-
Getting Started with NetScaler
-
Solutions for Telecom Service Providers
-
Load Balance Control-Plane Traffic that is based on Diameter, SIP, and SMPP Protocols
-
Provide Subscriber Load Distribution Using GSLB Across Core-Networks of a Telecom Service Provider
-
Authentication, authorization, and auditing application traffic
-
Basic components of authentication, authorization, and auditing configuration
-
-
Web proxy support for outbound calls to IDP or third party endpoints
-
Web Application Firewall protection for VPN virtual servers and authentication virtual servers
-
On-premises NetScaler Gateway as an identity provider to Citrix Cloud™
-
Authentication, authorization, and auditing configuration for commonly used protocols
-
Troubleshoot authentication and authorization related issues
-
-
-
-
-
-
Configure DNS resource records
-
Configure NetScaler as a non-validating security aware stub-resolver
-
Jumbo frames support for DNS to handle responses of large sizes
-
Caching of EDNS0 client subnet data when the NetScaler appliance is in proxy mode
-
Use case - configure the automatic DNSSEC key management feature
-
Use Case - configure the automatic DNSSEC key management on GSLB deployment
-
-
-
Source IP address whitelisting for GSLB communication channels
-
Use case: Deployment of domain name based autoscale service group
-
Use case: Deployment of IP address based autoscale service group
-
-
Persistence and persistent connections
-
Advanced load balancing settings
-
Gradually stepping up the load on a new service with virtual server–level slow start
-
Protect applications on protected servers against traffic surges
-
Retrieve location details from user IP address using geolocation database
-
Use source IP address of the client when connecting to the server
-
Use client source IP address for backend communication in a v4-v6 load balancing configuration
-
Set a limit on number of requests per connection to the server
-
Configure automatic state transition based on percentage health of bound services
-
-
Use case 2: Configure rule based persistence based on a name-value pair in a TCP byte stream
-
Use case 3: Configure load balancing in direct server return mode
-
Use case 6: Configure load balancing in DSR mode for IPv6 networks by using the TOS field
-
Use case 7: Configure load balancing in DSR mode by using IP Over IP
-
Use case 10: Load balancing of intrusion detection system servers
-
Use case 11: Isolating network traffic using listen policies
-
Use case 12: Configure Citrix Virtual Desktops for load balancing
-
Use case 13: Configure Citrix Virtual Apps and Desktops for load balancing
-
Use case 14: ShareFile wizard for load balancing Citrix ShareFile
-
Use case 15: Configure layer 4 load balancing on the NetScaler appliance
-
-
-
-
Authentication and authorization for System Users
-
-
-
Configuring a CloudBridge Connector Tunnel between two Datacenters
-
Configuring CloudBridge Connector between Datacenter and AWS Cloud
-
Configuring a CloudBridge Connector Tunnel Between a Datacenter and Azure Cloud
-
Configuring CloudBridge Connector Tunnel between Datacenter and SoftLayer Enterprise Cloud
-
Configuring a CloudBridge Connector Tunnel Between a NetScaler Appliance and Cisco IOS Device
-
CloudBridge Connector Tunnel Diagnostics and Troubleshooting
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Configuring CloudBridge® Connector between datacenter and AWS cloud
You can configure a CloudBridge Connector tunnel between a datacenter and AWS cloud to leverage the infrastructure and computing capabilities of the data center and the AWS cloud. With AWS, you can extend your network without initial capital investment or the cost of maintaining the extended network infrastructure. You can scale your infrastructure up or down, as required. For example, you can lease more server capabilities when the demand increases.
To connect a datacenter to AWS cloud, you set up a CloudBridge Connector tunnel between a NetScaler appliance that resides in the datacenter and a NetScaler virtual appliance (VPX) that resides in AWS cloud.
As an illustration of a CloudBridge Connector tunnel between a datacenter and Amazon AWS cloud, consider an example in which a CloudBridge Connector tunnel is set up between NetScaler appliance NS_Appliance-DC, in datacenter DC, and NetScaler virtual appliance (VPX) NS_VPX_Appliance-AWS.
