Citrix SD-WAN™ Standard Edition Virtual Appliance (VPX) high availability Support for AWS
The following procedure describes how to deploy SD-WAN virtual (VPX) appliances in high-availability mode on the AWS cloud.
Points to consider when deploying SD-WAN VPX high availability appliances in the AWS Cloud.
- AWS does not support GARP (Generic Attribute Registration Protocol), VLAN or L2 related functionality, such as promiscuous mode and bridging. This is because two VMs belonging to different customers can be scheduled on the same host sharing NICs.
- L2 requires the switch appliance to be configured and these are not exposed to AWS users.
- SD-WAN appliance high availability model depends on GARP. When failover occurs, the new primary appliance sends GARPS out for VIP addresses.
- AWS takes a new approach for high availability failover. A new concept of ENI (Elastic Network Interface) is introduced. ENI is an entity which stands for Network Interface which has attributes like the IP address, MAC address, Security Group, and Port Rules.
- You can move ENIs from active or inactive Instance to another active or inactive Instance.
- The Instance must be capable to handling the hot plug of interfaces.
- Each Instance type has limitations on the number of ENIs associated and number of IPs per ENI.
- AWS design for high availability failover involves Instances communicating with the external server to call Query API AWS servers.
- The AWS servers are traditional HTTP servers. A request is sent from an instance to the Query API server to get or post information regarding an Instance/subnet/VPC or any other attribute on the AWS.
- For the cloud platform setup, the shared base MAC address configuration is ignored and has no significance.
Deploy Citrix SD-WAN standard edition VPX in high availability mode using cloud template
For more information,refer to the EBS best practices and Must-know best practices for Amazon EBS encryption
-
For defining Security groups the policy must look like the following:
- Outbound: Allow All traffic
- Inbound:
- SSH from all IP addresses / subnets from where management IP will be accessed.
- All traffic from your AWS VPCs (private IPs)
- All traffic from the WAN side public IPs of Citrix SD-WAN peer appliances hosted on prem or in cloud. From 11.3 release onwards, Citrix SD-WAN has introduced support for the M5 and C5 instances. The newer AWS regions such as Hong Kong and Paris only support M5 and C5 instances.
The M5 and C5 instances have improved hardware performance and are designed for higher demanding workloads. The M5 and C5 instances deliver better price/performance than the M4 instances on a per-core basis.
NOTE
The M5 and C5 instances are supported from a fresh provision of 11.3 and higher version only. To keep using the M5 and C5 instances, you cannot downgrade from 11.3 version since the M5 and C5 instances are not supported on any firmware version prior to 11.3 release.
Instances provisioned with 10.2.4/11.2.1 versions, AMIs cannot change their instance type to M5/C5.
Deploy SD-WAN standard edition VPX in high availability mode using cloud template
SD-WAN high availability solution template is published in the AWS marketplace, you can subscribe and use the CloudFormation template to deploy the HA setup.
Prerequisites
Before launching the CloudFormation template, you need to have VPC, subnets, route tables created for Management, LAN, and WAN network. To create and define the subnets and route tables (if not created), refer Installing SD-WAN VPX Standard Edition AMI on AWS topic.
To deploy SD-WAN standard edition VPX in high availability mode using cloud template:
-
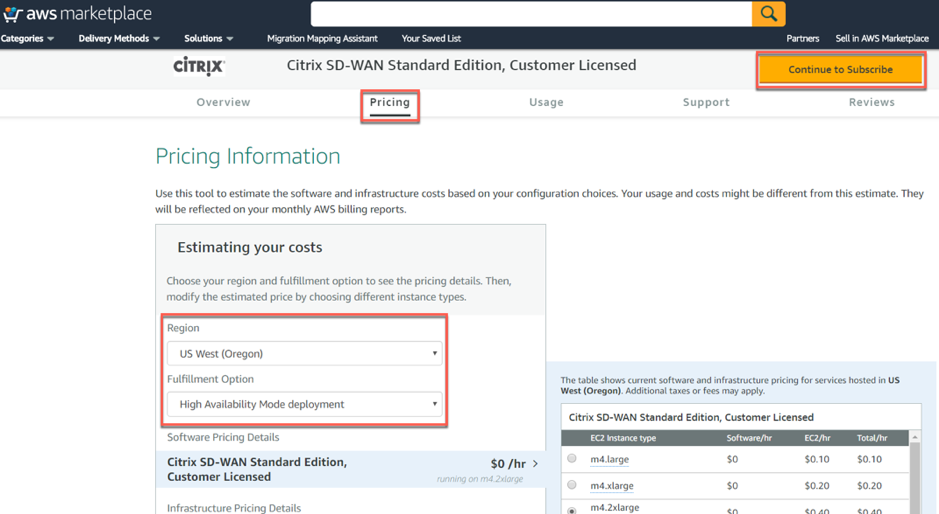
Go to AWS marketplace and click Pricing tab. Select the Region from the drop-down list and specify the Fulfillment Option as High Availability Mode deployment. Click Continue to Subscribe.
