-
-
-
-
Scenarios for Flexed or Pooled license expiry and connectivity issues behavior
-
Configure NetScaler Console as the Flexed or Pooled license server
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Enable data collection for NetScaler Gateway appliances deployed in double-hop mode
The NetScaler Gateway double-hop mode provides extra protection to an organization’s internal network, because an attacker would need to penetrate multiple security zones or Demilitarized zones (DMZ) to reach the servers in the secure network. If you want to analyze the number of hops (NetScaler Gateway appliances) through which the ICA connections pass, and also the details about the latency on each TCP connection and how it fairs against the total ICA latency perceived by the client, you must install NetScaler Console, so that the NetScaler Gateway appliances report these vital statistics.
Figure 3. NetScaler Console deployed in double-hop mode
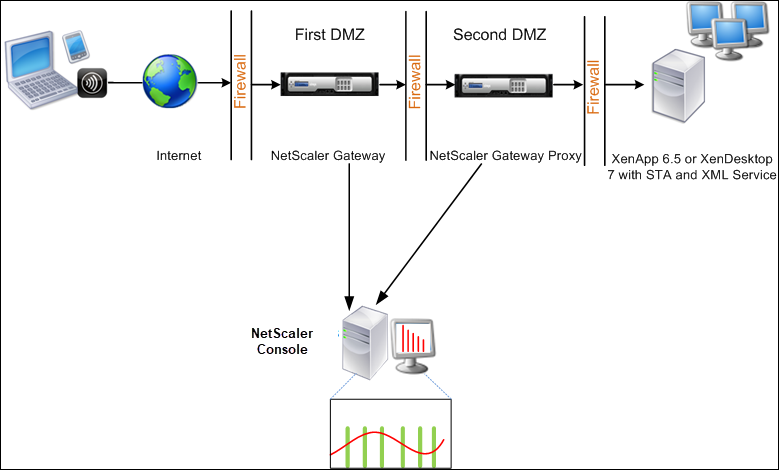
The NetScaler Gateway in the first DMZ handles user connections and performs the security functions of an SSL VPN. This NetScaler Gateway encrypts user connections, determines how the users are authenticated, and controls access to the servers in the internal network.
The NetScaler Gateway in the second DMZ serves as a NetScaler Gateway proxy device. This NetScaler Gateway enables the ICA traffic to traverse the second DMZ to complete user connections to the server farm.
The NetScaler Console can be deployed either in the subnet belonging to the NetScaler Gateway appliance in the first DMZ or the subnet belonging to the NetScaler Gateway appliance second DMZ. In the above image, the NetScaler Console and NetScaler Gateway in the first DMZ are deployed in the same subnet.
In a double-hop mode, NetScaler Console collects TCP records from one appliance and ICA records from the other appliance. After you add the NetScaler Gateway appliances to the NetScaler Console inventory and enable data collection, each appliance exports the reports by keeping track of the hop count and connection chain ID.
For NetScaler Console to identify which appliance is exporting records, each appliance is specified with a hop count and each connection is specified with a connection chain ID. Hop count represents the number of NetScaler Gateway appliances through which the traffic flows from a client to the servers. The connection chain ID represents the end- to end connections between the client and server.
NetScaler Console uses the hop count and connection chain ID to co-relate the data from both the NetScaler Gateway appliances and generates the reports.
To monitor NetScaler Gateway appliances deployed in this mode, you must first add the NetScaler Gateway to NetScaler Console inventory, enable AppFlow on NetScaler Console, and then view the reports on the NetScaler Console dashboard.
Enable data collection on NetScaler Console
If you enable NetScaler Console to start collecting the ICA details from both the appliances, the details collected are redundant. That is both the appliances report the same metrics. To overcome this situation, you must enable AppFlow for TCP on one of the first NetScaler Gateway appliances, and then enable AppFlow for ICA on the second appliance. By doing so, one of the appliances exports ICA AppFlow records and the other appliance exports TCP AppFlow records. This also saves the processing time on parsing the ICA traffic.
To enable the AppFlow feature from NetScaler Console:
-
Navigate to Infrastructure > Instances, and select the NetScaler instance you want to enable analytics.
-
From the Action list, select Enable/Disable Insight.
-
Select the VPN virtual servers, and click Enable AppFlow®.
-
In the Enable AppFlow field, type true, and select ICA/TCP for ICA traffic a TCP traffic respectively.
Note
If AppFlow logging is not enabled for the services or service groups on the NetScaler appliance, the NetScaler Console dashboard does not display the records, even if the Insight column shows Enabled.
-
Click OK.
Configure NetScaler Gateway appliances to export data
After you install the NetScaler Gateway appliances, you must configure the following settings on the NetScaler Gateway appliances to export the reports to NetScaler Console:
-
Configure virtual servers of the NetScaler Gateway appliances in the first and second DMZ to communicate with each other.
