $locName -AllocationMethod Static
Note
Check availability of domain names before using.
Allocation method for IP addresses can be dynamic or static.
7. Assign IP Configuration
In this use case, consider the following points before assigning IP addresses:
- IPConfig-1 belongs to subnet1 of VPX1.
- IPConfig-2 belongs to subnet 1 of VPX1.
- IPConfig-3 belongs to subnet 1 of VPX1.
Note
When you assign multiple IP configurations to a NIC, one configuration must be assigned as primary.
$IPAddress1="11.6.1.27"
$IPConfig1=New-AzureRmNetworkInterfaceIpConfig -Name $IPConfigName1 -Subnet $subnet1 -PrivateIpAddress $IPAddress1 -PublicIpAddress $pip1 –Primary
$IPAddress2="11.6.1.28"
$IPConfig2=New-AzureRmNetworkInterfaceIpConfig -Name $IPConfigName2 -Subnet $subnet1 -PrivateIpAddress $IPAddress2 -PublicIpAddress $pip2
$IPAddress3="11.6.1.29"
$IPConfig3=New-AzureRmNetworkInterfaceIpConfig -Name $IPConfigName3 -Subnet $subnet1 -PrivateIpAddress $IPAddress3 -Primary
Use a valid IP address that meets your subnet requirements and check its availability.
8. Create NIC
$nic1=New-AzureRmNetworkInterface -Name $nicName1 -ResourceGroupName $rgName -Location $locName -IpConfiguration $IpConfig1,$IpConfig2,$IPConfig3 -NetworkSecurityGroupId $nsg.Id
9. Create Citrix ADC VPX Instance
1. Initialize variables.
$suffixNumber = 1
$vmName = $vmNamePrefix + $suffixNumber
2. Create VM config object.
$vmConfig=New-AzureRMVMConfig -VMName $vmName -VMSize $vmSize -AvailabilitySetId $avSet.Id
3. Set credentials, OS, and image.
$cred=Get-Credential -Message "Type the name and password for VPX login."
$vmConfig=Set-AzureRMVMOperatingSystem -VM $vmConfig -Linux -ComputerName $vmName -Credential $cred
$vmConfig=Set-AzureRMVMSourceImage -VM $vmConfig -PublisherName $publisher -Offer $offer -Skus $sku -Version $version
4. Add NIC.
$vmConfig=Add-AzureRMVMNetworkInterface -VM $vmConfig -Id $nic1.Id -Primary
Note
In a multi-NIC VPX deployment, one NIC should be primary. So, “-Primary” needs to be appended while adding that NIC to the VPX instance.
5. Specify OS disk and create VM.
$osDiskName=$vmName + "-" + $osDiskSuffix1
$osVhdUri=$prmStorageAccount.PrimaryEndpoints.Blob.ToString() + "vhds/" + $osDiskName + ".vhd"
$vmConfig=Set-AzureRMVMOSDisk -VM $vmConfig -Name $osDiskName -VhdUri $osVhdUri -CreateOption fromImage
Set-AzureRmVMPlan -VM $vmConfig -Publisher $publisher -Product $offer -Name $sku
New-AzureRMVM -VM $vmConfig -ResourceGroupName $rgName -Location $locName
10. Check NIC Configurations
After the VPX instance starts, you can check the IP addresses allocated to IPConfigs of the VPX NIC by using the following command.
$nic.IPConfig
11. Check VPX-side Configurations
When the Citrix ADC VPX instance starts, a private IP address associated with primary IPconfig of the primary NIC is added as the NSIP address. The remaining private IP addresses must be added as VIP or SNIP addresses, as determined by your requirements. Use the following command.
add nsip <Private IPAddress><netmask> -type VIP/SNIP
You’ve now configured multiple IP addresses for a Citrix ADC VPX instance in standalone mode.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.