-
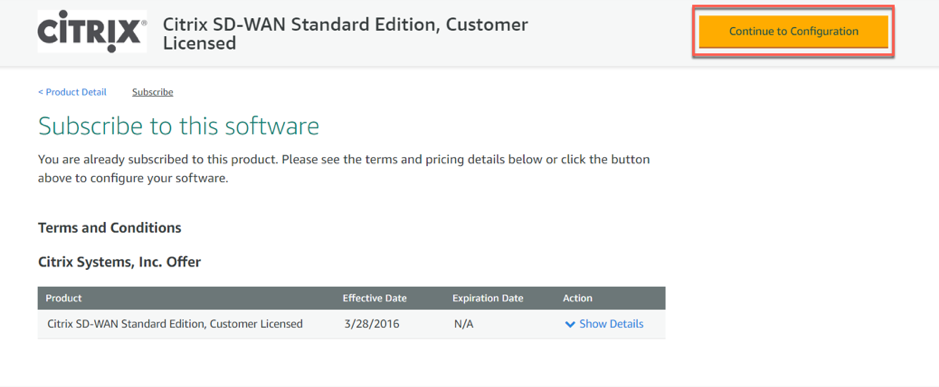
Click Continue to Configuration.
-
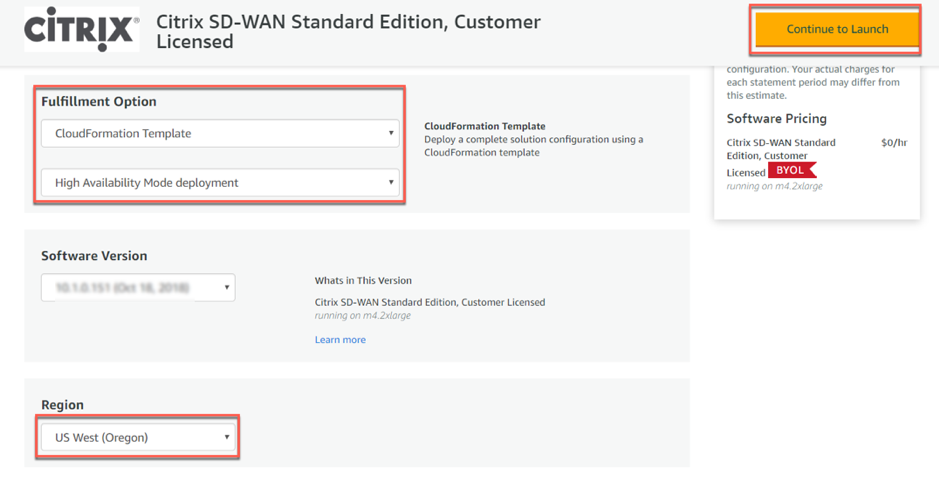
Specify Fulfillment Option as CloudFormation Template and High Availability Mode Deployment from the drop-down list. Select Region and click Continue to Launch.
-
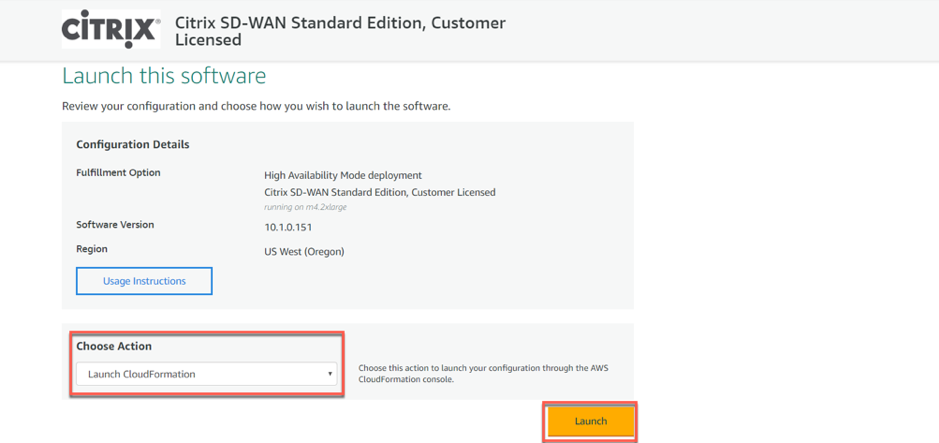
Choose action as Launch CloudFormation in the launch software window and click Launch.
-
In the Create Stack window, the predefined S3 template URL appears during the CloudFormation. Click Next.
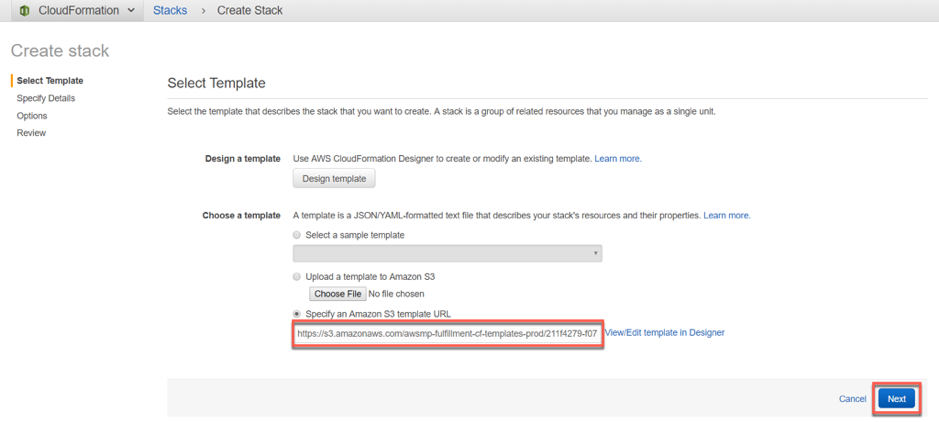
-
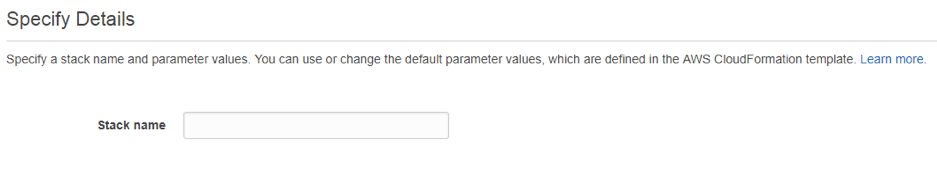
Specify a Stack name in the Specify Details section.