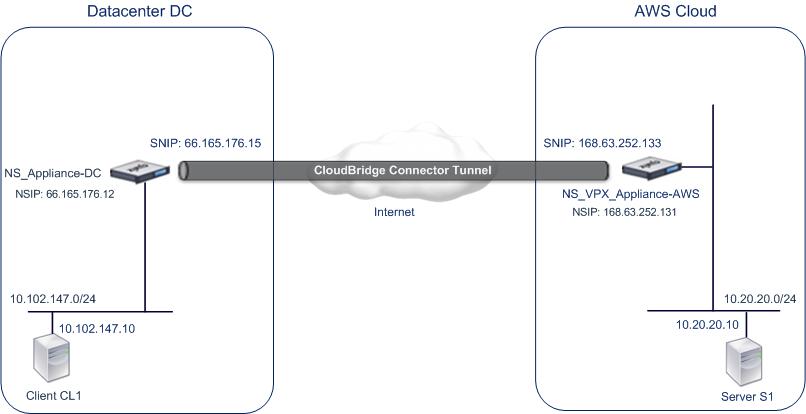
Both NS_Appliance-DC and NS_VPX_Appliance-AWS function in L3 mode. They enable communication between private networks in datacenter DC and the AWS cloud. NS_Appliance-DC and NS_VPX_Appliance-AWS enable communication between client CL1 in datacenter DC and server S1 in the AWS cloud through the CloudBridge Connector tunnel. Client CL1 and server S1 are on different private networks.
Note:
AWS does not support L2 mode, hence it is necessary to have only L3 mode enabled on both the endpoints.
For proper communication between CL1 and S1, L3 mode is enabled on NS_Appliance-DC and NS_VPX_Appliance-AWS and routes are updated as such:
- CL1 have a route to NS_Appliance-DC for reaching S1.
- NS_Appliance-DC have a route to NS_VPX_Appliance-AWS for reaching S1.
- S1 should have a route to NS_VPX_Appliance-AWS for reaching CL1.
- NS_VPX_Appliance-AWS have a route to NS_Appliance-DC for reaching CL1.
The following table lists the settings on NetScaler appliance NS_Appliance-DC in datacenter DC.
| Entity | Name | Details |
|---|---|---|
| The NSIP address | 66.165.176.12 | |
| SNIP address | 66.165.176.15 | |
| CloudBridge Connector tunnel | CC_Tunnel_DC-AWS | Local endpoint IP address of the CloudBridge Connector tunnel: 66.165.176.15, Remote endpoint IP address of the CloudBridge Connector tunnel: 168.63.252.133, GRE Tunnel Details - Name= CC_Tunnel_DC-AWS |
The following table lists the settings on NetScaler VPX NS_VPX_Appliance-AWS on AWS cloud.
| Entity | Name | Details |
|---|---|---|
| NSIP address | 10.102.25.30 | |
| Public EIP address mapped to the NSIP address | 168.63.252.131 | |
| SNIP address | 10.102.29.30 | |
| Public EIP address mapped to the SNIP address | 168.63.252.133 | |
| CloudBridge Connector tunnel | CC_Tunnel_DC-AWS | Local endpoint IP address of the CloudBridge Connector tunnel:168.63.252.133, Remote endpoint IP address of the CloudBridge Connector tunnel: 66.165.176.15; GRE Tunnel Details Name= CC_Tunnel_DC-AWS, IPSec Profile Details, Name= CC_Tunnel_DC-AWS, Encryption algorithm= AES, Hash algorithm= HMAC SHA1 |
Prerequisites
Before setting up a CloudBridge Connector tunnel, verify that the following tasks have been completed:
-
Install, configure, and launch an instance of NetScaler Virtual appliance (VPX) on AWS cloud. For instructions on installing NetScaler VPX on AWS, see Deploy a NetScaler VPX instance on AWS.
-
Deploy and configure a NetScaler physical appliance, or provisioning and configuring a NetScaler virtual appliance (VPX) on a virtualization platform in the datacenter.
-
Make sure that the CloudBridge Connector tunnel end-point IP addresses are accessible to each other.
NetScaler VPX license
After the initial instance launch, NetScaler VPX for AWS requires a license. If you are bringing your own license (BYOL), see the VPX Licensing Guide at: http://support.citrix.com/article/CTX122426.
You have to:
- Use the licensing portal within Citrix® website to generate a valid license.
- Upload the license to the instance.
If this is a paid marketplace instance, then you do not need to install a license. The correct feature set and performance will activate automatically.
Configuration steps
To set up a CloudBridge Connector tunnel between a NetScaler appliance that resides in a datacenter and a NetScaler virtual appliance (VPX) that resides on the AWS cloud, use the GUI of the NetScaler appliance.
When you use the GUI, the CloudBridge Connector tunnel configuration created on the NetScaler appliance, is automatically pushed to the other endpoint or peer (the NetScaler VPX on AWS) of the CloudBridge Connector tunnel. Therefore, you do not have to access the GUI (GUI) of the NetScaler VPX on AWS to create the corresponding CloudBridge Connector tunnel configuration on it.