-
Bind the NetScaler Gateway virtual server in the second DMZ to the NetScaler Gateway virtual server in the first DMZ.
-
Enable double hop on the NetScaler Gateway in the second DMZ.
-
Disable authentication on the NetScaler Gateway virtual server in the second DMZ.
-
Enable one of the NetScaler Gateway appliances to export ICA records
-
Enable the other NetScaler Gateway appliance to export TCP records:
-
Enable connection chaining on both the NetScaler Gateway appliances.
Configure NetScaler Gateway using the command line interface:
-
Configure the NetScaler Gateway virtual server in the first DMZ to communicate with the NetScaler Gateway virtual server in the second DMZ.
add vpn nextHopServer [**-secure**(ON OFF)] [-imgGifToPng] … add vpn nextHopServer nh1 10.102.2.33 8443 –secure ON <!--NeedCopy--> -
Bind the NetScaler Gateway virtual server in the second DMZ to the NetScaler Gateway virtual server in the first DMZ. Run the following command on the NetScaler Gateway in the first DMZ:
bind vpn vserver <name> -nextHopServer <name>
bind vpn vserver vs1 -nextHopServer nh1 <!--NeedCopy--> -
Enable double hop and AppFlow on the NetScaler Gateway in the second DMZ.
set vpn vserver [**- doubleHop** ( ENABLED DISABLED )] [- appflowLog ( ENABLED DISABLED )] set vpn vserver vpnhop2 –doubleHop ENABLED –appFlowLog ENABLED <!--NeedCopy--> -
Disable authentication on the NetScaler Gateway virtual server in the second DMZ.
set vpn vserver [**-authentication** (ON OFF)] set vpn vserver vs -authentication OFF <!--NeedCopy--> -
Enable one of the NetScaler Gateway appliances to export TCP records.
bind vpn vserver<name> [-policy<string> -priority<positive_integer>] [-type<type>]
bind vpn vserver vpn1 -policy appflowpol1 -priority 101 –type OTHERTCP\_REQUEST <!--NeedCopy--> -
Enable the other NetScaler Gateway appliance to export ICA records:
bind vpn vserver<name> [-policy<string> -priority<positive_integer>] [-type<type>]
bind vpn vserver vpn2 -policy appflowpol1 -priority 101 -type ICA\_REQUEST <!--NeedCopy--> -
Enable connection chaining on both the NetScaler Gateway appliances:
set appFlow param [-connectionChaining (ENABLED DISABLED)] set appflow param -connectionChaining ENABLED <!--NeedCopy-->
Configuring NetScaler Gateway using configuration utility:
-
Configure the NetScaler Gateway in the first DMZ to communicate with the NetScaler Gateway in the second DMZ and bind the NetScaler Gateway in the second DMZ to the NetScaler Gateway in the first DMZ.
-
On the Configuration tab expand NetScaler Gateway and click Virtual Servers.
-
In the right pane, double-click the virtual server, and in the Advanced group, expand Published Applications.
-
Click Next Hop Server and bind a next hop server to the second NetScaler Gateway appliance.
-
-
Enable double hop on the NetScaler Gateway in the second DMZ.
-
On the Configuration tab expand NetScaler Gateway and click Virtual Servers.
-
In the right pane, double-click the virtual server, and in the Basic Settings group, click the edit icon.
-
Expand More , select Double Hop and click OK.
-
-
Disable authentication on the virtual server on the NetScaler Gateway in the second DMZ.
-
On the Configuration tab expand NetScaler Gateway and click Virtual Servers.
-
In the right pane, double-click the virtual server, and in the Basic Settings group, click the edit icon.
-
Expand More, and clear Enable Authentication.
-
-
Enable one of the NetScaler Gateway appliances to export TCP records.
-
On the Configuration tab expand NetScaler Gateway and click Virtual Servers.
-
In the right pane, double-click the virtual server, and in the Advanced group, expand Policies.
-
Click the + icon and from the Choose Policy list, select AppFlow, and from the Choose Type drop-down list, select Other TCP Request.
-
Click Continue.
-
Add a policy binding, and click Close.
-
-
Enable the other NetScaler Gateway appliance to export ICA records:
-
On the Configuration tab expand NetScaler Gateway and click Virtual Servers.
-
In the right pane, double-click the virtual server, and in the Advanced group, expand Policies.
-
Click the + icon and from the Choose Policy drop-down list, select AppFlow, and from theChoose Type drop-down list, select Other TCP Request.
-
Click Continue.
-
Add a policy binding, and click Close.
-
-
Enable connection chaining on both the NetScaler Gateway appliances.
-
On the Configuration tab, navigate to Settings > Appflow.
-
In the right Pane, in the Settings group, click Change Appflow Settings.
-
Select Connection Chaining and Click OK.
-
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.