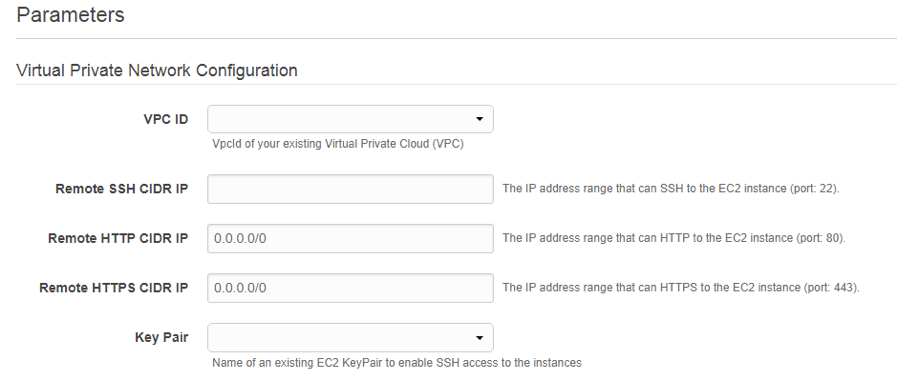
- Configure Virtual Private Network Configuration. Fill in the following parameter details:
- VPC ID: Provide the virtual private cloud ID.
-
Remote SSH CIDR IP: Provide the IP address range that can SSH to the EC2 instance (port 22).
Note It is recommended to allow SSH only from the known IP addresses.
- Remote HTTP CIDR IP: Provide the IP address range that can HTTP to the EC2 instance (port80).
- Remote HTTPS CIDR IP: Provide the IP address range that can HTTPS to the EC2 instance (port 443).
- Key Pair: Provide a name of an existing EC2 KeyPair to enable SSH access to the instances.
-
Configure Network Interfaces which must be attached to the instances created. Note that the Primary IPs are for the primary instance of the high availability pair and Secondary IPs are configured for the secondary instance of the high availability pair.
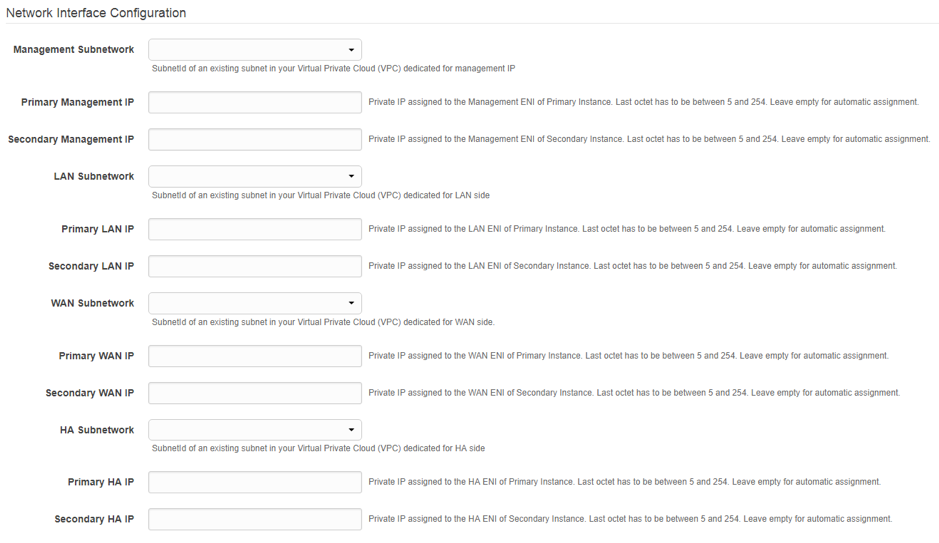
-
Configure other Parameters such as Instant Type and Tenancy Type and click Next.
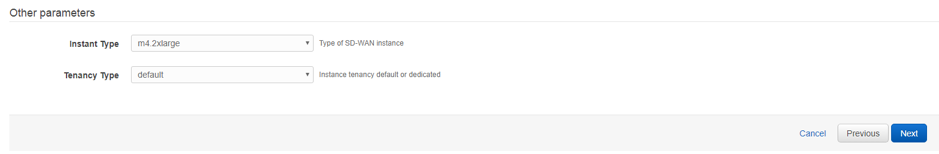
NOTE
If any validations fail, AWS notifies you and would not let you proceed until the errors are resolved.