The CloudBridge Connector tunnel configuration on both peers (the NetScaler appliance that resides in the datacenter and the NetScaler virtual appliance (VPX) that resides on the AWS cloud) consists of the following entities:
- IPSec profile—An IPSec profile entity specifies the IPSec protocol parameters, such as IKE version, encryption algorithm, hash algorithm, and PSK, to be used by the IPSec protocol in both the peers of the CloudBridge Connector tunnel.
- GRE tunnel—An IP tunnel specifies a local IP address (a public SNIP address configured on the local peer), remote IP address (a public SNIP address configured on the remote peer), protocol (GRE) used to set up the CloudBridge Connector tunnel, and an IPSec profile entity.
- Create a PBR rule and associate the IP tunnel with it—A PBR entity specifies a set of conditions and an IP tunnel entity. The source IP address range and the destination IP range are the conditions for the PBR entity. You must set the source IP address range and the destination IP address range to specify the subnet whose traffic is to traverse the CloudBridge Connector tunnel. For example, consider a request packet that originates from a client on the subnet in the datacenter and is destined to a server on the subnet in the AWS cloud. If this packet matches the source and destination IP address range of the PBR entity on the NetScaler appliance in the datacenter, it is sent across the CloudBridge Connector tunnel associated with the PBR entity.
To create an IPSEC profile by using the command line interface
At the command prompt, type:
add ipsec profile <name> [-**ikeVersion** ( V1 | V2 )] [-**encAlgo** ( AES | 3DES ) ...] [-**hashAlgo** <hashAlgo> ...] [-**lifetime** <positive_integer>] (-**psk** | (-**publickey** <string> -**privatekey** <string> -**peerPublicKey** <string>)) [-**livenessCheckInterval** <positive_integer>] [-**replayWindowSize** <positive_integer>] [-**ikeRetryInterval** <positive_integer>] [-**retransmissiontime** <positive_integer>]**show ipsec profile** <name>
To create an IP tunnel and bind the IPSEC profile to it by using the command line interface
At the command prompt, type:
add ipTunnel <name> <remote><remoteSubnetMask> <local> [-protocol <protocol>] [-ipsecProfileName <string>]show ipTunnel <name>
To create a PBR rule and bind the IPSEC tunnel to it by using the command line interface
At the command prompt, type:
add ns pbr <pbr_name> ALLOW -srcIP = <local_subnet_range> -destIP = <remote_subnet_range> -ipTunnel <tunnel_name>apply ns pbrsshow ns pbr <pbr_name>
Example
> add ipsec profile CC_Tunnel_DC-AWS -encAlgo AES -hashAlgo HMAC_SHA1
Done
> add ipTunnel CC_Tunnel_DC-AWS 168.63.252.133 255.255.255.0 66.165.176.15 –protocol GRE -ipsecProfileName CC_Tunnel_DC-AWS
Done
> add ns pbr PBR-DC-AWS ALLOW –srcIP 66.165.176.15 –destIP 168.63.252.133 ipTunnel CC_Tunnel_DC-AWS
Done
> apply ns pbrs
Done
<!--NeedCopy-->
To configure a CloudBridge Connector tunnel in a NetScaler appliance by using the GUI
-
Type the NSIP address of a NetScaler appliance in the address line of a web browser.
-
Log on to the GUI of the NetScaler appliance by using your account credentials for the appliance.
-
Navigate to System > CloudBridge Connector.
-
In the right pane, under Getting Started, click Create/Monitor CloudBridge.
-
The first time you configure a CloudBridge Connector tunnel on the appliance, a Welcome screen appears.
-
On the Welcome screen click Get Started.
Note:
If you already have a CloudBridge Connector tunnel configured on the NetScaler appliance, the Welcome screen does not appear, so you do not click Get Started.
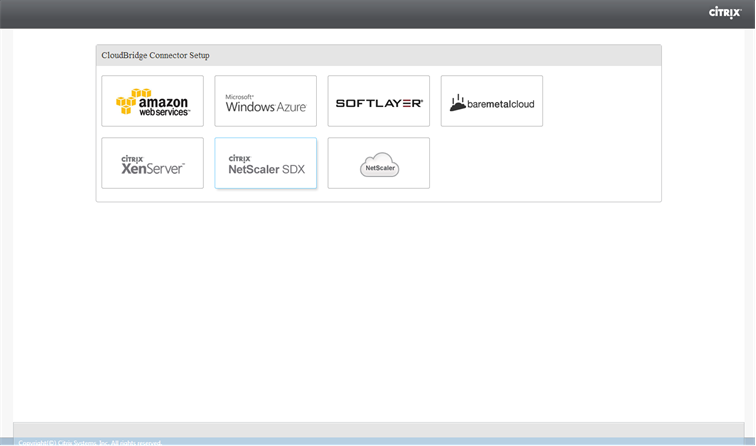
- In the CloudBridge Connector Setup pane, click amazon web services
- In the Amazon pane, provide your AWS account credentials: AWS Access Key ID and AWS Secret Access Key. You can obtain these access keys from the AWS GUI console. Click Continue.