-
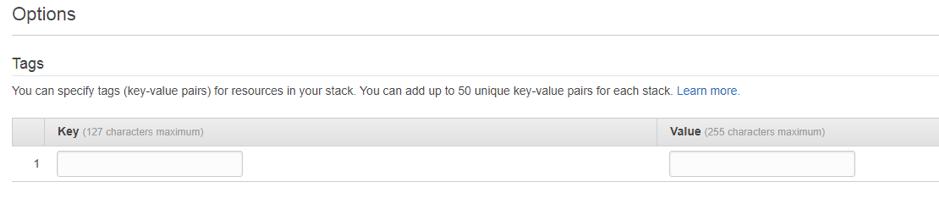
Set Tags. These tags are AWS-specific options which are user configurable.
-
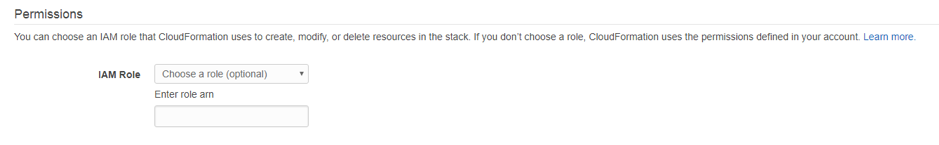
Configuring the IAM role is not recommended. This is already created by the customized IAM role, which is done through the Cloud Formation template.
-
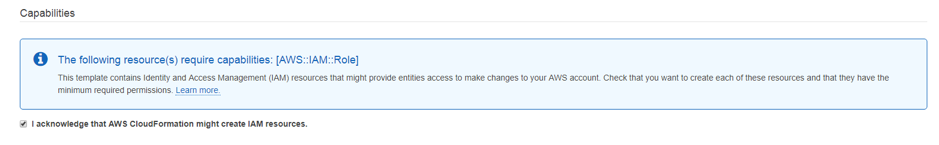
After clicking next, Review the template and acknowledge the custom IAM role which has been created by Cloud Formation template. Proceed with Create.
-
The new stack that you created appears on the Cloud Formation Stacks page. After successful template upload, Monitor the status of the template.
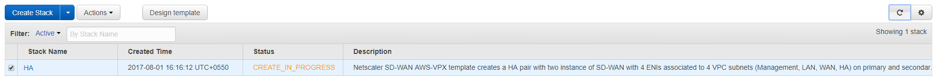
-
Monitor the events of all the resources created by the Cloud Formation template. If there is any failure, detailed descriptions of events are generated by AWS which helps in debugging the issue. The Events appear as follows:
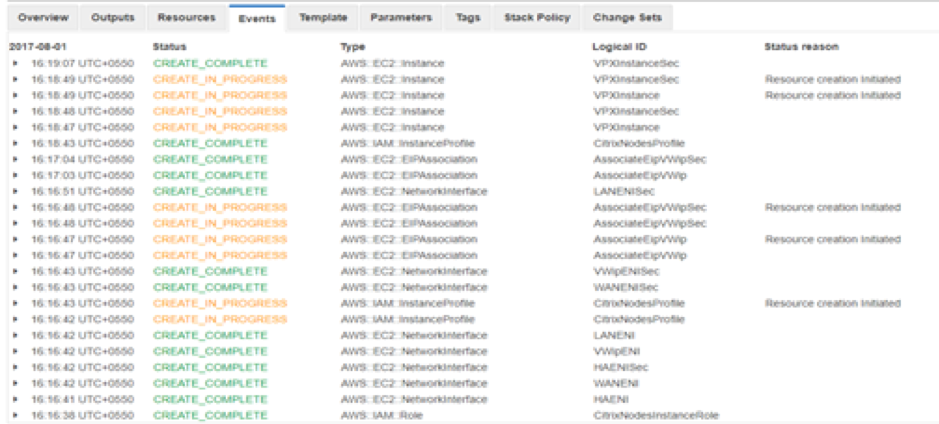
-
After successful stack creation, the status of the template appears as Create_Complete.
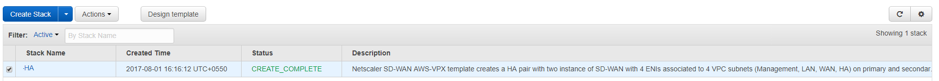
-
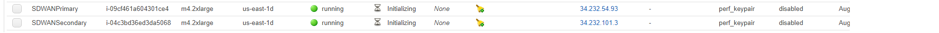
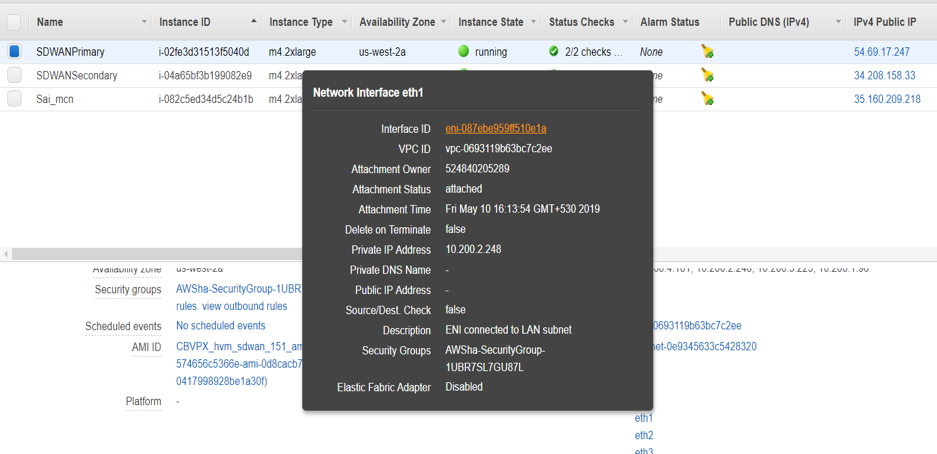
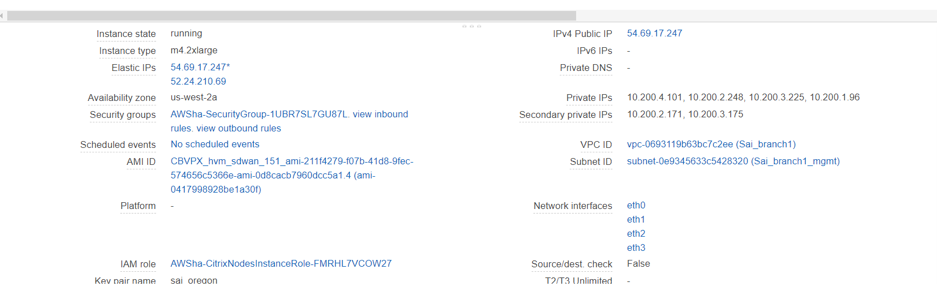
Navigate from AWS console to Services > EC2 > Instances. You can see two instances SDWANPrimary and SDWANSecondary instances created, up and running with Elastic IPs associated with the instances.
-
Select SDWANPrimary instance. You can notice all the resources rightly assigned to the instance, Security groups, Elastic IP, IAM role, and four Network Interfaces. Failed to create any high availability functionality might not work as expected.
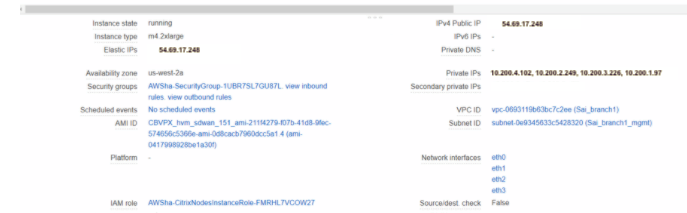
- Similarly select SDWANSecondary instance and verify the above resources.
Secondary floating IPs for LAN and WAN links
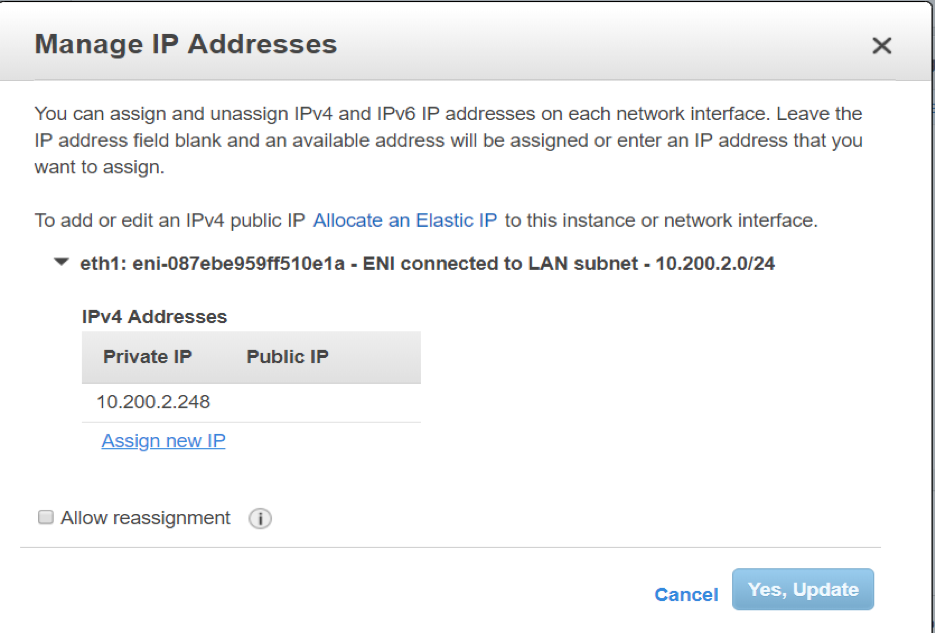
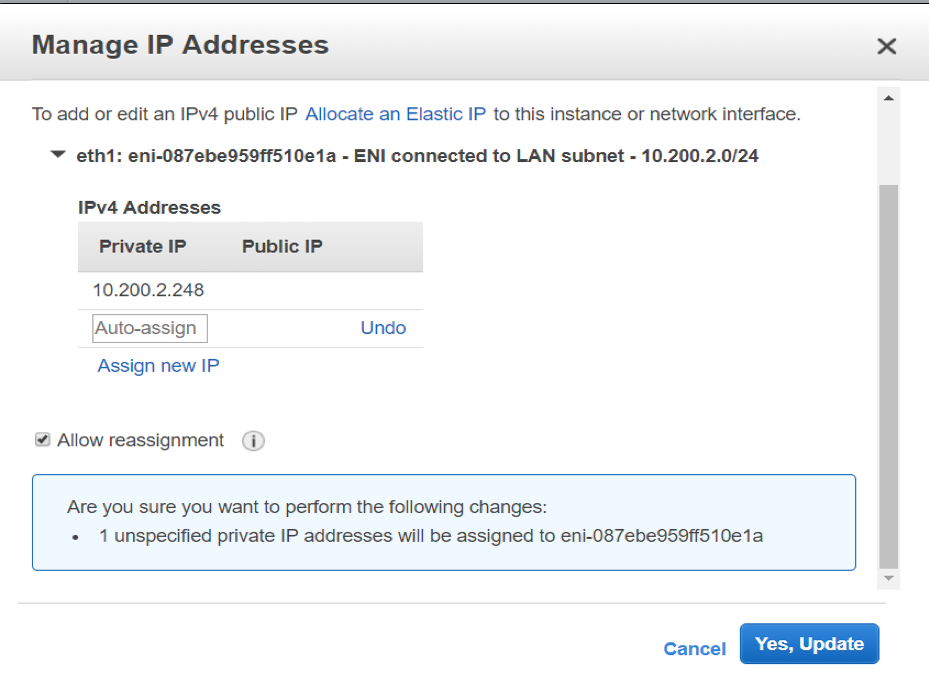