Note
Earlier, the Setup wizard always connects to the same AWS region even when another region is selected. As a result, configuring CloudBridge Connector tunnel to a NetScaler VPX running on the selected AWS region used to fail. This issue has been fixed now.
-
In the NetScaler pane, select the NSIP address of the NetScaler virtual appliance running on AWS. Then, provide your account credentials for the NetScaler virtual appliance. Click Continue.
-
In the CloudBridge Connector Setting pane, set the following parameter:
- CloudBridge Connector Name—Name for the CloudBridge Connector configuration on the local appliance. Must begin with an ASCII alphabetic or underscore (_) character, and must contain only ASCII alphanumeric, underscore, hash (#), period (.), space, colon (:), at (@), equals (=), and hyphen (-) characters. Cannot be changed after the CloudBridge Connector configuration is created.
-
Under Local Setting, set the following parameter:
- Subnet IP—IP address of the local endpoint of the CloudBridge Connector tunnel. Must be a public IP address of type SNIP.
-
Under Remote Setting, set the following parameter:
-
Subnet IP—IP address of the CloudBridge Connector tunnel end point on the AWS side. Must be an IP address of type SNIP on the NetScaler VPX instance on AWS.
-
NAT—Public IP address (EIP) in AWS that is mapped to the SNIP configured on the NetScaler VPX instance on AWS.
-
-
Under PBR Setting, set the following parameters:
- Operation—Either the equals (=) or does not equal (!=) logical operator.
- Source IP Low—Lowest source IP address to match against the source IP address of an outgoing IPv4 packet.
- Source IP High—Highest source IP address to match against the source IP address of an outgoing IPv4 packet.
- Operation—Either the equals (=) or does not equal (!=) logical operator.
- Destination IP Low—Lowest destination IP address to match against the destination IP address of an outgoing IPv4 packet.
- Destination IP High—Highest destination IP address to match against the destination IP address of an outgoing IPv4 packet.
-
(Optional) Under Security Settings, set the following IPSec protocol parameters for the CloudBridge Connector tunnel:
- Encryption Algorithm—Encryption algorithm to be used by the IPSec protocol in the CloudBridge tunnel.
- Hash Algorithm—Hash algorithm to be used by the IPSec protocol in the CloudBridge tunnel.
-
Key— Select one of the following IPSec authentication methods to be used by the two peers to mutually authenticate.
- Auto Generate Key— Authentication based on a text string, called a pre-shared key (PSK), generated automatically by the local appliance. The PSKs keys of the peers are matched against each other for authentication.
-
Specific Key—Authentication based on a manually entered PSK. The PSKs of the peers are matched against each other for authentication.
- Pre Shared Security Key—The text string entered for pre-shared key based authentication.
-
Upload Certificates—Authentication based on digital certificates.
- Public Key—A local digital certificate to be used to authenticate the local peer to the remote peer before establishing IPSec security associations. The same certificate should be present and set for the Peer Public Key parameter in the peer.
- Private Key—Private key of the local digital certificate.
- Peer Public Key—Digital certificate of the peer. Used to authenticate the peer to the local end point before establishing IPSec security associations. The same certificate should be present and set for the Public key parameter in the peer.
-
Click Done.
The new CloudBridge Connector tunnel configuration on the NetScaler appliance in the datacenter appears on the Home tab of the GUI. The corresponding new CloudBridge Connector tunnel configuration on the NetScaler VPX appliance in the AWS cloud appears on the GUI. The current status of the CloudBridge connector tunnel is indicated in the Configured CloudBridge pane. A green dot indicates that the tunnel is up. A red dot indicates that the tunnel is down.
Monitoring the CloudBridge Connector tunnel
You can monitor the performance of CloudBridge Connector tunnels on a NetScaler appliance by using CloudBridge Connector tunnel statistical counters. For more information about displaying CloudBridge Connector tunnel statistics on a NetScaler appliance, see Monitoring CloudBridge Connector Tunnels.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.