You need a secondary floating IPs for LAN and WAN links for the high availability to work. Once the stack is created, assign new secondary private IPs to the LAN and WAN interfaces of the active EC2 instance. These secondary configured IPs are used while configuring virtual IP addresses in VPX.
Perform the following procedure to attach the secondary LAN IPs to the active instance:
Note
Once the HA solution is deployed, we have to assign secondary floating IP only to the primary instance.
-
Navigate to Services > EC2 > Instances.
-
Navigate to Services > EC2 > Network interfaces and select the LAN/WAN Elastic Network Interfaces (ENI) of the primary instance.
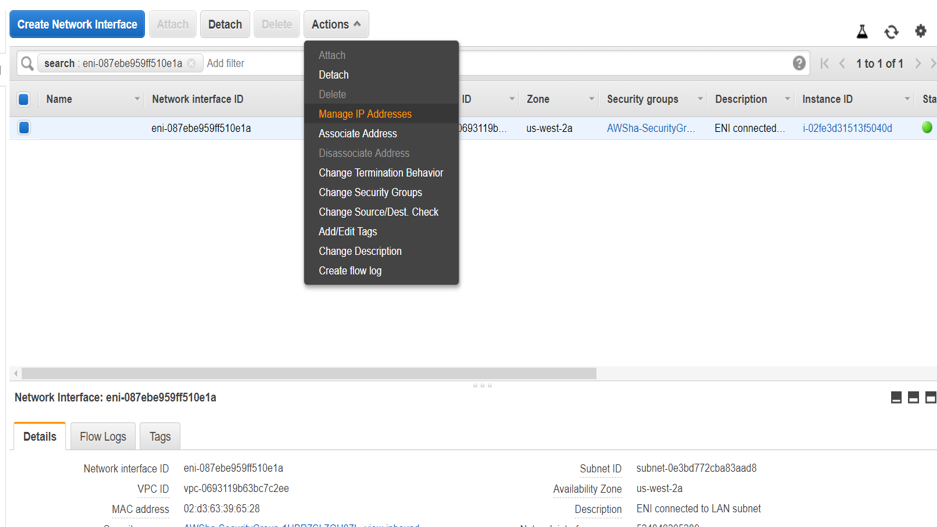
-
Assign new secondary IP.
-
Click Yes, Update.
-
Similarly create secondary private IP for the WAN interface as well.
Public IP on WAN link
A public IP required on the WAN link to communicate with the external world. Perform the following steps to associate elastic IP to the WAN ENI interface:
-
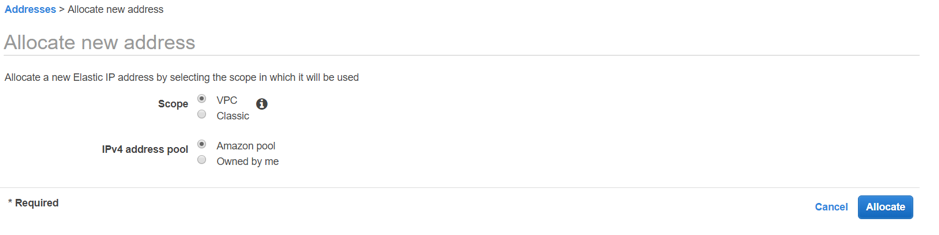
Navigate to Addresses > Allocate new address.
-
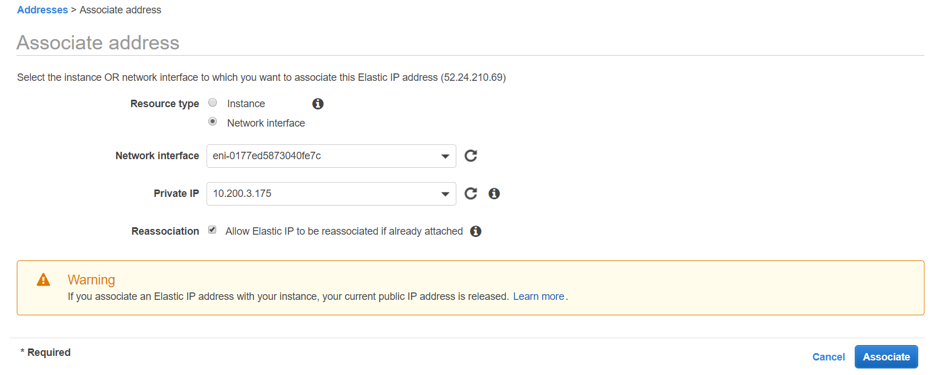
Select the elastic IP created, and click Action > Associate address and associate the public to the secondary private WAN IP which we just created.
-
Verify final interfaces and IPs are expected as below:
- Primary Instance:
- Secondary Instance:
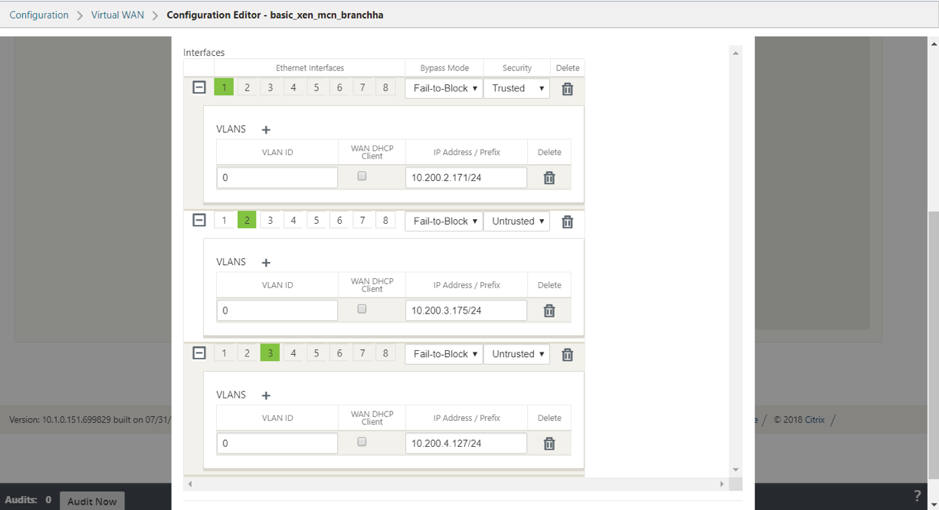
Now the instance provisioning is completed. Configuring SD-WAN high availability appliance is almost similar to configuring standalone appliance. Differences are listed below:
-
While creating LAN and WAN Virtual IP interfaces, specify the secondary private IPs created. And for the high availability virtual IP interface, specify a dummy IP in the high availability network.
-
Enable high availability and specify the high availability interface IPs of the active and secondary instance.
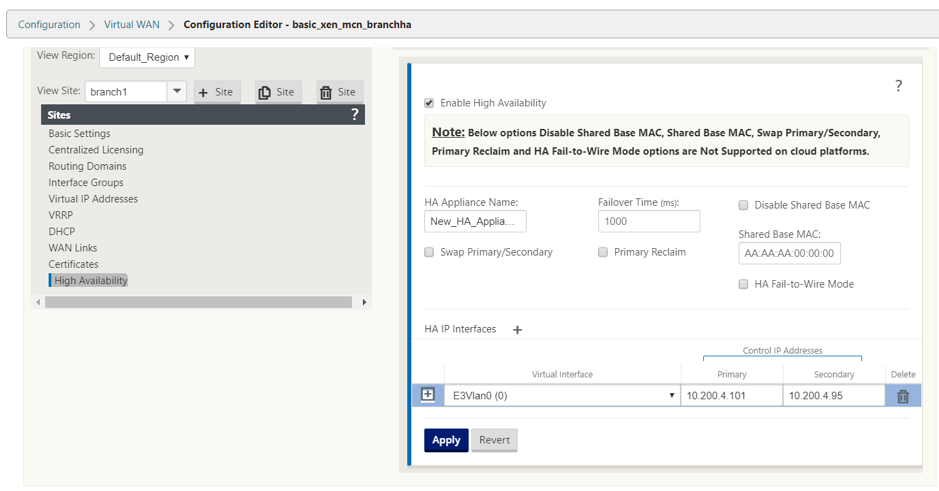
You can verify the high availability status.
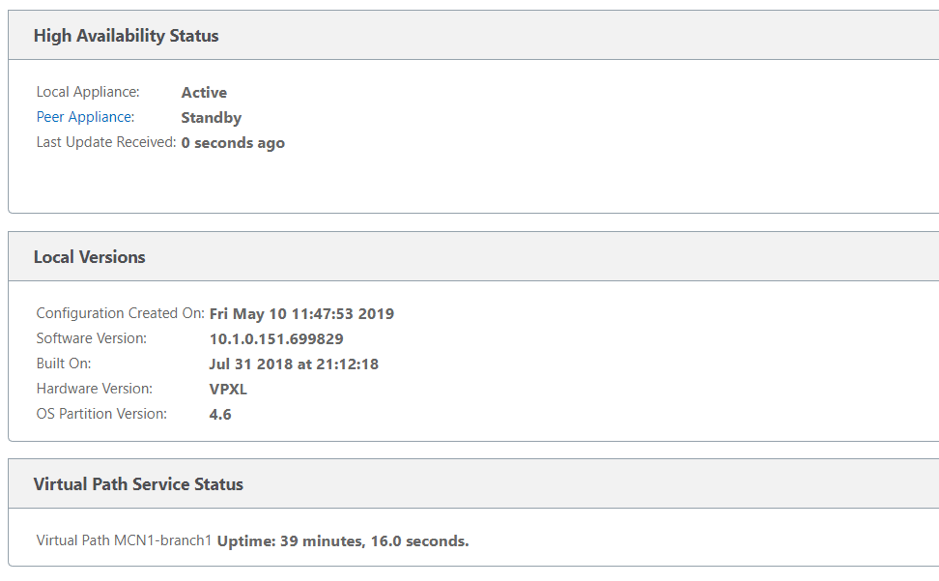
- Primary Instance:
How to configure high availability Fail-Over for any SD-WAN instance running on AWS
Set up high availability peers with one high availability peer with three or more ENIs, and 1 high availability peer with an equal number of ENIs. In both Peers, the first ENI is dedicated to Management. One high availability peer owns all Traffic ENIs. During a Failover, the traffic ENIs move from the failing instance to the new Primary instance.
For example, it can take up to or more than 20 secs to move two traffic ENIs. AWS do not have SLAs on API response and you cannot have one for high availability fail-over time.
Note
The AWS design has a limitation of instances dependent on the AWS servers to respond for attach and detach. The fail-over time is unpredictable.
Configuration steps
- Acquire information about your high availability Peer Instance about information on the number of ENIs associated and details of ENIs associated using the REST API.
- Detect the condition of the failing instance.
- Call Detach of ENIs from failing instance using REST APIs.
- Ensure all ENIs associated are detached.
- Attach ENIs to the current Primary instance.
- Ensure All ENIs are attached.
- Trigger upper layers to detect that new ENIs are in place.
How to configure SD-WAN VPX-SE in a single AWS Virtual Private Cloud (VPC) Subnet or between regions with Public WAN link IP address
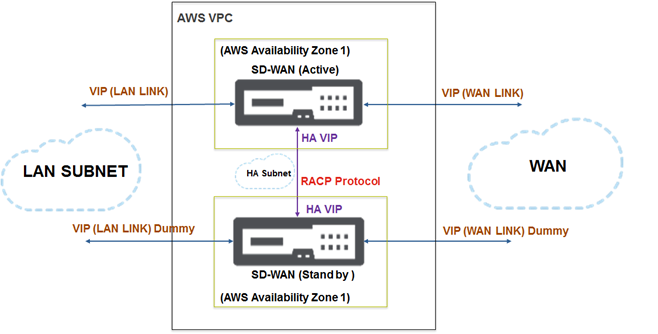
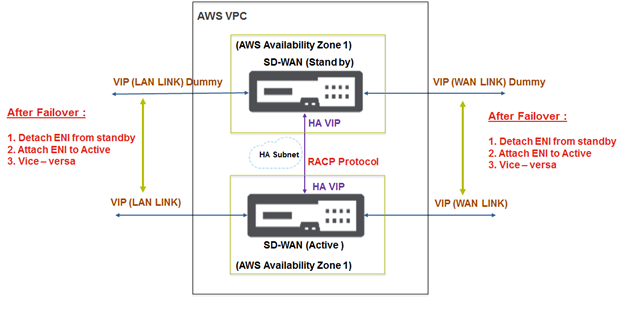
In AWS VPC, for an active SD-WAN instance, another high available SD-WAN instance running in the same VPC is released.
- The links configured are the same between active and stand-by SD-WAN appliances.
- For AWS, you can create a subnet and a dedicated link for the RACP protocol to communicate between the SD-WAN appliances.
- In the SD-WAN GUI, configure the following:
- Create an interface group. Name it as high availability-LINK. Add the interface used for high availability.
- Create a Virtual IP address for the Interface group.
- In High Availability Node, Enable high availability and add control Virtual IPs which the RACP protocol uses for communication. Ensure that the IP addresses are same as the configured IP addressed while creating network interfaces in AWS.
- Perform Change Management and download the active configuration for the stand-by SD-WAN appliance.
- After applying configuration through local change management on the stand-by SD-WAN appliance, you will see heartbeats exchanged between active and stand-by SD-WAN high availability appliances.
- When failover occurs, you see SD-WAN appliance transitioning from stand-by to active modes and/or conversely without any configuration loss.
Note
AWS supports high availability mode with features such as Elastic Load balancing and auto-scaling where the challenge is to sync configuration within the SD-WAN appliances. In this deployment, you apply the existing RACP protocol for efficient high availability.
Both MCN and branch site appliances can be made available in the cloud environment.
In this article
- Deploy Citrix SD-WAN standard edition VPX in high availability mode using cloud template
- Deploy SD-WAN standard edition VPX in high availability mode using cloud template
- Secondary floating IPs for LAN and WAN links
- Public IP on WAN link
- How to configure high availability Fail-Over for any SD-WAN instance running on AWS
- How to configure SD-WAN VPX-SE in a single AWS Virtual Private Cloud (VPC) Subnet or between regions with Public WAN link IP address